Fraudsters no longer need to steal an existing account to cause damage. They fake the device, spoof the location, spin up a bot farm and walk straight through controls built for a different era. Passwords and static IP checks were never designed to stop this. Device intelligence was.
What is Device Intelligence?
Device intelligence is the analysis of device-level data to assess the risk behind every digital interaction. It goes beyond knowing which device is connecting, it evaluates how that device is behaving, what environment it is operating in, and whether that combination is consistent with a genuine user.
When someone signs up, logs in, makes a payment or requests a withdrawal, their device quietly generates hundreds of signals: operating system, browser version, screen resolution, location, network type and more. Device intelligence captures these in real time, combines them into a risk profile and scores the session before a fraudster can cause damage.
Done well, it is invisible to genuine users and devastating to fraudsters.
Device Intelligence Vs. Device Fingerprinting
Device intelligence and device fingerprinting are integral components in the ongoing battle against online deception and fraudulent activities. Device fingerprinting is the process of generating unique identifiers for individual devices based on various attributes and configurations. These identifiers serve as a means of distinguishing one device from another within a network or ecosystem.
On the other hand, device intelligence expands beyond mere identification to encompass a comprehensive analysis that examines user behaviors, usage patterns and device interactions to gain deeper insights and understand risk profiles. While device fingerprinting creates identifiers for devices, device intelligence utilizes these identifiers and other data sources to identify standard device setups to fraudsters’ tool stacks and facilitate better anti-fraud decision-making.
How Does Device Intelligence Work
When a user accesses a platform, whether an ecommerce retailer, social media or online banking service, their device shares hundreds of passive signals with your servers to function. Device intelligence captures those signals and processes them in three steps.
1. Signal collection
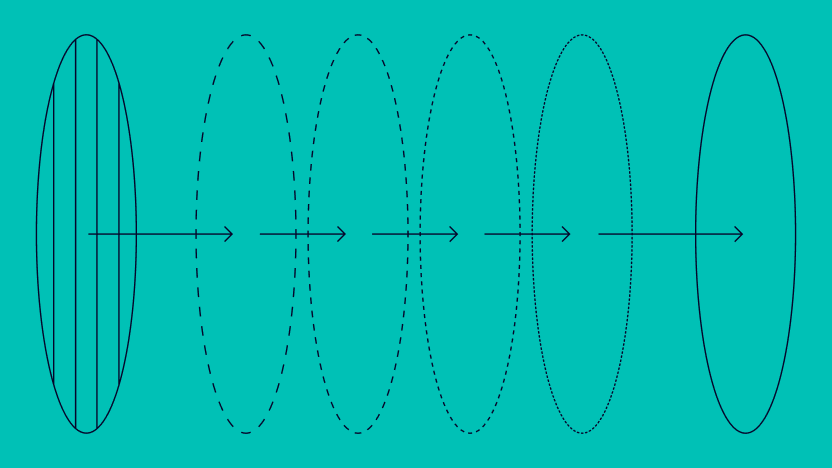
As a session begins, hardware and software configuration, network type, location signals and interaction patterns are gathered from the device. These combine into a stable device identifier that recognises a returning device even after resets or session changes.
2. Behavioral and environmental analysis
Device intelligence analyzes not just what the device is but how it is being used. Is the interaction pattern consistent with a real user? Is this a genuine phone or an emulator? Is the session being remotely accessed or screen-shared? Behavioral signals surface risks that hardware checks alone would miss.
Risk scoring and decisioning
The collected signals feed into a real-time risk score. Low-risk sessions pass through without friction. Higher-risk sessions trigger step-up authentication, restricted functionality or a block before damage is done. The decision is tied to the specific signals that triggered it so analysts can understand and act on it quickly.
Where Device Intelligence Makes the Biggest Difference
Device intelligence applies across the entire customer journey. Here are the five fraud types where it has the most direct impact.
- Bonus and promo abuse Device intelligence identifies legitimate customers versus abusers by analyzing cookie and device-sharing patterns and detecting attempts to manipulate data using privacy tools.
- Multi-accounting By tracking device and browser IDs across accounts, device intelligence flags multiple accounts operated from the same device and protects the integrity of your user base.
- Account takeover Device intelligence identifies unfamiliar devices, suspicious emulators and virtual machines attempting to log in, and detects real-time signals like remote access, screen sharing and on-call status during sensitive account changes.
- Chargeback and friendly fraud By recording a customer’s typical device, browser, IP and transaction behavior, device intelligence provides concrete evidence to challenge fraudulent chargeback claims.
- Bot attacks Device intelligence analyzes browser configurations, window sizes and screen resolutions while identifying emulators, virtual machines and proxies to detect and block automated attacks.
Enhanced Fraud Prevention Capabilities
Modern fraud detection software tools can now discern if someone is remotely accessing a customer’s device, such as through screen sharing on mobile and web apps. These systems can further identify apps capable of interfering with or altering other applications on Android platforms. Another crucial aspect is on-call monitoring, particularly relevant for iOS and Android users, where the system can determine the call status of a customer. This feature is invaluable in detecting phishing scams, especially in the financial service industry. Understanding the type of carrier, whether it’s a primary provider like AT&T, T-Mobile or Verizon versus a VoIP service, aids in distinguishing legitimate user activity from fraudulent attempts.
Additionally, residential proxy detection plays a vital role in verifying user locations and identifying suspicious attempts to access restricted services or manipulate IP addresses. These advanced capabilities collectively enhance fraud detection measures, ensuring heightened security and protection against evolving threats.
Device Intelligence and Network Analysis: Seeing the Bigger Picture
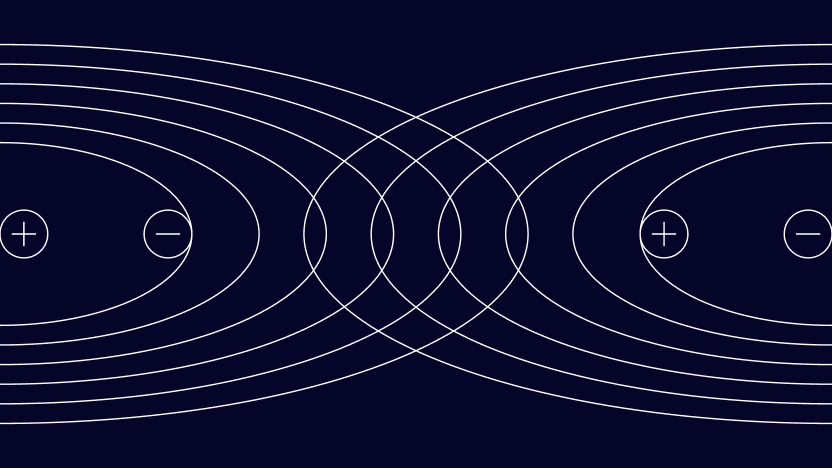
Device intelligence tells you what is happening on a single device. Network analysis tells you what is happening across all of them.
When the same device hash appears behind 30 different accounts or the same IP subnet shows up across a wave of new registrations, the risk is not in any one session — it is in the pattern. Network analysis connects those dots automatically, grouping accounts by shared signals and surfacing coordinated fraud rings that individual device checks would never catch.
Together, device intelligence and network analysis move fraud detection from reactive to proactive. Device signals feed into network grouping and network patterns feed back into stronger device rules — a continuous loop that gets sharper over time.
Future-Proofing Fraud Prevention
Operating with real-time, unparalleled information, device intelligence reaches beyond traditional methods like multi-factor authentication or security questions. By connecting the dots through a vast array of data points, ranging from geolocation and IP information to more nuanced behavioral device data like battery life, phone orientation and font count, device intelligence offers a comprehensive view of a user and relevant user interactions.
Through scrutinizing thousands of device signals, it can swiftly identify deviations from typical user patterns. Whether detecting sudden changes in geolocation, unusual IP addresses, or discrepancies in device configurations, device intelligence is a vigilant guardian against fraudulent attempts, serving as a dynamic and proactive defense mechanism in the fight against online fraud.
Use device intelligence for a proactive defense against the most sophisticated fraud schemes.
Speak with an Expert
FAQ About Device Intelligence
Device intelligence works as one layer in a broader fraud stack. At SEON, device signals combine with digital footprint data including email, phone and IP signals into a single risk score. This means a clean device paired with a suspicious digital footprint is still correctly identified as elevated risk.
Yes. As fraudsters use AI to generate synthetic identities and scale attacks, device intelligence counters by analyzing the technical environment behind every session. AI-generated identities still need a real device to operate from, and that device leaves signals that behavioral and environmental analysis can detect.
Yes. While fraud prevention is the primary use case, device intelligence also supports AML compliance by enriching transaction monitoring with device context, reduces friction in onboarding by fast-tracking low-risk devices and strengthens chargeback dispute evidence.
Yes. Device intelligence collects technical signals from devices including hardware configuration, software environment and network behavior, without processing personal data. This makes it compatible with GDPR and other major privacy frameworks.