The EU’s SCA requirements can be worrying for businesses.
The European Union created the PSD2 regulation, to further promote positive competition and innovation within the payments industry as well as further secure transactions.
We’ll go over what your risk management team should keep an eye on, how the different elements work including 3DS2 and how SEON can support you in ensuring compliance.
The Second Payment Services Directive
The latest directive from the European Union. This Second Payment Service Directive forces banks to share their collected user data. If you, as a customer, authorize data sharing, third-party services can use it for a variety of services and financial products.
The directive also pushes for Payment Initiation Services (PIS). These online services can access a user’s payment account to initiate payment directly, as long as authentication is checked and consent is given.
What Is SCA in Relation to PSD2?
Short for strong customer authentication, SCA is a requirement under the European Union’s PSD2 that seeks to improve the security of online payments by ensuring the cardholder identifies themselves by at least two types of authentication.
In simple terms, this means that when the customer wants to buy something online, they will be asked by the issuer bank for more information: Not just to input their card number (something they own) but to type an additional PIN or password (something they know), fingerprint (something they are) or even an additional one-time password from an authentication application or sent to their mobile device (something they own). Thus, in total, there will be two factors that authenticate their identity.
However, SCA is not always needed per PSD2. Where the customer is known and has identified themselves in other manners – e.g. by logging into a verified account using a password – SCA measures such as 3-D Secure can be circumvented without compliance concerns. This reduces some friction and encourages customers to form closer ties with certain businesses they return to often.
Partner with SEON and stay compliant to the Payment Services Directive 2 (PSD2). Learn more today with SEON.
Ask an Expert
What Does PSD2 Say About SCA?
“Payment service providers shall have transaction monitoring mechanisms in place that enable them to detect unauthorised or fraudulent payment transactions.”
All online payments made by customers in the EU need to be secured through the appropriate technology. In PSD2, it is referred to as strong customer authentication (SCA).
Article 2(1) of the PSD2 clearly stipulates that: “payment service providers shall have transaction monitoring mechanisms in place that enable them to detect unauthorized or fraudulent payment transactions”.
The minimum requirements for payment transaction analysis are further explained in Article 2(2). These include:
- Checks against lists with compromised or stolen authentication elements
- Checks against known fraud scenarios
- Detection of malware infection of the authentication device
- Deviations in the amount of the transaction
- Analysis of the device/software, when provided by the PSP
What Is the Goal of PSD2 SCA?
Financial products and services vary greatly across Europe, both in quality and price. The EU’s PSD2 directive aims to reduce domestic frameworks and harmonize local regulations. This helps third party financial services scale across the continent, fosters international ecommerce, and attracts new ventures wishing to tap into a larger, unified market.
PSD2 SCA in particular aims to build trust among consumers when it comes to paying with their cards online, over the phone and in person – as well as, of course, to protect cardholders and banks from data breaches, counterfeiting, and other cyber threats.
The PSD2 also simplifies the current payment chain. PIS cut down on middlemen by potentially removing bank card companies, acquirers and payment gateways, allowing banks to deal directly with merchants. It will significantly reduce transaction costs.
We should mention that the EU is currently in the process of creating the new version of PSD2, dubbed PSD3, following consultations in the summer of 2022. PSD3 will look to expand on PSD2, bringing it up to date and taking additional considerations into account.
There is no known implementation timeline at the time of writing, although it is going to be a lengthy process. Ultimately, PSD3 is not likely to be fully enforced before 2026.
How to Authenticate a Payment with SCA
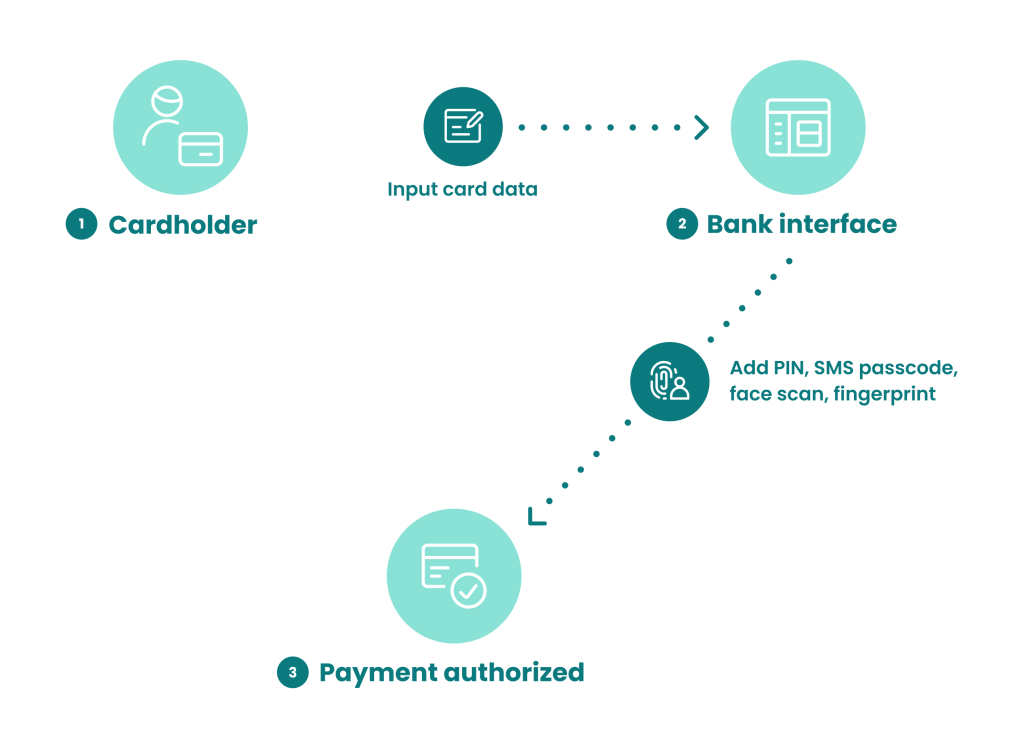
To pass through strong customer authentication (SCA), a shopper will have to provide more than their card or card number. This normally takes the form of these steps when the payment is online:
- At checkout, the shopper enters their card details, inclusive of the CVV number and card expiry date.
- A prompt pops up connecting them directly to their card issuing bank. The prompt asks them for one or more of the following:
- to enter a one-time password sent to them on their phone
- to provide a keyphrase they have defined at an earlier date. This serves the same purpose as a password.
- to look at their mobile selfie camera and blink
- to submit their fingerprint via fingerprint reader
- The submitted data is cross-referenced with the data on file for the person and, if it matches, the payment goes through.
Many in-person payments already involve two factors: Having the card as well as knowing its PIN. Contactless payments are often exempt. However, even for contactless low-value payments, a cardholder will be prompted to insert their card and input their PIN occasionally.
PSD2 Exemptions
In the respective legislation, the EU’s competent bodies have defined that certain types of transactions are PSD2 exempt. In general terms, they can occur when the risk is low, be it because of pre-established trust or low risk.
It is important to note that PSD2 exemptions we list below are not absolute and can be subject to limitations and conditions. They can also vary depending on the country.
PSD2 exemptions defined by the EU include:
- Transactions below a certain amount: Because they are considered to involve a low risk of fraud, transactions of particularly low value (typically less than €30) are exempt.
- Transactions between trusted parties: Whenever all parties involved in a transaction have demonstrated themselves to be trustworthy, as well as that they are who they say they are, this transaction can be exempt. For example, a returning customer to Amazon who has paid with the same card before may not need to complete the SCA step reserved for new customers or new payment cards.
- Repeat payments: Repeat payments are deemed to be similar to transactions between trusted parties and can thus be exempt.
- Transactions that only involve certain types of providers: When a transaction only involves PSPs, PISPs and AISPs – companies that provide payment services, payment initiation and account information services – then it is exempt from certain PSD2 requirements.
- One-leg transactions: When only one leg of the payment is within the EU area, it is considered low risk and is exempt. This can happen either when the payer or the payee is not in the EU.
- Corporate payments: Some corporate payments are exempt, including the payment of staff salaries, as they are between known parties. However, this varies per country and is best confirmed by a legal expert.
- Remote payments: Specific types of remote payments are also exempt. These include contactless payments.
- Deemed safe after transactional risk analysis (TRA): The EU also defines how TRA exemptions work, which are a category in themselves. They refer to transactions that may not belong to the above types of exemptions but have nevertheless been demonstrated to be safe by risk analysis. Normally, the merchant’s fraud rates have to be low. The exact percentage correlates to the amount of the payment, but there are no TRA exemptions for transactions over €500.
How Does 3-D Secure 2.0 Work With PSD2?
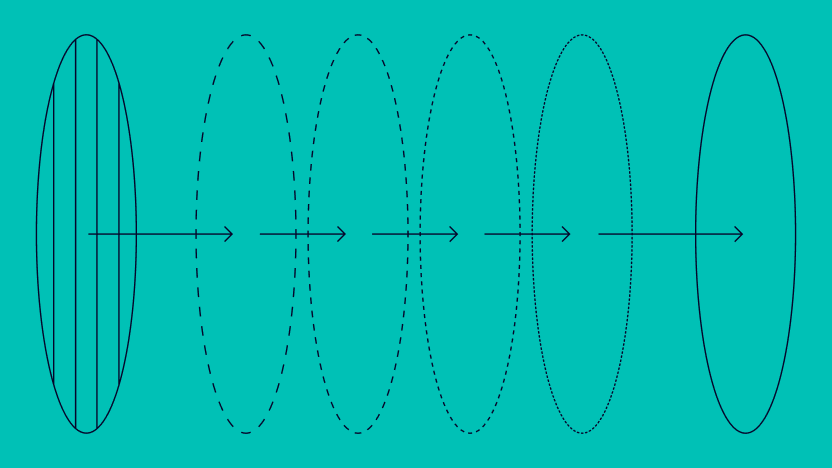
3-D Secure is the standard designed by EMVCo and major credit card schemes. 3-D Secure 1.0 usually required a static token (like a password) to complete a card payment, but 3-D Secure 2.0 increases the number of data point checks to improve payment security.
The previous version was notoriously clunky. US merchants reported decreased conversion rates of up to 45% because of the friction it creates for users. So yes, it might help reduce chargeback fraud, but also overall profits.
The 2.0 version will enable a more frictionless payment method by enabling dynamic 2FA which provides multiple data points from the merchant to the issuer. So these data points can reduce fraud for PSD2-based payments while meeting requirements.
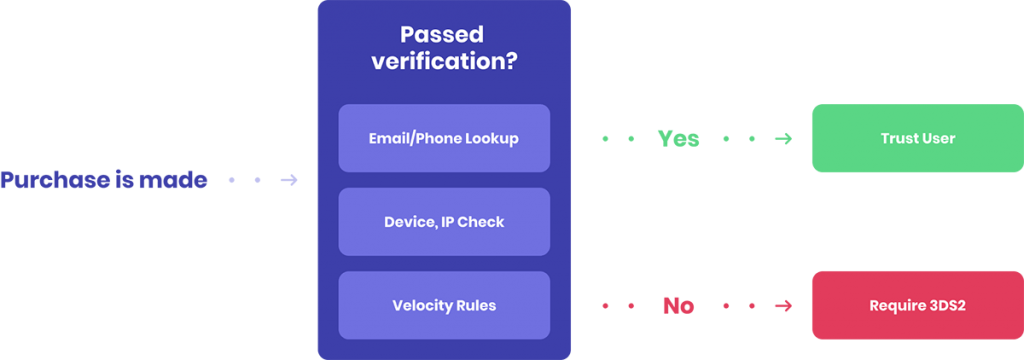
However, contrary to popular belief, 3-D Secure is not mandatory to pass the SCA requirements. Firstly, there are a number of exemptions (low-value or low-risk transactions, subscriptions, whitelisted merchants, etc..).
Secondly, the right fraud authentication tool can help you achieve the same – if not more – than 3-D Secure to meet PSD2 authentication standards without going into manual reviews.
Below is our breakdown of the SCA requirements, and how a risk management tool like SEON can meet them.
How SEON Can Help You Meet PSD2 SCA
SEON’s industry-agnostic, modular solutions can help merchants meet PSD2 SCA in various ways. Namely, by utilizing our software, you will be able to:
- Qualify for TRA exemptions: SEON’s platform can be easily set up to implement TRA exemptions along with their limits and categories, which depend on the sum spent.
- Reduce payment friction safely: SEON will conduct the transactional risk analysis for you and exempt provably good users from having to complete an SCA step.
- Increase customer loyalty: Provide friction-free experiences to your loyal, legitimate customers by marking them as exemptions to any risk rules you implement for SCA. This way they will not have to do SCA every time, and are more likely to be returning customers.
- Stop account takeovers: Using in-depth device fingerprinting, unique digital footprint analysis, velocity checks and real-time monitoring, SEON will flag or block suspicious logins that could result in account takeovers, to minimize the chance of a fraudster gaining access to a legitimate customer’s account.
- Flag common fraud scenarios: See a user’s fraud score and explanations of how exactly it is reached, make adjustments based on your risk tolerance and get machine learning suggestions on stopping fraud even more efficiently.
- Detect fraudster tools and software: SEON identifies methods and applications employed by fraudsters to evade your defenses, including spoofing tools, VPNs, Tor, proxies, specialty browsers and more.
Partner with SEON to reduce fraud with real-time data enrichment, clearbox machine learning, and advanced APIs – while staying compliant.
Ask an Expert
Conclusion – PSD2, SCA and Fraud Authentication
PSD2 is a strongly consumer-focused directive from the European Union. Everyone, on paper, should benefit from decreased transaction fees, reduced payment friction, and increased authentication security.
However, this security point may be challenging for Risk Ops teams in the same way the GDPR and fraud detection appear at odds with each other.
It might require you to train fraud managers, who might feel they have to jump through hoops to help remain their organizations compliant. Luckily, at SEON, we firmly believe implementing our series of fraud authentication tools can cover all those legal requirements, while future-proofing your business.
FAQ
Deadlines for PSD2 SCA for online merchants depend on their country. For example, in Spain, all transactions had to be SCA compliant by March 1, 2021, and in Belgium by May 18, 2021. In the UK, the country’s FCA extended the implementation deadline, which eventually passed on March 14, 2022.
These EU regulations specify that for all card-not-present payments that exceed a minimum of €30 should be authenticated using at least two factors. For instance, a factor can be a password or a fingerprint. This method of providing strong customer authentication is often known as 2FA or MFA.
Sources
- AI Editorial: Is 3-D Secure a Conversion Killer?