Bots now make up most of the internet. This year, automated traffic officially surpassed human activity at 51%, marking a major shift in how the digital ecosystem operates.
For fraudsters, this isn’t just progress — it’s opportunity. Automation lets bad actors scale attacks instantly, probe defenses and slip through weak points faster than any human team can react. Bots are no longer a nuisance; they’re powerful fraud enablers capable of launching thousands of coordinated attacks with precision.
This article breaks down why bots have become such an effective fraud vector, how they infiltrate digital platforms and the key signals businesses must watch to stay protected.
What Is Bot Detection?
Bot detection is the process of identifying and distinguishing automated traffic (bots) from human users across websites, servers or networks. It aims to recognize individual bots, botnets and scripts by analyzing how they behave and connect to your systems.
Not all bots are harmful. Google’s web crawlers help index pages for search, monitoring bots from uptime services help to ensure site availability and SEO tools and site analytics bots serve legitimate functions. Yet, an alarming percentage of bot traffic is used for fraudulent purposes. According to reports, 37% of bot traffic is attributed to bad bots.
In fraud prevention, bots can signal risk as they’re often used to automate account takeovers (ATOs), generate fake signups or attempt fraudulent payments. The challenge then is to allow the good bots and stop the bad ones before they breach your defenses.
The Importance of Bot Detection for Businesses
Bot detection ensures your web traffic comes from real users. Fraudsters rely on bots to mimic human behavior and launch scaled attacks like credential stuffing, carding, bonus abuse and fake onboarding attempts. These are particularly damaging in high-risk industries like fintech, eCommerce and iGaming.
Once deployed, bot attacks can hammer your site 24/7: thousands of login attempts per second, dozens of fake signups with synthetic data, credit card fields filled in at inhuman speed. Each action undermines trust, skews metrics, adds fraud losses and bloats operational overheads like KYC costs and manual reviews.
How to Detect Bots and Bot Traffic
Bot detection often starts with spotting the subtle but consistent signs of automation — clues that separate human users from scripted activity. Unlike real users, bots behave with mechanical precision or exhibit strange inconsistencies that reveal their true nature.
- Unusual behavior patterns: Bots tend to operate at inhuman speeds — completing forms in milliseconds, refreshing pages rapidly or interacting with site elements without the natural delays you’d expect from a real user.
- Device and browser inconsistencies: Device fingerprinting can uncover mismatched or spoofed configurations that indicate the presence of bots.
- Geolocation and time-based anomalies: A user logging in from New York at 3 a.m. and again from Singapore five minutes later should raise red flags. Especially if they’re completing high-risk actions.
To detect bots effectively, you need to examine the full context of every interaction. That means not just analyzing a single data point, but correlating several: how the user connects, how fast they move through a workflow, what device they’re using and how that behavior compares to the rest of your traffic.
Bot Detection Techniques
Bot detection techniques vary in their efficacy. As such, if you’re keen to protect your business from the negative consequences of bot traffic, it’s a good idea to use a combination of approaches. Let’s take a look at some of these:
- Firewalls and blacklists: Web application firewalls (WAFs) and access-control lists (ACLs) can be effective against known threats. They provide protection from session hijacking, cross-site scripting, SQL injections and the like but advanced bots can easily slip past.
- CAPTCHAs: Useful against basic bots, but not enough on their own. Sophisticated fraudsters now use CAPTCHA-solving services or machine learning to bypass this purported safety mechanism.
- Two-factor (2FA) and multi-factor authentication (MFA) : Adds an extra step for account access, protecting against bot-enabled takeovers. That said, it won’t help against bots used for fake registrations or distributed denial of service (DDoS) attacks.
- Real-time monitoring: Constant surveillance of traffic ensures you can flag suspicious behavior as it happens rather than after the damage is done.
- Device fingerprinting: Gathers non-identifiable data from a user’s hardware and software setup to detect anomalies. Ideal for spotting emulators, automation tools and reused setups.
- Device hashes: In the case of bots set up to commit multi-accounting abuse, creating and comparing device hashes will allow you to identify returning users and bots, even if they attempt to pass off as different people.
Why Is Bot Detection So Difficult?
When it comes to the detection of basic bots, adding a few rudimentary technical hurdles will work. For insWhile CAPTCHAs have been shown to reduce bot traffic by up to 88%, the sophisticated bots are a different story. Modern bots can simulate mouse movements, typing patterns, and even human-like timing, allowing them to bypass traditional bot detection tools. To counteract this, businesses tighten their defenses to catch these advanced threats — often at the cost of user experience. Legitimate customers may face repeated CAPTCHAs, blocked logins or rejected transactions, which lead to frustration, abandoned checkouts and ultimately, lost revenue and trust.
For example, referral fraud bots are designed to trigger rewards and start affiliate fraud by completing a sequence of actions mimicking human behavior that may not raise any eyebrows.
- Sign up for affiliate programs
- Auto-click links
- Auto-fill forms using synthetic data
- Use stolen cards to make deposits
- Trigger reward payouts
- Change device settings, then repeat
These complex, human-like actions are harder to catch and incredibly damaging. That is, of course, unless you have the right bot detection tool.
Emerging Threats: AI-Powered Bots
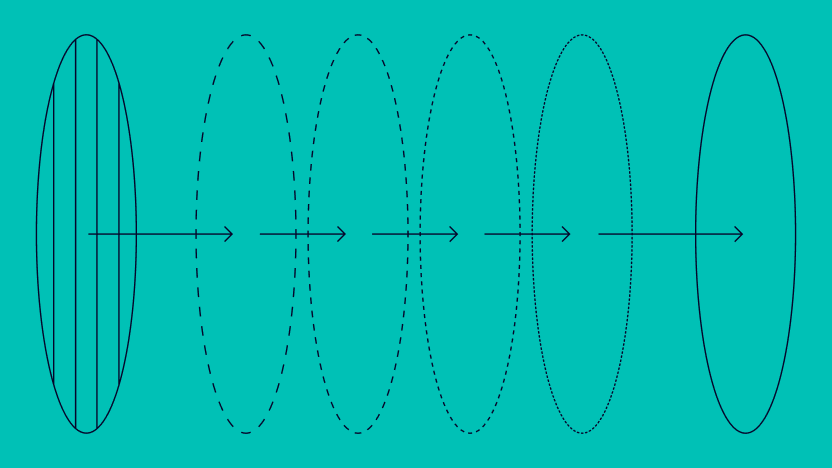
AI-powered bots are reshaping the bot detection landscape, creating threats far more sophisticated than traditional automated scripts. These advanced bots use machine learning to mimic human behavior, rotate identities and adjust their tactics in real time, making them extremely difficult to spot with CAPTCHAs, IP blocks or static rules. They can simulate realistic mouse movements, keystrokes and session flows, allowing them to blend into normal traffic while executing credential stuffing, fake signups, payment fraud and large-scale attacks at machine speed.
In high-risk sectors like iGaming, fraud rings now rely on agentic AI to automate entire abuse workflows — from generating synthetic identities to managing fleets of devices, proxies and virtual machines for multi-accounting and bonus abuse. This turns fraud into a continuous, industrialized operation that outdated detection systems cannot keep up with. To defend against AI-powered bots, businesses need real-time behavioral analytics, device intelligence and anomaly detection capable of identifying subtle, AI-generated patterns that human users would never produce. As these threats evolve, adaptive, multi-layered bot mitigation is no longer optional — it’s essential for staying ahead of modern fraud.
Explore SEON’s latest thought leadership on how agentic AI is scaling bonus abuse — and what operators need to stay ahead.
Read more
How Does SEON Help With Bot Detection
SEON’s fraud prevention enables fraud detection and bot mitigation by combining machine learning, data enrichment and real-time monitoring to paint a full picture of any user interacting with your platform.
- Spot spoofed environments with device fingerprinting: Detect headless browsers, emulators and virtual machines by analyzing over 300 device parameters. Ideal for catching bots trying to spoof or rotate identities.
- Separate humans from scripts with behavioral analysis: Monitor mouse movements, typing cadence and timing to identify automated behavior, making it easier to block bots that mimic real users.
- Uncover hidden threats with IP & network intelligence: Flag connections using proxy and VPN and compare IP geolocation with user-submitted information to catch inconsistencies and expose coordinated bot activity early.
- Catch high-speed automation with velocity rules: Detect unnatural activity spikes, like mass account creation or repeated logins, by tracking the speed and frequency of user actions in real time.
By layering these capabilities, SEON gives you a proactive, adaptable defense against both basic and sophisticated bot threats — catching them early, and acting before they harm your business.
FAQs
Bot detection starts with gathering data about your user’s behavior and connection. By looking at whether they connect with proxies, VPNs, or Tor, you can increase suspicions. Emulators and virtual machines should also raise red flags. Then you need to compare such data and user actions with others to spot patterns.
An IP address isn’t usually enough to let you know if you’re dealing with a bot or not. However, you can assess whether it points to a VPN, proxy or Tor browser. This can help you raise red flags, depending on the user’s behavior.
Not directly. An IP address alone won’t confirm whether you’re dealing with a bot, but it can provide useful context. If the IP is linked to a known proxy, VPN, data center or Tor exit node, that’s a signal worth investigating, especially when combined with behavioral data like high-speed clicks, repeated login attempts or identical browser fingerprints across multiple accounts.
The easiest way to block bots is to enable CAPTCHAs. However, it won’t stop the more sophisticated bots. To block those, you need to enable a combination of data enrichment (to learn more about how they connect to your site) and velocity rules (to understand their online behavior).
Sources
- Imperva: 2025 Bad Bod Report