Credit card fraud is increasingly prevalent, with projections from the Nilson Report estimating losses could soar to an astonishing $38.5 billion by 2027. As the issue becomes increasingly pervasive, understanding how to detect credit card fraud and the reasons behind its prevalence is essential for consumers and businesses alike.
In this article, we will explore the mechanisms of credit card fraud detection and the various techniques employed to safeguard transactions.
What Is Credit Card Fraud Detection?
Credit card fraud detection refers to the combination of tools, technologies and processes to prevent unauthorized purchases in both online and physical environments. The goal is simple: verify that the cardholder is who they say they are and confirm the legitimacy of every transaction.
Detection methods range from basic authentication (like CVV checks) to advanced analytics powered by machine learning. Core techniques include:
- Multi-Factor Authentication (MFA): Verifies identity using multiple layers, such as SMS codes or app confirmations
- 3-D Secure (3DS): Adds an extra password or code entry before approving a transaction
- Biometric verification: Confirms identity through fingerprints, facial recognition or voice
- One-Time Passwords (OTP): Send unique codes for single-use authentication
Modern systems also monitor transaction anomalies. For example, an order from a high-risk IP address or a device not previously linked to the customer can trigger alerts. Depending on the credit card fraud detection system in place, this can happen in real time or through retrospective investigation.
How Does Credit Card Fraud Detection Work?
At its core, credit card fraud detection combines data analysis with automated decisioning. Financial institutions and merchants rely on several overlapping methods:
- Machine Learning Models: Algorithms analyze transaction patterns to spot unusual activity, such as large overseas purchases or multiple small test transactions. These models continuously adapt as new fraud tactics emerge.
- Rule-Based Systems: Merchants create predefined rules, such as blocking transactions above certain thresholds or flagging mismatched billing and shipping addresses.
- Behavioral Analytics: Systems track how users interact with sites or apps, from typing speed to navigation habits, to identify anomalies.
- Authentication Layers: Tools like tokenization, biometric verification and 3DS provide additional barriers to unauthorized use.
By layering these approaches, businesses can block fake credit card detection attempts before losses occur, minimizing friction for legitimate customers.
With the fraud management industry set to reach USD 38.2 billion by 2025, explore our top fraud detection tools to protect your transactions effectively.
Read More
How Do Fraudsters Get Credit Card Numbers?
Unfortunately, credit card numbers are cheap and accessible on illicit marketplaces, sometimes selling for as little as $17. Criminals rely on multiple methods to acquire them, including:
- Theft: Criminals physically steal credit cards or gain access to them.
- Skimming and cloning: Fraudsters use skimmers to capture credit card details from legitimate card readers, allowing them to create unauthorized copies.
- Account takeover: A fraudster gains unauthorized access to a victim’s account linked to a credit card. The situation is often exacerbated if the account functions as an e-wallet (e.g., BNPL or cryptocurrency accounts).
- Phishing and social engineering: Scammers exploit human psychology to extract sensitive information through deceptive emails, SMS or fake online stores.
- Infiltrating legitimate online stores: Criminals inject malicious scripts into existing eCommerce websites, a technique known as online skimming, often utilizing sophisticated tools like MageCart.
Each method fuels the underground economy for stolen credentials, making credit card fraud detection essential.
How to Detect Credit Card Fraud
Detecting credit card fraud requires businesses to be vigilant in recognizing when card details may have been compromised. Various tools and techniques can help identify suspicious activities based on transaction behavior.
Card Security Features
Credit card networks have developed several security features designed to prevent fraudulent credit card networks have implemented several security measures to prevent fraudulent purchases, including:
- Address Verification Service (AVS): This service verifies the cardholder’s identity by cross-referencing their registered address with the bank’s records.
- 3-D Secure (3DS): A security layer that prompts users to enter a code to complete a transaction, offered under different names by various card operators (e.g., Visa Secure, Mastercard SecureCode).
- CVV (Card Verification Value): A three-digit card code confirming possession during a purchase.
While these features enhance security, they can also introduce friction in purchasing. For example, companies like Amazon may forgo CVV verification to streamline checkout and improve customer experience, relying instead on other security measures.
Risk Scoring
Risk scoring / fraud scoring is a standard method for evaluating transaction risk. By applying heuristic rules, businesses can make informed decisions about allowing a payment. For instance, the risk score increases if an IP address differs from the shipping address.
A velocity rule scores transaction behavior by looking at data points within a specific time frame. For instance, it might block an account after multiple failed password attempts within a short time frame. Risk scoring systems can be either transparent (whitebox) or opaque (blackbox), depending on whether risk managers customize the rules or rely on preset algorithms. Organizations with dedicated resources may prefer whitebox systems for greater flexibility, while those with limited capabilities might opt for out-of-the-box solutions.
Digital Footprint Analysis
Confirming a user’s online identity without adding friction is crucial for preventing fraudulent transactions. Digital footprint analysis serves as an invisible security layer that gathers additional information from single data points, such as:
- Digital and social checks: Assessing whether contact information corresponds with registered social and digital accounts.
- IP analysis: Checking for connections from VPNs or suspicious proxies.
- BIN lookup: Verify whether the payment card type aligns with expected usage patterns.
- Device intelligence involves analyzing information about the devices used to access your platform and identifying, for instance, whether the user has previously accessed the site from the same device.
This approach allows businesses to build comprehensive user profiles without requesting extra information, feeding valuable data into risk-scoring systems to better assess potential fraud. Digital footprint analysis can also provide crucial evidence in disputes over chargebacks or instances of friendly fraud.
How SEON Does Credit Card Fraud Detection
SEON provides an advanced credit card fraud detection system that integrates seamlessly into payment flows. Its technology empowers merchants to verify cardholder identity, block suspicious transactions and minimize chargebacks without compromising customer experience.
Key features include:
- Card BIN lookup: This feature verifies the card’s validity, identifies the issuing bank, and determines its country of origin, helping to assess the risk associated with a transaction.
- Digital footprint analysis: You can simply check the shopper’s online presence by entering their email address or phone number. A lack of a digital footprint may warrant further investigation. SEON provides 900+ first-party, real-time data signals that go deeper and further than any other provider
- IP intelligence: SEON analyzes how customers connect to your checkout process, flagging harmful IP addresses, VPNs, Tor usage or suspicious DNS activities.
- Custom risk rules: SEON comes pre-loaded with 240+ default risk rules tailored for various sectors, such as online retail and BNPL services. In addition, custom rules help automate and fine-tune risk assessment so it fits each business’s specific needs.
- Flexible integrations: Go live in days, not months. You can enhance your existing systems with additional data intelligence, connect via API for complete automation or use plugins for platforms like Shopify.
By combining these tools, SEON helps businesses achieve proactive credit card fraud detection, reduce fake transactions, and safeguard revenue and customer trust.
SEON’s customizable risk scoring, digital footprint analysis and machine learning capabilities help businesses reduce fraud by up to 99%.
Ask an Expert
FAQ
Fraud prevention software should be able to detect credit card fraud instantly. It will use a combination of risk rules to flag a transaction and prevent it before it happens. If you detect credit card fraud, you will need to initiate a chargeback request. The chargeback may take up to 120 days to be settled.
Theoretically, you can trace credit card fraud. In practice, however, it is very unlikely that the fraudster will be prosecuted – unless they are caught as part of a large-scale anti-fraud operation.
If your business processed a fraudulent credit card transaction, you are legally forced to repay the sum to the cardholder. You may also dispute the chargeback process, which may be a long and costly process.
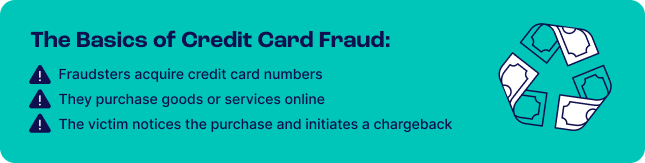
Credit card fraud happens when a fraudster gets hold of someone else’s credit card details and makes a purchase with it. This is clear fraud, where the goal is to not pay for a good or service and still receive it.
Note that there is also another type of credit card fraud that happens when the cardholder is being dishonest. In that scenario, the payment looks legitimate, but the cardholder has already decided to return the item or ask for a refund.
Sources
- Juniper Research: Online Payment Fraud
- The Guardian: Stolen credit card details available for £1 each online
- Nilson Report: Card Fraud Losses Dip to $28.58 Billion
- Magecart: A Deep Dive Into Magecart