What Is a Botnet?
A botnet is a group of internet-connected devices that have had malicious programs installed on them – bots – that allow them to be controlled by a third party in unison. These are normally controlled without their legitimate owner’s knowledge, and they are often used to inflict harm as part of various malicious schemes.
The term botnet is a portmanteau – as it comes from merging the words robot and network. It’s an apt term, as it refers to a large mass of essentially mindless machines being controlled by a single, central entity at the top of the network. It’s an army of zombie devices following their leader’s commands.
One botnet can consist of tens of thousands, or even millions, of PCs, laptops, tablets, smartphones, and other devices. Cybercriminals use them to carry out various fraudulent activities, such as email spamming, click fraud, data theft, and distributed denial of service (DDoS) attacks.
Why Are Botnets Used?
A botnet is a way for cybercrime to scale. It allows a single individual or a small group to conduct an attack that would have otherwise required hundreds, or thousands, of individual criminals. Moreover, while most security infrastructures can handle a single malicious user, when a thousand devices show up in place of one, security protocols can bend or even break.
Botnets are controlled by cybercriminals using command and control software that allows them to execute orders throughout the distributed network from a top-down perspective.
These “herders” can exploit vulnerabilities in people’s computers, such as outdated or non-existent internet security software, to deploy malware that “recruits” devices to a botnet army. Not that the computer gets a chance to turn down this recruitment. The malware they use can spread incredibly fast, providing the herder with a powerful and rapidly expanding network of machines to use for their nefarious purposes.
Typically, these bots reach their target computer through quietly-installed malware from a compromised website or file. The botnet can lay dormant for months, or even years. Once the time is right, collectively to perform a range of tasks but is most commonly used to aid cybercrime. Owners of devices in a botnet are typically unaware that their devices are infected and enslaved.
How Do Botnets Work?
There are two distinct stages to the creation of a botnet: infecting/enlisting bot devices and deploying them. Let’s take a look at these in more detail:
- A herder makes a botnet work by infecting as many devices as possible with malware. Devices can be infected through tactics like phishing emails, software and website vulnerabilities and trojan horses.
- Once the malware is in place on a device, the herder will be able to control it via a CMS.
- Once in control of a botnet that might include dozens to thousands of machines, the herder can carry out coordinated strategies to exploit weak points in a system.
By creating a zombie botnet, the herder gains the ability to undertake a range of large-scale attacks, controlling the extensive network through their command server.
What Is a Botnet Attack?
Coordinated tactics by bots to attack security infrastructure or inflict other harm are called botnet attacks. Botnets are used for a range of malicious purposes. Because the botnet herder can perform admin-level tasks within the user’s operating system, they have the ability to:
- launch brute force attacks – for example, trying many permutations of a password until the right one is found, to try to gain unauthorized access to systems
- commit ad or affiliate fraud by sending bots to click on ads, either boosting numbers artificially or reaping PPC fees without actually directing any traffic to the host
- send mass spam emails from compromised email addresses
- perform crypto mining, using the processing power of enslaved computers to perform this resource-intensive task
- distribute additional malware via fraudulent emails or other phishing attacks.
- launch botnet DDoS attacks, essentially breaking a website by flooding it with unexpected traffic
Why Are Botnets So Hard to Stop?
Botnets are hard to stop because of their sheer size, the relative ease with which they are created and expanded, the huge number of always-connected devices out there, and many systems’ difficulty in protecting against an onslaught of attackers, rather than a handful of them.
Figures from the AV-Test Institute show that it registers more than 350,000 new pieces of malware and potentially unwanted applications every single day, many of which are expected to contribute to the creation of botnets. Malware accounts for around 90% of those registrations. The cybersecurity specialists at Spamhaus, meanwhile, report that botnet traffic rose by 23% during Q4 2021, compared to Q3.
Such a huge volume of malware means that it is impossible to keep every machine safe all the time, even with a vigilant approach to IT security. And many private individuals are, unfortunately, less than vigilant when it comes to keeping their antimalware security up to date and patching vulnerabilities promptly.
This fast-moving arms race means there are always new opportunities for those who control botnets to grow their networks.
Explore how SEON uses real-time signals, device intelligence, and behavioral analysis to identify automated traffic and reduce bot-driven fraud.
Learn more
Types of Botnets
Within the general definition of a botnet, a distributed network of compromised machines controlled by a single entity, different varieties or classes of botnets exist to serve different purposes with slightly different methods. Based on how they are controlled, these are:
The Client-Server Botnet
The client-server model is where the botnet command is handled through a single server. The herder’s commands go through this server to control the entire network.
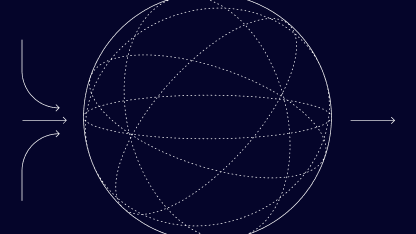
P2P Botnet
The peer-to-peer model is a decentralized way of operating a botnet. Instead of connecting with a commanding server, the bots distribute information and commands with each other. Essentially, each bot in the network acts as its own server, by comparison to the client-server botnet.
In a P2P botnet, each bot waits for commands to be published by the herder, either actively scanning the designated publishing domain for any commands to pull, or else passively waiting for commands to be pushed to the botnet. This is a more modern approach to creating a botnet, which removes the vulnerability of having the command server as a single point for failure for the botnet.
Because a P2P botnet is decentralized, it is even harder to take down than a client-server type of botnet.
The Compliant/Controlled Botnet
This is a client-server botnet where the malware has infected a central server, now hijacked and receiving commands, which it then distributes.
Also note that some botnets can be combinations of the above classes.
3 Examples of Botnet Attacks
Botnet attacks can be hugely disruptive and damaging, as these three examples demonstrate.
1. The ZeuS Botnet Attack
The ZeuS botnet emerged in 2007 and remains in operation to this day. It has infected over 13 million computers in more than 196 countries so far, using them to carry out online bank fraud around the world. The financial impact of this banking trojan exceeds $120 million.
2. The Mariposa Botnet Attack
There have been two major Mariposa botnet outbreaks to date, infecting 12 million and 11 million machines respectively. This trojan/worm emerged in 2009 and spread to 190 countries by 2011. It was used for a range of online scams, as well as DDoS attacks and the theft of user credentials from zombie machines for sale on the dark web.
3. The Mirai Botnet Attack
The Mirai botnet is IoT-focused and has infected at least 560,000 Internet of Things devices since it first popped up in 2016. Mirai and its clones and spin-offs are used to mount DDoS attacks, including the famous attack that knocked out the domain name provider Dyn and effectively broke the internet for a short time back in October 2016.
How to Stay Safe from Botnets
All types of online devices can be compromised into a botnet, both belonging to private individuals and businesses and organizations. If you’re worried that botnet malware may have infected your internet-connected device, it’s time to check the following.
Legacy cybersecurity companies provide ways to scan for botlike malware either for free or with their antivirus/antimalware software. If you are indeed infected, then you’ll need to know how to get rid of botnet malware from your device. The process for this will vary depending on your device, operating system and the type of malware.
How to Stop a Botnet Attack
If you’re a business that’s worried about botnets and bot attacks, be sure to keep up to speed with how to detect bots and what the latest botnet threats are. You will normally rely on a combination of defenses in place to prevent such elaborate and large-volume attacks against your operations.
Bot detection and mitigation software solutions will shore up your defenses against the threat of botnet attacks but so will most sophisticated risk mitigation, fraud prevention, cybersecurity and firewall software and tools, all deployed as part of a risk stack that corresponds to your particular needs.
In terms of staying safe from botnets, it is essential to keep your operating system and risk prevention software up-to-date on your device, including any and all software patches. That being said, keeping educated on the present and common threats combined with a healthy dose of digital skepticism are as good a part of your botnet defense as making sure your virus definitions are updated.