As real-time payments grow globally, payment gateways and service providers (PSPs) face increasing pressure to outpace fraudsters. In 2024, scam-related fraud surged by 56%, now accounting for 23% of fraudulent transactions. With eCommerce fraud expected to rise from $44.3 billion in 2024 to $107 billion by 2029, businesses must adopt intelligent, adaptive strategies to balance security and user experience.
In this article, you’ll learn how to detect payment fraud across the entire customer journey. We’ll break down key techniques, such as digital footprint checks, AI, device intelligence and behavioral analytics, and explain how to build an adaptable fraud prevention approach that reduces false positives and scales as your business grows.
What Is Payment Fraud?
Payment fraud refers to unauthorized transactions made using stolen, fabricated or otherwise illegitimate payment credentials. It occurs when cybercriminals exploit security gaps to manipulate or hijack digital payments, often for financial gain.
For example, a fraudster might purchase stolen credit card details from the dark web and use them to buy high-value electronics online, leaving both the business and the cardholder to deal with the fallout. These attacks can involve various payment methods, including credit cards, virtual wallets, direct debits and mobile payments.
The damage goes beyond money. Victims often suffer from reduced credit scores, while businesses face chargebacks, financial losses and damaged customer trust. Fraudsters use tactics like phishing emails, malware infections and social engineering to access sensitive information.That’s why businesses need more than firewalls. Payment transaction monitoring, combined with encryption, tokenization and multi-factor authentication, is essential to detect suspicious activity before it leads to losses.
How Does Payment Fraud Affect Businesses?
Payment fraud has several negative effects on businesses:
- Financial impact: Companies face the financial burden of fraudulent transactions, including chargebacks and lost goods, which can significantly affect their profitability.
- Higher operational costs: Businesses must invest in advanced security systems, fraud detection technologies, and employee training to combat fraud, leading to higher operational expenses.
- Damage to reputation: Frequent fraud incidents can undermine customer trust, leading to a decline in customer loyalty and a potential long-term revenue loss.
- Operational challenges: Addressing and investigating fraud cases diverts resources and focus away from core business activities, disrupting daily operations and reducing overall efficiency.
- Regulatory risks: Non-compliance with security regulations can lead to substantial fines and legal consequences, further straining a business’s finances and operations.
Types of Payment Fraud
- Card testing: This is when fraudsters use stolen credit card information to make small online transactions to verify if the card details are valid and active. Once a card is confirmed as functional, fraudsters use it for more significant fraudulent transactions or sell it as validated information to other criminals. This form of fraud results in unauthorized charges to the cardholder and chargebacks and processing fees for the business.
- Credit card fraud: From the physical theft of card information to using a card’s skimmed details from an illegal device, stolen card fraud involves the unauthorized use of credit or debit card information. Fraudsters use card details to make unauthorized transactions or cash withdrawals, leading to financial loss for legitimate cardholders and the financial institutions involved.
- Chargeback fraud: Frequently referred to as friendly fraud, chargeback fraud occurs when a cardholder makes an online purchase and then requests a chargeback from the issuing bank after receiving purchased goods or services. Legitimate chargebacks are meant for unauthorized use or defective products. Chargeback fraud occurs when a request is made despite there being no actual issue with the transaction.
- Refund fraud: Another common type of fraud that occurs when money is illicitly obtained from a business through deceptive means. In other words, when an individual makes a purchase (either legitimately or fraudulently) and manipulates or deceives a merchant’s return policy to obtain a refund or credit they are not entitled to, resulting in a financial loss for the business.
- BIN attacks: A brute force type of attack in which fraudsters use the first six digits on a credit card to algorithmically try to guess the other legitimate numbers in an attempt to generate a usable card number. Once a valid card number is obtained, fraudsters use it to make unauthorized transactions or create counterfeit cards.
- Gift card fraud: Using stolen or fake gift card details to make unauthorized purchases, often through scams or account takeovers. Fraudsters exploit the anonymity and ease of use of gift cards for illicit transactions, including chargebacks, pay-with-gift-card scams, and the generation or theft of card numbers for resale or laundering.
- Authorized Push Payment (APP) Fraud: Refers to fraudulent activity where victims are coerced into executing real-time payments to fraudsters, often through social engineering tactics, including impersonation. These authorized fraudulent schemes can include investment scams, in which victims are deceived into transferring funds for fictitious investments and romance scams, in which the fraudster tricks the victim into believing they are in a romantic relationship.
How Payment Fraud Detection Works
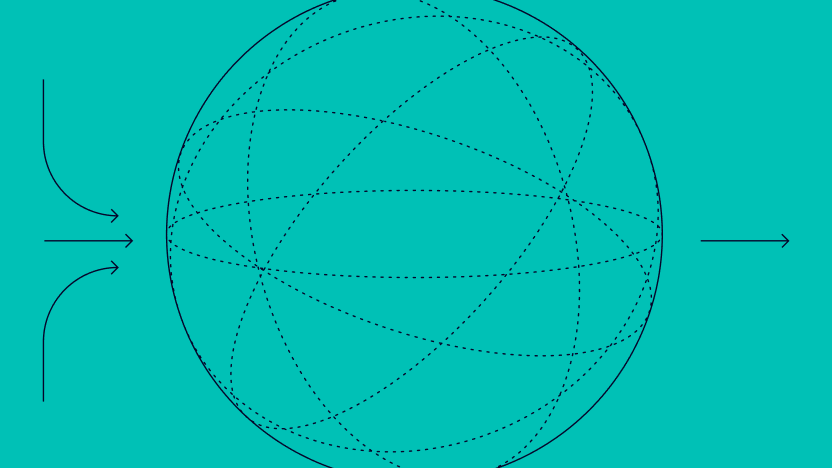
Payment fraud doesn’t happen in one place or at one moment; it surfaces across the entire customer journey, from account creation through to settlement. That’s why effective detection isn’t a single control but a layered system, one that catches anomalies in real time while reducing friction for legitimate users.
The foundation of modern fraud detection is gathering and cross-referencing signals at every touchpoint to build a fuller picture of who is actually behind a transaction.
IP and network signals add location and connection context. Mismatches between a user’s claimed origin and their network characteristics or signs of anonymization tools can indicate elevated risk, particularly when they appear alongside other anomalies.
Device intelligence examines the hardware and software environment in which a user operates. Consistent device behavior is a marker of genuine users; emulators, spoofed configurations and multiple accounts tied to the same device signature are not.
Card and issuer verification uses Bank Identification Number (BIN) data to validate that card details align with the expected issuer, region and card type — a check that frequently surfaces card-not-present fraud and testing activity before a transaction completes.
Real-time transaction monitoring compares each payment against established behavioral baselines — for an individual user, a customer segment or a merchant category. Sudden velocity changes, atypical geographies or unusual spending patterns can all trigger risk flags in the moment they occur.
“Every leap in payments innovation comes with a trade-off; the faster money moves, the less time there is to stop it from moving in the wrong direction.”
Husnain Bajwa, SVP of Product for Risk Solutions
In practice, this means payment risk detection logic must operate at the speed of the transaction itself — not after the fact.
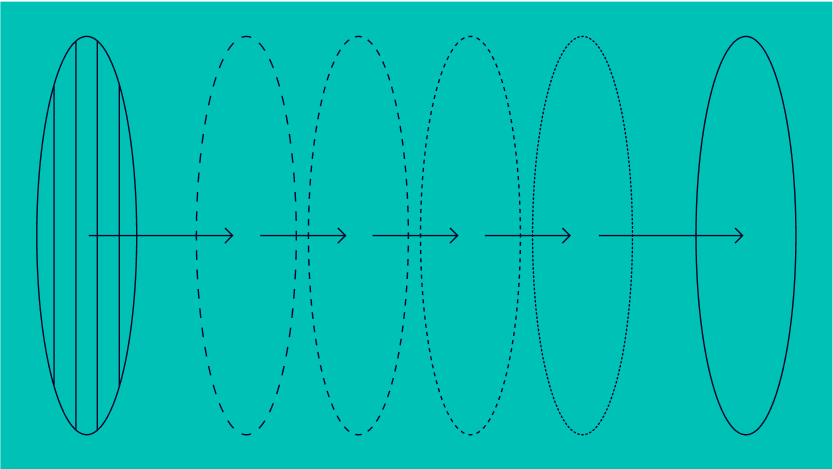
Adaptive rules allow fraud teams to tune detection logic to their specific business context, adjusting thresholds, adding conditions and evolving rule sets as new threats emerge or traffic patterns change.
Machine learning extends the reach of rule-based systems by identifying subtle, evolving behavioral patterns that static rules may miss. Models trained on transaction data can adapt as fraud tactics shift, flagging risk that doesn’t yet fit known profiles.
Behavioral analytics provides a continuous layer of context throughout a session. The way a user types, navigates and interacts with a platform differs meaningfully between genuine customers, bots and compromised accounts, giving fraud teams a behavioral signal independent of the data a user submits.
AML and sanctions screening adds a compliance dimension for regulated payment providers, cross-referencing users and transactions against watchlists and monitoring for patterns consistent with financial crime.
Case management and investigation tools bring these signals together for human review when it’s needed, giving analysts consolidated context across a user’s history to make faster, more consistent decisions and reduce false positives.
Together, these methods create a detection posture that covers the full payment journey from the moment a user signs up to the point funds are settled, enabling businesses to act on risk early, accurately and without disrupting the customers they want to serve.
Félix Improves Onboarding
“The effect was immediate and eye-opening. It’s given us the confidence to drive forward at full speed”
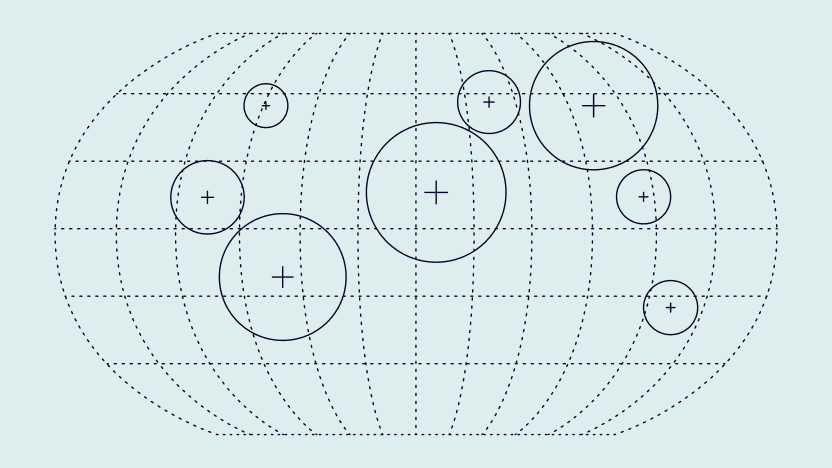
Where Payment Fraud Happens: High-Risk Points in the User Journey
Payment fraud targets three specific moments where account control or sensitive data is most exposed. Identifying these touchpoints allows businesses to apply layered defenses without adding friction for legitimate users.
- Account Creation (User Signup Fraud): When new accounts are opened with fake or stolen credentials, fraudsters gain a foothold before a single transaction occurs. Analyzing digital signals at signup, such as email quality, phone validity and IP reputation, lets fraud detection tools flag synthetic or stolen identities before access is granted.
- Account Login (Account Takeover Fraud): Login events are the primary vector for account takeover (ATO) attacks. Monitoring IP consistency, device fingerprints and behavioral patterns at each login helps detect credential stuffing and session hijacking in real time.
- Checkout (Card-Not-Present & Transaction Fraud): At the point of payment, fraudsters exploit stolen card data or manipulate payment flows to push through unauthorized transactions. Real-time risk scoring compares each transaction against established customer behavior, flagging mismatched billing details, unusual velocity or sudden spend spikes for immediate review.
Addressing fraud at each of these stages rather than at the transaction alone provides businesses with a significantly broader detection surface and reduces both false positives and revenue loss.
Choosing a Payment Fraud Prevention Solution
Selecting the right fraud prevention solution starts with understanding your own risk exposure. Different business models, payment volumes and customer profiles create different fraud surfaces, and no single configuration suits every operator.
The most effective payment fraud detection solutions address fraud across the full customer journey rather than at a single checkpoint, since fraudsters probe for gaps wherever controls are weakest.
Key criteria to evaluate:
- Integration depth: Clean connectivity with existing payment infrastructure, with minimal engineering lift and clear API documentation
- Signal breadth and data freshness: Accurate detection depends on the quality and recency of the underlying data, enriched with real-time signals from digital footprints, device intelligence and behavioral context
- Transparency in scoring: Explainable risk scores allow analysts to understand decisions, challenge incorrect outcomes and refine rules over time
- Adaptability: Rule sets and machine learning models should evolve as fraud patterns shift, without requiring vendor intervention for every change
- Customizable rules engine: The ability to tune thresholds and review borderline cases is as important as the raw catch rate
Businesses that treat fraud prevention as a fixed configuration rather than an evolving capability tend to fall behind. The strongest approaches pair automated detection with analyst tools to investigate, learn and adjust, keeping defenses current as threats develop.
Frequently Asked Questions
Strong detection reduces fraud loss, chargebacks, manual reviews and customer trust erosion across the payment journey. Without detection coverage at registration and login, fraud that occurs earlier in the customer journey reaches the payment stage undetected, making it significantly harder and more expensive to stop.
Detection identifies risky activity in real time and surfaces it for a decision. Prevention focuses on stopping fraud from succeeding through controls and workflow design. The two functions are complementary: detection provides the signal, prevention applies the response.
CNP fraud, card testing, BIN attacks, APP fraud, account takeover at checkout, gift card fraud and synthetic identity fraud are the most common categories. Each requires different detection signals and response approaches
Core signals include device, IP and geolocation intelligence, digital footprint analysis across email and phone data, behavioral analytics, velocity rules and card and issuer data. Layered signals reduce blind spots and improve decision accuracy compared with single-point checks.
You might also be interested in reading about: