Worldwide, shoppers are growing used to having convenient shopping experiences that are entirely virtual, up until the point their real purchase arrives at their door. Many expect this now as standard. This includes online storefronts, online banking to manage their funds digitally, and, naturally, digital payment options, including virtual credit cards (VCCs).
According to Juniper, virtual cards are a growing market: Their market size was $2.4 trillion in 2022, and Juniper predicts that their worth will increase by 280% by 2027 – meaning the market could have a value of $9.1 trillion in the near future.
The downside is that fraudsters see any new innovation in payment processing as an opportunity and virtual credit cards are no exception. The nature of virtual credit cards being entirely online and often mobile offers user convenience, but also an entirely new attack surface for fraudsters. Though some fraudulent attacks may be unique to virtual credit cards, many are common to digital payment fraud in general, meaning there are established ways to stop them.
Let’s look into VCCs and the fraudulent attacks to which they can be vulnerable.
What Is a Virtual Credit Card?
A virtual credit card is functionally similar to a traditional plastic credit card, except that it exists purely digitally. Generally, VCCs can be accessed via a mobile wallet or website. They offer certain security advantages over traditional cards as they are less likely to be physically stolen.
For example, virtual card users don’t pose the risk of physically exposing their numbers and data to anyone else, avoiding things like scammers with data-stripping card skimmers.
Some VCC providers offer temporary, pre-paid, and one-time-use cards for security and flexibility.
In the modern consumer landscape, VCCs can be used anywhere online that accepts card payments, and generally anywhere in-person where a mobile device can be tapped to pay. Notably, virtual cards can’t be swiped in a card reader.
Though most VCCs are offered by banks and connected directly to a bank account, there are companies that only offer VCCs, such as Entropay, ecoPayz, and Payoneer. Services like these can generate temporary cards, prepaid cards, or one-time-use cards, and can be charged with a variety of payment options. At the time of writing, three major US banks offer fully virtual or “hybrid” cards: CapitalOne, Bank of America, and Citibank.
This move to virtual cards from plastic is a more secure one in a certain sense, but it also exposes that payment ecosystem to the world of digital fraud, which is expanding much faster than the ways your plastic card can be pickpocketed.
What Is the Risk of Virtual Cards?
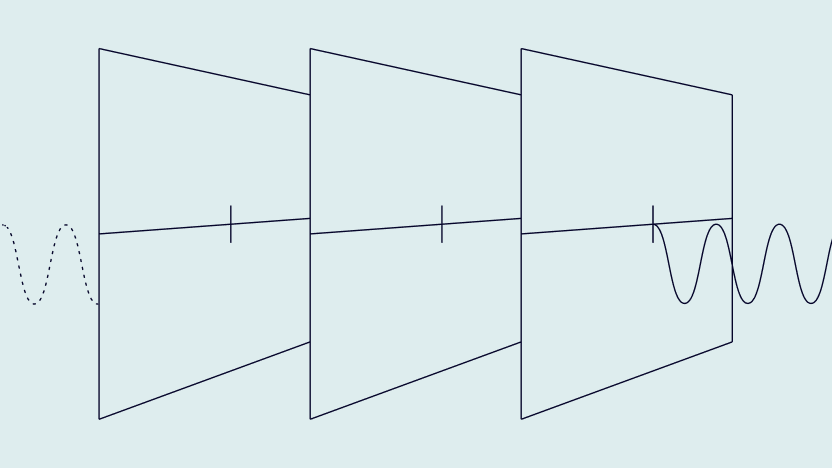
While they cannot be physically lost or stolen, virtual credit cards present an entirely new digital vector for fraudsters to attack. Like any online account, virtual credit card accounts, the mobile wallets they are kept in, and even the online bank accounts they may be connected to are vulnerable to account takeover (ATO) fraud, phishing, and more sophisticated attacks, such as man-in-the-middle attacks.
In certain offline situations, virtual credit cards can offer less security than a physical credit card, as everyone will know that, if their plastic card is lost or stolen, they should cancel their card immediately to avoid unauthorized charges. As there is no physical reminder that this must be done with a virtual card, the theft or breach could potentially go unnoticed while exorbitant charges or snowballing data theft occurs.
This is especially true if the VCC user decides to opt out of notifications associated with their virtual card use. Both physical and virtual cardholders often have the choice to receive a text message or app notification every time their card is used, but many people choose not to. Timewise, this can lead to an extended attack surface for a fraudster to exploit.
Though virtual card providers offer nominally more secure options, like cards that expire quickly and thus can’t be used to rack up unauthorized charges outside of a narrow time window, these innovations can ultimately lead the user, the provider, and the merchant into a false sense of security.
Free BIN lookup!
Enter the first 6 or 8 digits of a card number (BIN/IIN)
Text here
Other persistent security issues with VCCs stem from a lowered bar for entry when it comes to onboarding. Overall, applying for a virtual credit card generally offers a lower-friction experience than a traditional card, especially for cards that offer low risk to the provider if the customer defaults on their credit, such as single-use VCCs.
While this brings a more democratized spending power to people who previously had trouble getting a traditional credit card, it also represents new fraud vulnerabilities:
- Single-use VCCs: Fraudsters may attempt brute-force BIN attacks, using software to generate random VCC numbers, then using bots to throw those generated numbers through a payment gateway until one works.
- Multi-use VCCs: With low-friction onboarding, fraudsters may use bots to try and generate cards en masse.
- Physical credit card holders: Fraudsters may use stolen account details to apply for VCCs, potentially leading to false negative fraud checks when virtual card transactions are made.
- Other digital payment service users: Fraudsters may also target a cardholder’s mobile wallet app and/or full-service neobank account. If one of these accounts gets hacked, it can lead to more accounts being compromised, particularly if your security settings are low and you aren’t using a variety of username/password combinations.
Ultimately, virtual credit cards are developing technologies that, while promising, still come with the disadvantages that exist within the card not present (CNP) ecosystem. Users of VCCs should be aware that, although there are security benefits that come with having virtual cards, this does not mean they are invulnerable, especially after a target is subjected to phishing and ATO attacks.
How Can Virtual Credit Card Fraud Affect Your Business?
Aside from the obvious negative financial effects of credit card fraud, VCC fraud carries a particular risk to the cyber safety and reputation of your business. If a major vulnerability is found and exploited publicly, in the digital payment world this will very likely lead to a mass migration to a competing service that apparently offers tighter safety and security.
Also, the financial damage associated with VCC fraud, and CNP fraud in general, has a tendency to snowball. Users who have unauthorized charges will likely seek chargebacks, which are more damaging than refunds. Increased chargebacks can lead to a business being dropped by payment processors. And a lack of access to a reputable payment processor can start the entire negative feedback loop over again. In short, stakeholders across the payment process are impacted negatively.
As mentioned earlier, when a virtual credit card is compromised, it can lead to a greater threat of compromised cybersecurity – as opposed to someone just leaving their physical bank card in the reach of a thief. As such, organizations need to be aware that VCCs are yet another digital temptation to attract online fraudsters, and that can lead to plenty of other layers of a data breach.
Put another way, VCC fraud may be the tip of the iceberg because a single data breach can lead to far more serious ones, especially if the compromised virtual credit card was made possible by successful phishing attempts. The loss of trust from your workforce and customers, along with your overall reputational damage, can be astronomical for your business when it’s faced with online fraud – and virtual credit card fraud adds a whole new layer to how the damages can take shape.
Partner with SEON to reduce fraud rates in your business with real-time data enrichment, machine learning, and advanced APIs.
Ask an Expert
Examples of Virtual Credit Card Fraud
Let’s take a look at some major examples of fraud involving virtual credit cards (VCCs): card not present fraud, subscription abuse, trial exploitation, money laundering, and VCC generator scams.
Card Not Present (CNP) Fraud
By definition, a fraudster who misuses a VCC commits card not present (CNP) fraud because there is no physical card to use in the first place. Instead, they steal or copy their victim’s VCC and use it to make remote transactions at online shops.
CNP fraud is itself a significant problem: According to Nilson, 68% of all losses experienced by merchants and acquirers are down to CNP fraud.
Subscription Abuse
Subscription abuse is when a fraudster keeps entering new account details to benefit multiple times from the features of an online subscription, such as a streaming service or online casino.
VCCs, particularly those with low-security onboarding, or single-use functionality, can be used and regenerated multiple times in order to commit subscription abuse.
It’s worth noting that subscription abuse is an umbrella term that encompasses a range of methods used to game online account features. Promo abuse is a specific example and subset of subscription abuse and so is trial exploitation, mentioned below.
Trial Exploitation
This is when a fraudster keeps signing up with “new” accounts for services that offer a free trial, and then cancels their registration before the subscription stops being free.
Because they’re often temporary and disposable – and able to be digitally and randomly generated upon request – fraudsters can use VCCs so they don’t have to keep finding new physical credit card details.
VCC Generator Scams
It is not just the abusers of virtual credit cards who can use the technology for illicit gain. Some corrupt websites claim to offer the generation of a VCC to innocent cardholders searching the internet for an alternative to physical credit cards.
Those people can be enticed by the offer of a VCC and ultimately tricked into providing their financial information, leading to cases of phishing and/or identity theft.
How to Prevent Virtual Credit Card Fraud
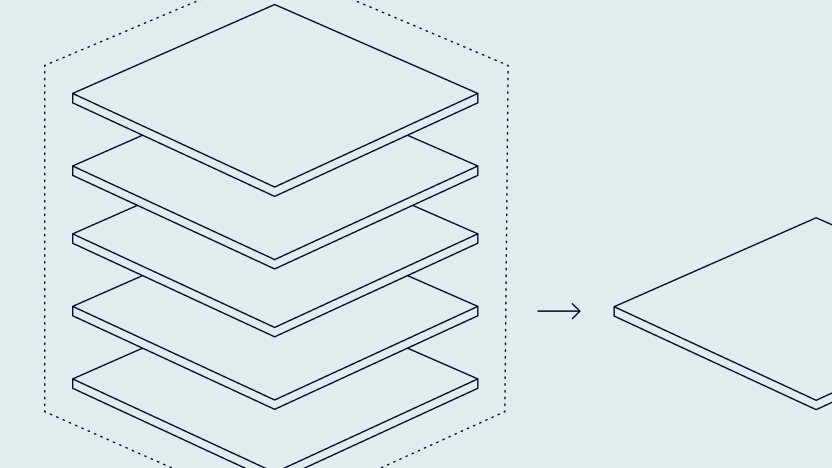
While virtual credit card fraud may not be completely preventable, it can certainly be combated with the right security checks, balanced with low friction to satisfy modern business concerns. The key is therefore for businesses that generate or accept VCCs to optimize the use of dynamic friction.
Dynamic friction is the use of proportionality in online security measures: It is a system that aims to ensure low-risk individuals are faced with limited security checks, while higher-risk individuals are scrutinized with more stringent measures.
This leads to the question of which strategies can optimize this approach of dynamic friction. Let’s take a look at some core tools that can achieve it:
- Risk-based authentication (RBA): Businesses such as online shops can take stock of a user’s transaction history and geolocation to help determine how likely a user is to be a high-risk individual and thus determine the stringency of the authentication checks that should be performed.
- Transaction Velocity Monitoring: A specific type of transaction monitoring, transaction velocity monitoring involves the frequency of transactions being monitored by a software system or fraud analyst to determine whether a user is making payments of suspiciously high amounts and/or at suspiciously high rates.
- Cardholder Verification Methods: To avoid the aforementioned snowballing consequences that unauthorized VCC purchases can lead to, businesses can introduce small moments of friction into the payment authorization process, such as requesting a virtual CVV or CVV2 that can be generated by a separate app and that behaves much like a layer of multi-factor authentication security.
These are three of the many approaches you can take to ensure the successful use of dynamic friction when dealing with potential VCC fraudsters.
On top of the above, there are of course further best practices, such as using password security apps like password managers. These help customers who are rightly using different combinations of usernames and passwords track their various login credentials, helping combat ATO attacks, which are especially dangerous in the context of VCC fraud.
It’s also key to ensure that regular audits take place to help your organization keep track of both legitimate and suspicious transactions, alongside customers, data, and operations at large.
Choosing a Solution Against Virtual Credit Card Fraud
This decision-making process should be determined by three major factors: How often your business experiences VCC fraud, how damaging the VCC fraud attacks are, and the types of approaches your attackers are using to carry out VCC fraud.
In other words, weigh up your organization’s situation and act accordingly. If you have an influx of VCC fraud that stems from account takeover (ATO) attacks, it will be best to focus your efforts on purchasing software that specializes in device fingerprinting. These efforts should not exist in a vacuum – they should be paired with awareness messaging to customers to be aware of prevalent ATO and phishing scams.
If, on the other hand, you find that you’re dealing more with VCC fraudsters who simply keep entering a suspiciously high number of new virtual credit card numbers into your business’ system of transactions, you may benefit more from a fraud prevention solution that specializes in transaction monitoring, as this will identify unusual purchasing patterns over time.
For example, SEON has velocity checks and velocity rules whose APIs can not only help you determine whether a VCC has been used but can also be adjusted in accordance with the VCC fraud patterns your organization may witness when monitoring transactions and user behaviors. If you find that, say, one IP geolocation user keeps using multiple virtual credit cards at a suspiciously high rate, this could be a sign of foul play, or at least of bot-like automation that may raise red flags.
Regardless of your experiences, circumstances, and risk appetite, it is always best to thoroughly research what may be the best fraud detection software for your business. Rather than a single one-size-fits-all system, you may find that it’s more a question of which solution or combination of solutions is best to stack together to achieve a comprehensive approach to detecting VCC fraud.
SEON’s advanced APIs and device fingerprinting provide fast, scalable fraud prevention solutions, no matter the size or ambition of your organization.
Ask an Expert
How SEON Helps Fight Virtual Credit Card Fraud
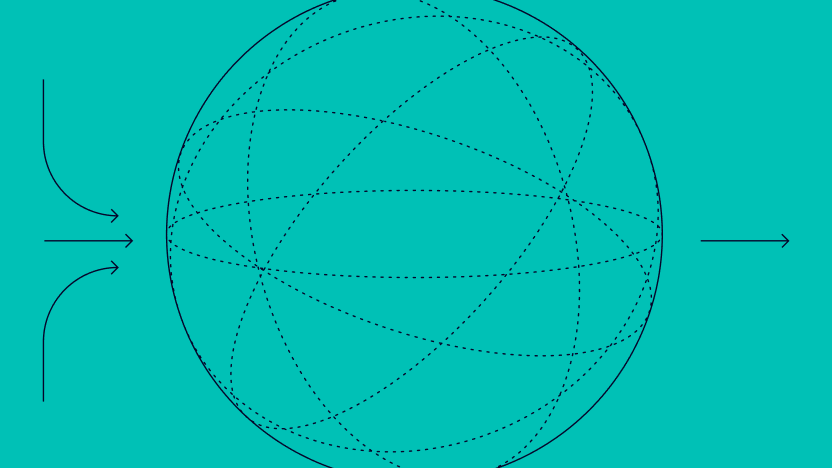
Because VCC fraud is a type of card not present fraud, traditional card security measures such as chip verification cannot prevent it. Instead, the key way to combat it is to establish specific attributes of the device being used for the VCC transaction and form an individual risk rating accordingly. Enter SEON’s device fingerprinting, IP geolocation, and fraud scoring capabilities.
A VCC fraudster can steal a virtual credit card just as they could a physical credit card. An extra downside, however, is that the victim won’t easily notice that a physical card is missing, which would trigger them to open their online banking app and click a ‘Report your card lost or stolen’ button. Accordingly, the key approach to combating VCC fraud is to do so through less of a focus on the virtual card itself and more on the virtual cardholder.
Fighting VCC fraud, therefore, boils down to using SEON’s device fingerprinting to combat fraudsters. The below animation shows an initial view of how SEON’s device fingerprinting looks in action:
FLet’s now have a closer look at how SEON is equipped to scrutinize virtual cardholders, utilizing device fingerprinting and other state-of-the-art technologies.
- Device hashes: SEON creates device hashes automatically as part of its device fingerprinting module, and this means that any changes to a hash can be flagged for review. While changes in device hashes may be innocent, they can also be a sign of an account takeover (ATO), which is a smoking gun in many attacks – including VCC fraud.
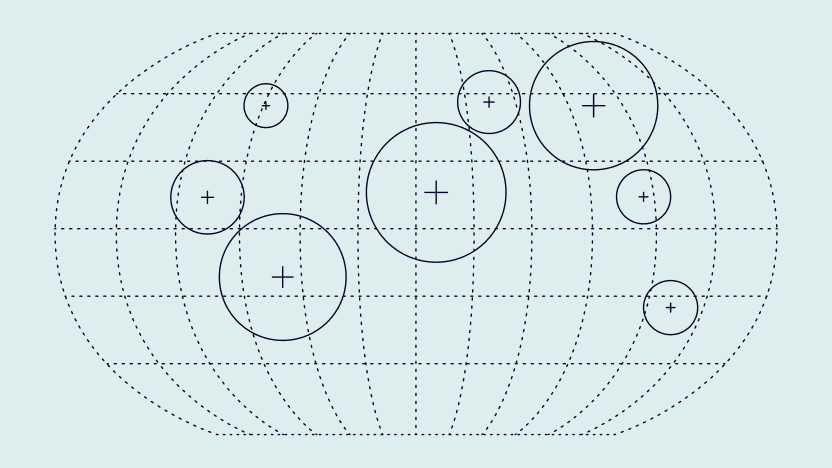
- IP lookup: Due to virtual credit cards’ use for online transactions, virtual credit card fraudsters may not even be from the same time zone as the victim, let alone the same region. SEON’s ability to flag transactions made in a different IP geolocation to the real cardholder helps spot suspicious payments that can be traced back to potential VCC fraudsters.
- Email lookup tools: SEON’s reverse email lookup tool, which utilizes open-source intelligence (OSINT) features such as social media accounts, will help determine if a user is pretending to be multiple, not-necessarily-real people all ordering to the same address using various VCC payments.
- Velocity checks: SEON users can gauge certain signs of VCC fraud that are specific to their organization and industry. For example, any business owner who is concerned by unusually high instances of VCC payments that occur in quick succession can set SEON’s velocity rules to flag such transactions for review.
- Detecting fraud with machine learning: Over time, SEON gathers historical data related to your users and their transactions. Its machine learning capabilities can use such insights to spot patterns and anomalies that may be attributable to VCC fraud.
Thankfully, the implementation of many of these security-minded checkpoints also presents little or no added friction in the user experience. Device fingerprinting and browser hash checks help facilitate the aforementioned system of dynamic friction, only adding significant roadblocks to the checkout stage for customers who are more likely to have malicious intent.
By using these data-driven approaches to finding fraudulent transactions, business owners will be altogether better equipped to combat virtual credit card fraud – along with many other types of fincrime.
Sources
- Juniper Research: Virtual Cards Market Research Report 2022-27: Size, Share
- Nilson Report: Card Fraud Worldwide
You might also be interested in: