Telecommunications fraud includes scams and attacks that exploit telecom networks, billing systems, or customer identities for profit.
In this guide, we break down 11 common telecom fraud types and how to detect and prevent them.
What Is Telecommunications Fraud?
Telecommunications fraud, also known as telco fraud or telecom fraud, includes any kind of activity designed to abuse and gain an advantage over telecommunications companies using deception (fraudulent practices).
This includes IRSF fraud (International Revenue Sharing Fraud), where fraudsters abuse premium phone rates, and interconnect bypass fraud, a form of arbitrage between operators’ call rates.
How Does Telecommunications Fraud Work?
Because telephony is the largest and oldest deployed network in the world, fraudsters have long developed tools and practices to exploit it to extract value. Revenues in 2023 are estimated at $498 billion – and it is still growing, at an expected rate of 2.08% year-on-year.
And while fraud attacks usually evolve quickly over time as companies squash them, telco fraud is unique as it’s often taken as a given. Its costs are absorbed by operators, who would rather not embark on integrating complex risk management systems into their architectures.
Adding to the challenge is the fact that telecom companies also break down their services to resell them to local networks and carriers – a £4/$5 billion industry in the UK alone.
As the technology to run your own mobile network becomes more widely available, large telecom operators are becoming targets of fraud indirectly, making it harder to identify.
11 Types of Telecommunications Fraud
Let’s now look at the most common types of telecom fraud attacks operators should know about.

1. International Revenue Sharing Fraud (IRSF)
International Revenue Sharing Fraud, or IRSF fraud, takes advantage of premium phone rates, which are then dialed unwittingly by users.
It is by far the biggest fraud challenge for telecom operators, costing the industry an estimated $4 to $7 billion a year according to Verdict. This is how it works:
- Bad agents sign up to lease a premium phone number.
- They break into a business’s phone systems and make calls to that number.
- The business pays as much as $1 a minute, 25% of which goes into the fraudster’s pockets.
Businesses may suddenly find themselves with astronomical phone bills for calls they do not recognize. The calls often happen outside of working hours and companies only realize they’ve been made when it’s time to foot the bill.
It doesn’t help that regulation is lacking in this area. Unlike with card payments, where the chargeback process can protect the person whose credit card was stolen, there is no such thing in the telephony world.
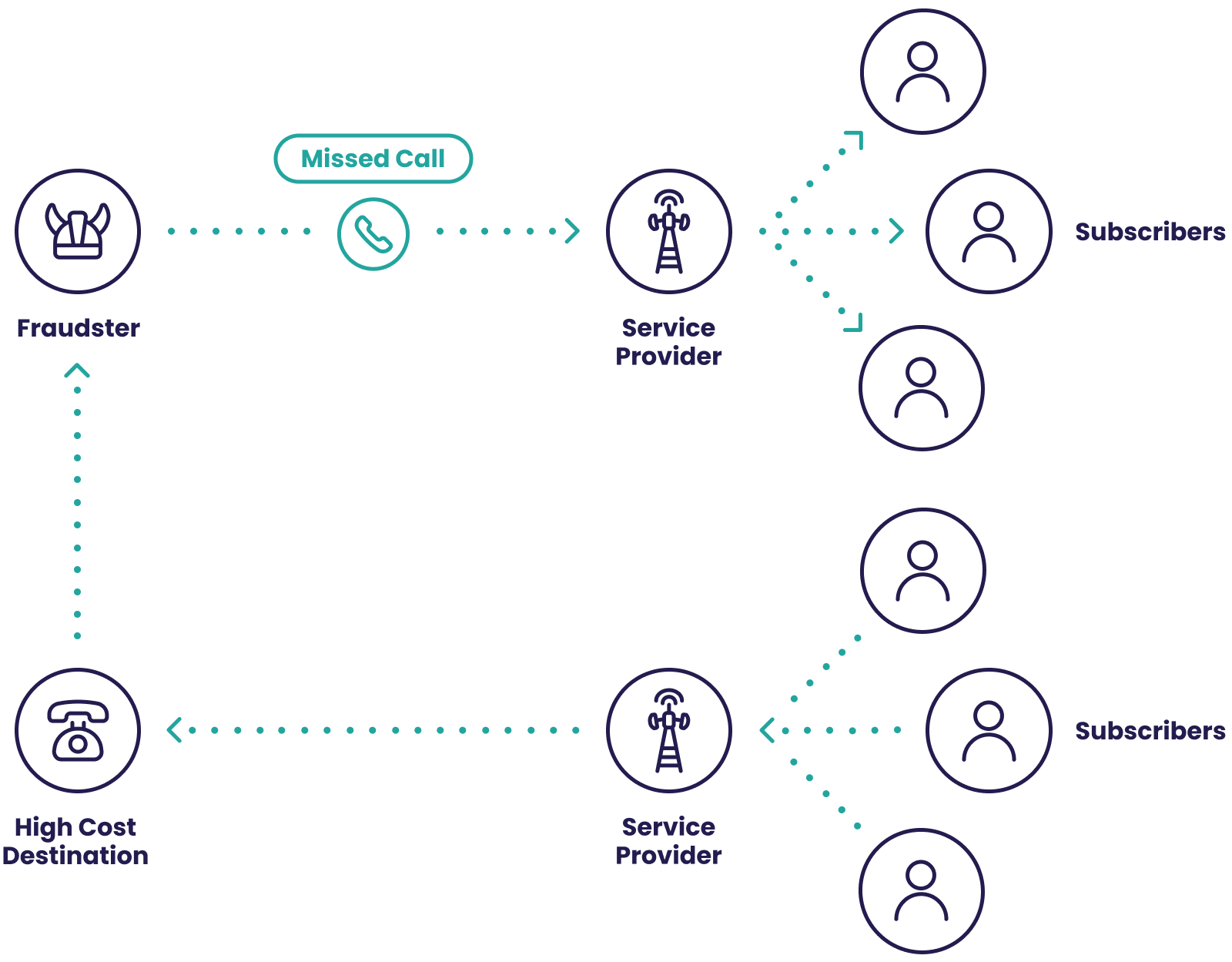
2. Wangiri Fraud
Wangiri fraud (from the Japanese for “one ring and cut”) is a telecom scam where fraudsters call a customer, let it ring once, then hang up. The goal is to trigger a callback, which routes the victim to a high-cost premium-rate number controlled by the attacker. An SMS version also exists, prompting users to call or text a specific number.
Common red flags include sudden spikes in calls to high-cost destinations and repeated short-duration calls. Telecom operators and call-heavy businesses can reduce risk by monitoring outbound dialing patterns and using tools like reverse phone lookup to flag suspicious numbers before customers are prompted to call back.
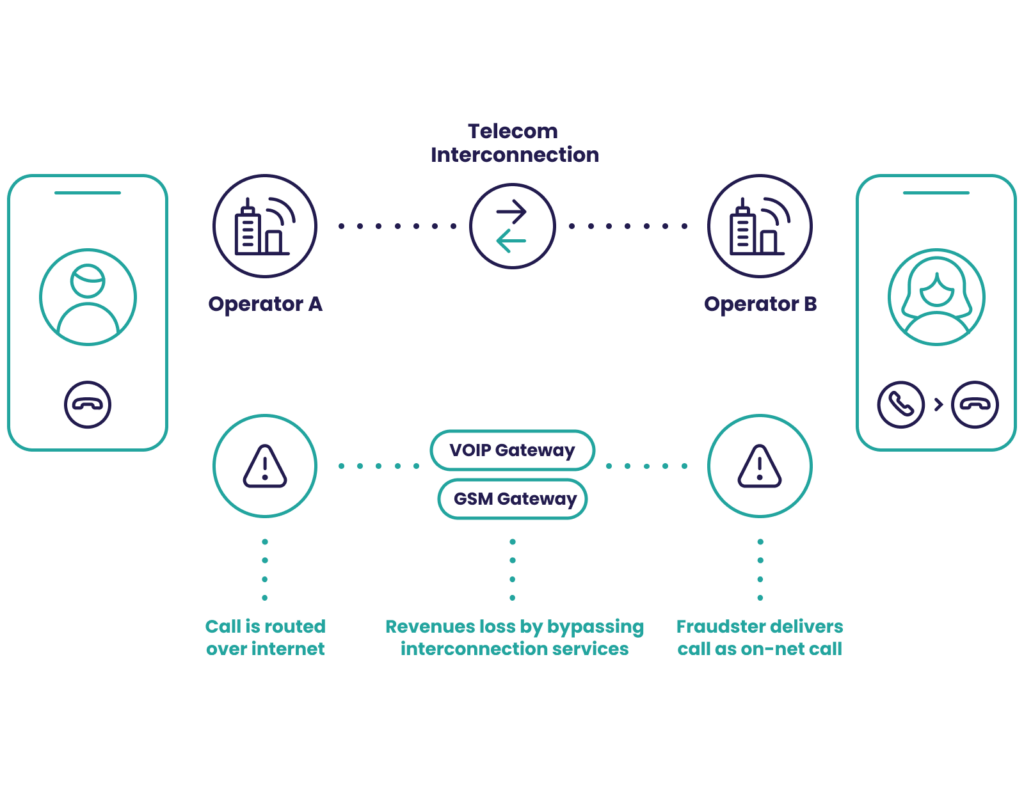
3. Interconnect Bypass Fraud
Interconnect bypass fraud, also known as SIM box fraud, takes advantage of something called a termination rate to make cheaper phone calls. It is estimated by CFCA to cost telecom operators $3.11 billion in lost revenue per year.
To understand it, let’s look at a scenario with two operators in different countries:
- A customer of Operator A calls a customer of Operator B.
- Operator A charges its customer a fee per minute.
- Operator B charges Operator A a fee for providing the call to its customer.
That last charge, where the call terminates, is the termination rate. These rates vary wildly depending on the contracts between the two operators. Some of them are expensive, others are close to 0.
This is where a fraudulent operator comes into the picture. They reroute these international calls using a SIM box or GSM gateway, effectively hijacking the connection to achieve cheaper termination rates. They are essentially making long-distance calls much cheaper, but the caller pays the same price – so the fraudster telco pockets the difference.
This also impacts telecom customer satisfaction because more often than not, the quality of these calls will be inferior to standard international calls.
4 Telecom Arbitrage Fraud
Arbitrage is the general practice of capitalizing on price differences. In the telco world, these differences appear in the long-distance rates between countries.
Just like with international bypass fraud, it can lower the international cost for customers, but also open the door to fraudulent companies who insert themselves between operators. They claim to connect directly from country A to B, whereas, in fact, they go through a cheaper rate country to connect the call.
5. PBX Hacking
PBX hacking allows fraudsters to take control of phone lines by exploiting unsecured phone networks.
A PBX (private branch exchange) is a private phone network that connects to external networks. It’s what allows companies to share lines and to reduce the number of numbers needed in an office, for instance.
Because a lot of these PBX are IP-based, they can be an easy target for hackers. They will log into the system and use it to their advantage – for instance for instances of IRSF fraud mentioned above. This is a cybersecurity and IT issue that can be avoided with better internal controls and password security.
6. Traffic Pumping
Traffic pumping, also known as access stimulation, is a practice where unscrupulous local exchanges cook the numbers of calls to their networks to benefit from compensation fees set up by the US FCC.
Under the Telecommunications Act of 1996, big telcos such as Sprint, Verizon, and AT&T have to pay fees to rural carriers – so these carriers do everything in their power to boost the number of calls to get larger payouts.
7. Deposit Fraud
Deposit fraud is a form of credit card fraud where criminals use stolen card details to buy prepaid SIMs or devices from telecom online stores. The impact often shows up later as chargebacks, and aggressive chargeback protection can increase false positives by blocking legitimate buyers.
A growing risk comes from 5G proxy networks, where fraudsters buy SIMs and USB dongles in bulk to build residential proxy setups and rotate IPs at scale. Using IP intelligence, including an IP fraud score, can help flag suspicious locations and network patterns before a purchase is approved.
8. Subscription Fraud
Subscription fraud in the telephony world sees criminals sign up for contracts using stolen IDs and stolen credit card numbers.
Phone contracts are harder for fraudsters to purchase than items because they involve a form of KYC verification. That is to say, you need to verify the user’s identity before they can subscribe.
Fraudsters love high-end smartphones they can acquire through contracts. It’s a simple case of submitting fake IDs, jailbreaking the device, and reselling it on second-hand markets. By the time the repo company comes, it realizes the person does not exist.
So how do they pass the KYC checks? That’s barely an inconvenience for identity fraud experts. They have a large pool of stolen identities to choose from, acquired via phishing techniques, bought on the dark web, or rented out from ID mules.
It should be noted that in-store purchases tend to have a higher risk rate than shipping. While fraudsters have plenty of options for acquiring drop addresses (where they receive items not tied to their real identities), it’s much easier for them to walk in and pick up the devices in person.
9. Account Takeover
Telecom companies that offer online customer accounts are frequent targets of account takeover (ATO) fraud. In these cases, fraudsters gain access to user accounts using stolen or compromised login credentials, allowing them to make unauthorized changes, access sensitive data, or carry out fraudulent transactions.
Account takeovers are costly and damaging. Beyond direct financial losses, ATO incidents erode customer trust and can expose telecom operators to regulatory and reputational risk. Telecom accounts are especially valuable to attackers because control over a phone number or SIM can enable password resets, intercept one-time passwords (OTPs), and facilitate further fraud across banking, fintech, and digital services.
Telecom account takeovers are often enabled by compromised credentials or SIM-related attacks, which is why many operators use dedicated account takeover detection tools to monitor login behavior and stop unauthorized access in real time.
To reduce ATO risk, telecom operators typically rely on layered controls such as strong authentication, behavioral monitoring, and real-time detection of suspicious login activity, helping ensure only legitimate users can access and modify their accounts.
Rebtel Blocks 30% More ATO Attempts
“What’s really cool is the way you can set up rules. There’s a whole bunch of logic that we’ve started playing with”
10. Smishing/SMS Phishing
Smishing, also known as SMS phishing, is the practice of sending mass SMS in order to obtain personal information from the person who receives the messages.
Mass spam campaigns are the bane of customers’ and telcos’ existence. This is why SMS phishing rings have become adept at avoiding detection. They’ve been known to use software to confirm the numbers they target are mobiles and not landlines (so telcos don’t notice red flags), create auto-shops to resell the stolen details, and even provide their own hosting services to host phishing sites and marketplaces.
The volume of social engineering attacks that take the form of smishing skyrocketed by more than 328% in 2020 and while telco operators don’t always take the fall for it, they should feel uncomfortable knowing that they are accidentally complicit in the practice (and it potentially affects their reputation, too). It is concerning that according to ProofPoint data from 2022, year-on-year awareness of smishing dropped to 23%.
A simple system for monitoring signups and transactions coming from the B2B service should be enough to ensure your telco company isn’t helping a smishing business.
11. SIM Jacking and SIM Swapping
Also known as SIM swapping, SIM jacking sees fraudsters take control of a person’s SMS messages and phone calls by switching a phone number to another they are in control of.
As more and more companies, such as banks, use OTP (one-time passwords) and 2FA (2-factor verification) delivered in the format of text messages or phone calls, fraudsters are attempting to take control of people’s phone numbers in order to intercept them.
The fraudster will contact the telco’s customer service and ask to transfer their number to a new SIM, which they control. When the procedure is complete, they can receive all the OTPs and SMS verifications needed to hijack customer accounts, from social media to fintech apps.
Telco operators have become much better at mitigating this kind of risk in the last few years, simply by deploying their own multi-factor authentication (MFA) systems to confirm if the user legitimately requested a number change.
Telecommunications Fraud Detection and Prevention
Telecommunications fraud detection and prevention encompasses a wide array of strategies and tTelecommunications fraud detection and prevention includes the strategies telecom operators use to identify suspicious activity, stop losses, and protect customer trust. Because attacks can scale quickly, effective prevention depends on real-time detection and fast response.
A strong telecom fraud prevention program typically combines:
- Real-time monitoring: Spot unusual call patterns, traffic spikes, and suspicious behavior early so teams can intervene quickly.
- Network controls: Use routing and blocking rules to limit exposure to known high-risk destinations and fraudulent traffic.
- Identity and account protection: Verify customers and stop abuse at signup and login using signals like digital footprinting, device intelligence, and risk-based authentication.
In practice, prevention comes down to three focus areas:
- Vetting resellers and partners: Reduce exposure to bad actors in your supply chain.
- Protecting revenue: Detect and block fraud before it becomes billable loss.
- Authenticating users: Confirm customers are real and prevent account-based abuse like ATO and SIM-related fraud.
SEON supports telecom fraud prevention by enriching onboarding and account activity with real-time digital identity and device signals, helping teams identify risky behavior earlier and reduce unnecessary manual reviews.
New and Evolving Telecommunications Fraud Techniques
Telecom fraud is continually evolving, with recent trends highlighting a rise in sophisticated attack vectors:
- Virtual SIM Cards (eSIMs): Despite their enhanced security features, such as being difficult to clone, eSIMs are still vulnerable to malware and social engineering attacks.
- Social Engineering Attacks: The pandemic has escalated the frequency and sophistication of phishing attacks, including SMS and call-based phishing, utilizing advanced techniques like deepfake technology and targeting specific individuals through CEO fraud and spear-phishing.
- Combined Attacks: Notable incidents of SIM swapping have been linked to groups like “Scattered Spider,” who have impersonated telecom staff to access systems and execute SIM swaps for financial gain.
- AI-Enabled Telecom Fraud: With AI and machine learning increasingly used in fraud prevention, fraudsters are also leveraging these technologies to refine their tactics, such as creating more convincing smishing messages.
- Fake and Synthetic IDs: Fraudsters are exploiting advanced methods to obtain ID documents, either through phishing or services that rent out IDs. Detecting synthetic ID fraud is becoming increasingly complex as these IDs often contain legitimate elements.
These trends underscore the dynamic nature of telecom fraud and the need for continuous advancements in fraud detection and prevention strategies.
Solutions for Telecommunications Fraud
Telecom fraudsters are skilled at hiding their identity. They use stolen IDs, compromised payment details, and evasive tactics to blend in, whether they’re targeting an online telecom store, customer accounts, or reseller workflows.
To reduce telecom fraud without adding unnecessary friction, operators need tools that enrich customer and session data in real time, flag high-risk behavior early, and support fast, consistent decisions.
SEON helps by combining digital identity signals, device intelligence, and automated risk rules to detect threats earlier and reduce manual review effort. The result is smoother operations and fewer cases of account takeover, transaction fraud, and identity abuse.
Telecommunications Fraud FAQ
The most costly fraud attacks for telecommunication companies include IRSF (international revenue share fraud), bypass fraud, and traffic pumping.
Fraudulent attacks such as account takeover, transaction fraud, and subscription fraud targeting telecommunications operators can be detected with real-time monitoring, digital footprinting and data enrichment. This allows companies to learn more about users in order to accept or decline their actions, such as a payment or login.
Sources used for this article:
- IBISWorld: Telecommunications Resellers in the UK – Market Research Report
- ZDNet: Phone fraudsters are stealing billions each year through a scheme known as IRSF
- Infosys BPM Podcast: Emerging Telecom Fraud Trends
- Dark Reading: Cybercriminals Target Telecom Provider Networks
- Statista: Telephony Worldwide
- Verdict: Telecom Fraud – the battle continues