By 2025, automated traffic had officially overtaken human activity, making up 51% of all online traffic. While many of these bots serve useful purposes, according to recent industry reports, 37% of all bot traffic is malicious.
Bot attacks have evolved from a background nuisance into one of the most effective enablers of online fraud. As attackers use them to scale abuse instantly, probe systems for weaknesses and execute thousands of attacks simultaneously, businesses find themselves in a bind: block too little and fraud scales, block too aggressively and legitimate traffic suffers.
Key Takeaways
- Bot attacks use automated scripts to mimic human behavior and scale fraud and cybercrime
- Not all bots are bad, but separating malicious bots from legitimate automation is a challenging task
- Common bot attacks include credential stuffing, DDoS, phishing, scalping and inventory denial
- Traffic spikes, failed logins and abnormal behavior patterns are early warning signs
- Effective bot prevention relies on layered defenses
What Are Bot Attacks?
A bot attack is an automated attack carried out using scripts or programs (“bots”) designed to imitate human behavior. These bots can interact with websites, apps, servers and APIs without direct human involvement. In some cases, coordinated bot and botnet attacks have even been used against entire organizations, government agencies and critical infrastructure.
Not all bots are inherently harmful, which is why distinguishing between legitimate and malicious bots is essential. Legitimate bots play a critical role in the digital ecosystem. Search engine crawlers like Googlebot help pages get indexed and discovered, uptime monitoring bots ensure websites remain available and analytics bots support performance tracking and optimization.
Malicious bots, on the other hand, are designed specifically to exploit systems for fraud or abuse. In the context of fraud, this scale is especially dangerous. Bots enable attackers to multiply attempts across key touchpoints such as signup, login and checkout, turning isolated attacks into sustained, high-volume campaigns with minimal effort and maintenance.
What Are the Different Types of Bot Attacks?
Bot attacks come in many forms, depending on the attacker’s goal and the part of the user journey being targeted. Below are some of the most common types businesses need to defend against:
- Credential Stuffing Bot Attacks
- DoS and DDoS Attacks
- Phishing Bot Attacks
- Spambot Attacks
- Scalper and Ticketing Bot Attack
- Inventory Denial Bot Attack
1. Credential Stuffing Bot Attacks
Credential stuffing is the automated attempt to crack someone’s account using a list of login details and passwords. It is extremely damaging for companies and their users, as it inevitably leads to account takeover fraud. Once bots have access to an account, fraudsters can cause all kinds of havoc, from identity theft to data breaches and payment fraud.
Statistically, these kinds of attacks have a low success rate, averaging around 0.1%, according to Cloudflare. This explains why fraudsters automate them using bots, which saves time and resources
2. DoS and DDoS Attacks
Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks aim to overwhelm a system so legitimate users can no longer access it. Bots flood servers with requests, draining resources and causing outages.
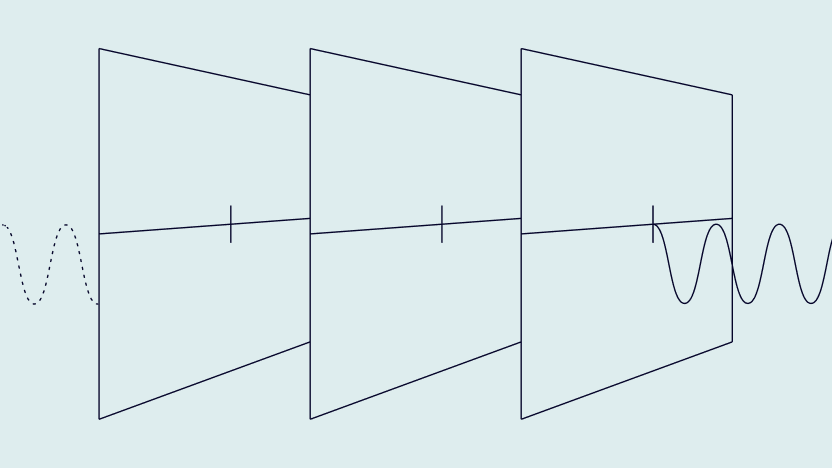
There are two common approaches:
- Low and slow attacks: Bots send subtle, long-running requests over time, gradually straining resources while avoiding detection. These attacks are harder to identify but can be just as disruptive.
- Fast attacks: High-volume traffic floods the system all at once, overwhelming servers immediately and causing instant downtime.
Both methods rely on automation and scale, making them impossible to execute manually.
3. Phishing Bot Attacks
The goal of phishing attacks is to trick victims into revealing sensitive information such as passwords, payment details or personal data. Bots automate phishing by handling outreach at massive scale.
- Email phishing: Bots send thousands of phishing emails in bulk, rotating sender addresses to bypass spam filters.
- Marketplace phishing: Scripts automatically reply to listings, requesting contact or payment details from sellers.
- Social media phishing: Bots send automated DMs prompting users to click malicious links or share information.
- Online dating phishing: Bots mimic real profiles, initiating conversations that lead to romance scams or identity theft.
4. Spambot Attacks
A spambot attack targets websites and takes advantage of various vulnerabilities to help a different website or page rank better and get more traffic. In the process, it is likely to result in a drop in traffic to the targeted website, because the bot’s spam content is incorrectly perceived as being created or enabled by the legitimate site’s administrators.
If your website has a public-facing tool such as an online form, a blog with open comments, or a shopping basket, you may be a the mercy of spambot attacks.
5. Scalper and Ticketing Bot Attack
Selling and buying tickets should be a straightforward affair. That’s until ticket scalpers realized they could buy the entire supply for a sold-out event and resell tickets at a higher price.
Of course, manually purchasing hundreds or thousands of tickets is physically impossible – especially when time is of the essence. This is where scalper and ticketing bots become a problem.
Fraudsters use automated scripts to purchase all the tickets as soon as possible. This has led to dissatisfied punters, and ticketing platforms scrambling for quick fixes.
6. Inventory Denial Bot Attack
Inventory denial attacks are similar to scalping but serve a different purpose. Instead of buying items to resell, bots reserve or add products to carts without completing purchases, preventing legitimate customers from buying high-demand items.
The main goal is disruption. For ecommerce businesses, this leads to lost sales opportunities, artificial scarcity and increased cart abandonment and return fraud
Learn how Europe’s largest online marketplace for collectible cards blocked bot attacks and fake accounts at scale with SEON.
Read the case study
How Do Hackers Perform Bot Attacks?
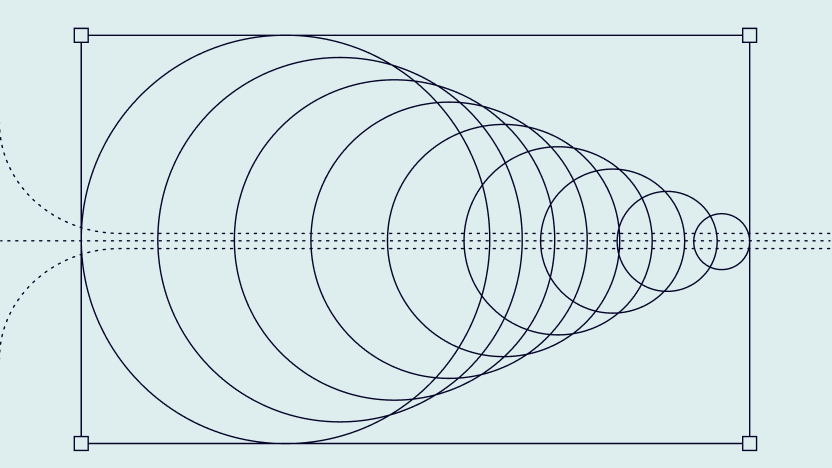
Bot attacks typically follow an automated lifecycle, allowing the process to repeat itself with minimal human input.
Let’s take a look at the typical stages:
| Stage 1 | Recon | Bots scan systems automatically to identify vulnerabilities and weak points. |
| Stage 2 | Setup | Attackers configure scripts to define timing, frequency and attack logic. |
| Stage 3 | Attack | Bots execute actions at scale across the entire user journey. |
| Stage 4 | Outcome | Attackers assess results and adjust scripts to improve effectiveness. |
What Is the Difference Between Bot Attacks and Botnet Attacks?
The key difference between bot attacks and botnet attacks lies in scale and coordination. A bot attack typically involves a single automated script or a small number of bots operating from one device or environment. These attacks can still be damaging, especially when targeting login pages, signup flows or payment forms.
A botnet attack, however, is far more powerful. Botnets consist of large networks of compromised devices all controlled remotely by an attacker. Because traffic is distributed across many IP addresses and locations, botnet attacks are significantly harder to detect and block. This makes them especially effective for large-scale DDoS attacks, coordinated credential stuffing campaigns and other high-volume forms of abuse.
Who Do Bot Attacks Target?
Bot attack targets are diverse and varied, just like victims of fraud or cybercrime. In general terms, the following are often targeted by bad bots:
- Websites: A bot may target websites for DDoS attacks, web content scraping, and so on.
- Online shops: There are plenty of reasons for criminals to want to target ecommerce and other companies that accept online payments. These include card testing, which is used to see which stolen card numbers are still valid, and account takeovers, which are increasingly more harmful due to shoppers storing their card numbers in their accounts for faster payments.
- Fintechs: Fintechs, online lenders, as well as companies in the BNPL sector, are prime targets for bot attacks. Some fraudsters want to carry out schemes that involve such things as automated and repeated attempts at loan applications, and account opening with stolen IDs.
- Individuals: Some fraudsters use bots and automation to target individuals, both private and professional. Perhaps predictably, these include obtaining personal information for identity theft and the creation of synthetic IDs. This is in addition to phishing for account passwords and further information to defraud others.
Why Are Bot Attacks Dangerous?
Bot attacks can harm their targets in a myriad of ways, depending on how they are deployed and the nature of the scheme.
For businesses in particular, the harmful effects of bot attacks include:
- revenue drop from lost sales or reputational damage
- website and/or server downtime
- increased chargeback requests, also affecting chargeback rates and relationships with payment processors
- organizational or customer data breaches
- compliance fines, such as those for anti-money laundering and GDPR – or even criminal charges
- decreases in stock price if a major attack is made public
- Google and other search engine ranking penalties for the website
Companies must do their best to prevent bot attacks, regardless of whether they are enabling fraud, cyberattacks, account takeovers, application fraud, or simply unscrupulous shopping.
That’s why many teams add bot detection software. It helps separate automated traffic from real users, so you can block suspicious activity earlier and keep normal customers moving.
What Are Botkits?
Simply put, a botkit isn’t necessarily linked to malicious bots – it is any SDK (software development kit), often open-source, that allows its users to build or customize a bot. However, when botkits are used to enable cybercriminals to conduct bot attacks, they are bad news. Because of their customizability, they allow more tech-savvy fraudsters to work more efficiently.
The dark web as well as parts of the clearweb are rife with fraudsters helping each other and providing free or paid-for fraud enablement tools such as botkits, which can make bot attacks more devastating. Vigilance is key to bot attack prevention.
How to Prevent Bot Attacks using Bot Prevention Techniques
There isn’t one “best” bot fix. What works depends on what you’re dealing with, like credential stuffing, scraping, fake signups, or card testing. In most cases, the safest approach is to layer a few defenses rather than betting everything on one control.
- Start by monitoring traffic at the points bots usually target: signup, login, and checkout. A WAF or firewall helps with known bad traffic, but you’ll usually need more than that.
- At signup, try to collect a bit more context so you can spot automation early. Simple checks like email and IP enrichment, plus device signals, often surface patterns that don’t look human. From there, velocity rules help catch bots that move too fast, repeat the same action over and over, or cycle through IPs while keeping the same underlying setup.
- On the login side, MFA is still one of the most reliable ways to slow down credential stuffing and brute-force attempts. For payments, enabling SCA/3DS (even when it’s optional) can make automated card abuse harder to scale.
CAPTCHAs can reduce noise in certain flows, but they’re not a silver bullet. Attackers can route around them or use solving services. The last layer is using behavioral patterns and anomaly detection (sometimes with machine learning) to pick up new bot tactics that rules don’t catch yet.
How SEON Can Help You Prevent Bot Attacks
Bot detection is becoming a central pain point for a number of verticals, including ticketing, where 39% of all traffic comes from bad bots, or gambling and gaming (25.9%). This is why SEON flags and blocks bot activity at several touchpoints and in real-time, always informed by fraud trends and industry needs.
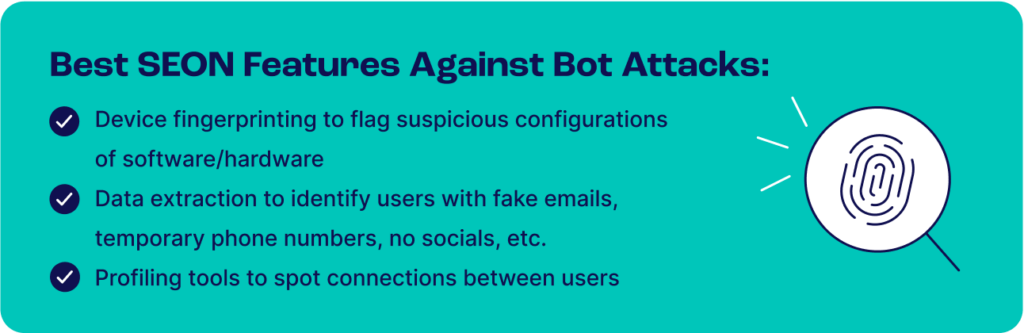
By combining multiple tools such as powerful velocity checks, unique digital footprinting from 90+ online sources, device fingerprinting, and many other insights, SEON allows you to detect bots and block their attacks from damaging your business.
Importantly, SEON provides detailed reporting and modular APIs, and allows you to fine-tune and adjust your bot prevention and other fraud detection strategy based on your own needs and risk appetites.
FAQs
Common signs include sudden or unexplained traffic spikes, repeated failed login attempts, activity originating from unusual geographic locations and interactions that occur at inhuman speeds. When these patterns appear consistently, they often indicate automated behavior rather than real users.
Bots are detected by analyzing behavioral patterns, device and network signals, action velocity and anomalies in real time. By correlating multiple data points instead of relying on a single indicator, businesses can more accurately distinguish between genuine users and automated threats.
You might also be interested in reading about:
- SEON: Bot Detection: How to Detect Bots
- SEON: Credential Stuffing: Prevention & Best Practices for Defense
Sources
- Imperva: 2025 Bad Bot Report
- Cloudflare: What is credential stuffing?
- Finadium: Financial services tops list for “bad bot” attacks