Transaction monitoring software has become essential for financial institutions, fintechs, and digital businesses to combat fraud, ensure compliance, and reduce risk. With the market expected to reach $50 billion by 2033, growth is driven by the rise of digital payments, online banking, and fintech services.
In this article, we’ll explore why selecting the right transaction monitoring software is critical for staying secure, compliant, and competitive in today’s digital finance landscape.
What Is Transaction Monitoring Software?
Transaction monitoring software is a tool used to automatically detect and flag suspicious transactions, including high-value cash deposits and unusual account activity. It is an essential component of any Anti-Money Laundering (AML) framework and helps organizations comply with government and international organizations’ regulations. Transaction monitoring software can help prevent fraud and illegal activities by identifying red flags to protect institutions and customers.
4 Features To Look For in Transaction Monitoring Software
A transaction monitoring software must be powerful enough to help you meet compliance regulations, When selecting the best transaction monitoring software, certain key features are essential to ensure compliance, detect suspicious activities effectively and streamline operations. Here are the critical features to look for:
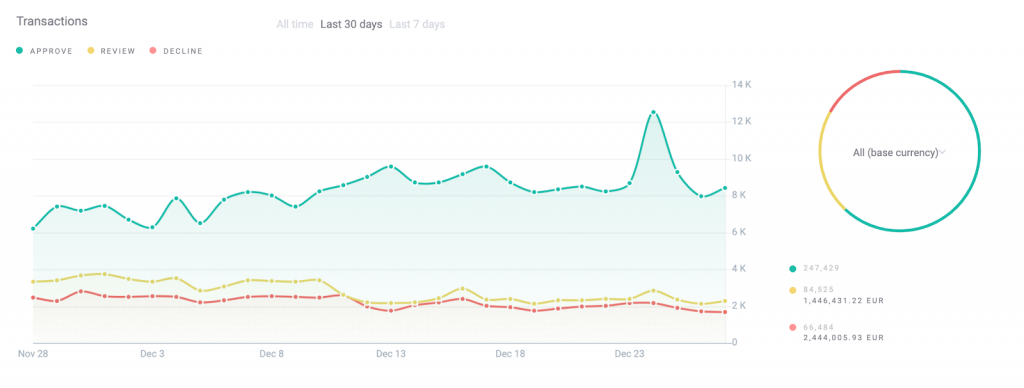
- Real-time detection with risk scoring: Effective tools combine real-time transaction analysis with dynamic risk scoring to instantly determine whether to approve, decline or flag a transaction for review. This minimizes friction for legitimate users while meeting compliance demands.
- Custom rules: As regulatory requirements evolve, your team should be able to build, test and adjust detection rules without relying on developers — ensuring fast adaptation and operational control.
- Sandbox testing: The ability to test rules in a sandbox environment using historical and live data helps reduce false positives and negatives. Look for solutions that apply AI/ML to suggest improvements based on your unique data patterns.
- Easy reporting and system integration: Robust reporting tools for audit trails and regulatory filings (like SARs), paired with easy integration into KYC, CRM and other systems, ensure a complete, compliant view of customer behavior.
The 6 Best Transaction Monitoring Software and Tools
Disclaimer: This article is based on online research and user reviews; we did not manually test every tool. Last updated in Q2 2025. Contact us for updates or corrections.
SEON: Transaction Monitoring Software that Adapts to Your Business
SEON provides a complete solution for fraud prevention and AML compliance, powered by real-time intelligence, customizable rules, and easy integration. Its advanced AML API performs deep screenings, checking for politically exposed persons (PEPs), criminal watchlists, sanctions, and blacklists — helping businesses stay compliant with confidence.
Built for flexibility, SEON allows users to set their own risk thresholds, use pre-built industry rule sets, and create custom logic in a no-code environment, enabling fast action without relying on engineering teams. By analyzing digital footprint data — like email, phone, IP, and device signals — SEON strengthens onboarding and transaction monitoring, making it easier to detect suspicious activity early and accurately.

Read reviews of SEON Fraud Fighters on G2
With SEON, you can:
- Set up intelligent, custom transaction rules — tailored to your unique risk appetite
- Detect and block suspicious activity with AI-driven alerts and pattern recognition
- Improve AML compliance through automated screening and audit-ready workflows
- Integrate quickly using a single API and prebuilt connectors for fast time-to-value
Learn more about SEON’s transaction monitoring capabilities
Speed up and automate your AML screening, monitor real-time transactions with easy-to-create rules and lock down suspicious activity with machine learning.
Speak with an Expert
Unit21
Unit21 offers no-code tools that help risk and compliance teams detect and manage fraud, money laundering, and other financial threats. Its platform combines a simple API with an intuitive dashboard to support real-time monitoring across various industries, making it accessible even for non-technical users. Built by security experts, Unit21 follows best-in-class security practices to ensure data protection and system reliability.
SAS
SAS is a leading provider of analytics software, known for its strong focus on data-driven solutions. Its hybrid approach to transaction monitoring combines AI, machine learning, and traditional techniques to deliver more accurate results. By leveraging graph analytics, anomaly detection, and text analysis, SAS helps businesses precisely identify suspicious behavior and uncover hidden risks within complex datasets.
Actico
Actico’s digital decisioning platform offers a range of tools for transaction monitoring, money laundering detection, and credit scoring, helping businesses automate and streamline their compliance processes. While it provides strong support for regulatory requirements, it lacks core fraud prevention and identity verification features. As a result, additional tools are needed to achieve full KYC or PSD2 compliance and cover the broader spectrum of risk management needs.
iComply
iComplyKYC supports AML compliance across 240+ countries and recognizes over 4,000 document types, helping businesses manage regulatory requirements on a global scale. It offers automated screening through access to exclusive global databases, making identity verification faster and more reliable. However, its transaction monitoring capabilities are primarily focused on individuals rather than detecting broader transaction patterns, making it a partial solution for organizations with more complex monitoring needs.
Dow Jones
Dow Jones provides automated risk screening and continuous monitoring of individuals and entities, helping businesses stay ahead of potential threats. Its tools are designed to analyze both structured and unstructured data from a wide range of sources, offering deeper insights into risk profiles. By delivering real-time threat detection, Dow Jones supports faster decision-making and strengthens overall compliance and risk management efforts.
Why Is Transaction Monitoring Software Important?

Transaction monitoring software is essential for modern risk and compliance teams. It enables businesses to detect suspicious activity in real time, manage risk more precisely and meet regulatory obligations with greater ease.
- Improve compliance: automated AML screening and real-time transaction monitoring ensure businesses meet regulatory requirements efficiently. Transactions are continuously screened against sanctions lists, PEPs and watchlists, keeping compliance processes rigorous and streamlined.
- Reduce the risk of fines: transaction monitoring software minimizes the risk of regulatory breaches by detecting suspicious behavior in a timely manner and maintaining a clear audit trail. Built-in reporting and customizable rule sets help demonstrate due diligence and reduce exposure to enforcement actions.
- Flag suspicious transactions to protect customers: advanced velocity rules and pattern recognition flag anomalous activity that may indicate fraud or abuse. This enables faster intervention, reducing harm to legitimate users and preserving trust in your platform.
- Identify potential fraudsters and criminals: the software uncovers hidden risks by analyzing digital footprints, device intelligence and behavioral signals. Machine learning enhances the detection of fraud rings, account takeovers and money laundering schemes, allowing you to act before damage is done.
Ultimately, AML transaction monitoring renders your organization’s incoming and outgoing payments safer while also helping you achieve compliance while becoming more efficient, trustworthy, and respectable.
How to Deploy Better a Transaction Monitoring Tool
Transaction monitoring software should be considered part of any customer risk assessment process and customer screening procedures, as fully automated on-premise installation or included as an outsourced third-party solution deployed as a layer in risk management. Regardless of the approach, here are a few tips on the best practices:
- Analyze inbound and outbound transactions: Evaluate both the flow of funds and the identities involved in transactions. This step aligns with customer due diligence (CDD) and know your customer (KYC) protocols. Accurate ID verification is essential for uncovering inconsistencies in user behavior and strengthening AML compliance across your operations.
- Monitor user activity: Customer behavior varies across financial products, so it’s important to track patterns carefully. For example, digital banks must watch for accounts involved in illicit transfers. Comparing activity across similar profiles improves detection. Your transaction monitoring system should support custom rules, dynamic risk scoring, and prioritized alerts to adapt AML strategies to your risk environment.
- Track transaction velocity: Set velocity rules within your monitoring system to flag unusual fund movements. These rules help detect rapid or repeated transactions that may signal fraud or money laundering. Be sure to calibrate thresholds to account for legitimate patterns, such as payroll deposits or high-volume users, to reduce false positives while maintaining oversight.
- Validate IBANs with context: International Bank Account Numbers (IBANs) were once a reliable way to link users to banks. Tools like IBAN.com can still verify details, but with digital banks like Wise, Revolut, and Monzo using sponsor banks, results can sometimes be misleading. When automating transaction monitoring, keep these nuances in mind, especially for geolocation filters or sanctions checks.
- Log and analyze historical data: Effective AML compliance goes beyond real-time alerts—it requires robust data retention for retrospective analysis. Your transaction monitoring system should maintain detailed logs, enabling you to reevaluate past transactions as new intelligence becomes available. Historical data is also valuable for training AI models, allowing your system to refine risk rules and improve detection accuracy over time.
See how SEON delivers adaptive, scalable, audit-ready transaction monitoring without added friction.
Ask an Expert
The Challenges of Deploying Tools for Transaction Monitoring
While transaction monitoring software is a regulatory requirement, its implementation often creates friction within companies and among risk teams — mainly due to the following factors:
- High cost: Whether deployed on-premise or through a third-party provider, transaction monitoring tools are costly to integrate, maintain and update over time.
- Labor-intensive: These systems help process growing volumes of data but still require a well-resourced compliance team to review alerts and generate reports.
- Time-consuming: The sheer volume of alerts can burden compliance teams, demanding significant time and effort for ongoing monitoring.
How SEON’s Software Does Transaction Monitoring
SEON brings together identity verification, transaction monitoring, and user authentication into one flexible, AI-powered platform. We help businesses meet AML compliance efficiently, accurately, and on their own terms.
Risk teams can tailor rules to their risk appetite, using either custom setups or machine learning suggestions — keeping full control at every step. SEON adapts to your business, not the other way around.
What sets us apart is our use of hidden digital footprint data, providing actionable insights that strengthen fraud prevention and AML efforts. With transparent, usage-based pricing, businesses of any size can access enterprise-grade protection without stretching budgets. As real-time transaction monitoring becomes essential, SEON delivers the tools to move faster, reduce risk, and stay audit-ready.
FAQs
Transaction monitoring software automates the detection of suspicious transactions in real-time, essential for AML and transaction fraud detection. It collects and normalizes data, applies rules to identify suspicious activity, and uses advanced analytics to detect anomalies. The system generates alerts for flagged transactions, which AML analysts review and investigate. Confirmed suspicious transactions are reported to regulatory authorities. The software is continuously updated to adapt to new threats and regulatory changes.
Deploying transaction monitoring tools presents several challenges. First, integration and maintenance costs can be high — especially for legacy systems or highly regulated sectors. Second, managing large volumes of alerts can overwhelm compliance teams, particularly when false positives are common. Finally, staying ahead of evolving threats and meeting changing regulatory expectations requires constant tuning, skilled personnel and access to high-quality data.
Transaction monitoring is critical for identifying and stopping money laundering, fraud and other illicit financial activity. It helps institutions protect themselves, their customers and the broader financial system. Beyond security, it’s also a legal obligation — failure to implement effective monitoring can result in substantial regulatory fines and reputational damage.
Businesses can manually monitor transactions, build in-house tools or deploy third-party transaction monitoring software. Increasingly, organizations choose third-party solutions for their speed, scalability and regulatory readiness. These tools integrate with internal systems to track deposits, withdrawals, payments and account activity — raising real-time alerts when thresholds are exceeded or behaviors deviate from expected patterns.