100 new users register in an hour. Same device. Different names. Each one claims a $10 welcome bonus and withdraws immediately. Your onboarding flow passed them all.
Similar scenarios play out regularly across crypto on-ramps, digital banks and lending apps. The fraud scheme is simple. The problem is that most onboarding checks are built to verify identity, not to detect coordination. Those are different problems, and they require different signals.
Key Takeaways
- Batch registration fraud exploits the speed-to-onboard gap: platforms that prioritize frictionless signup create the conditions fraudsters need.
- Device intelligence, IP history and email age are three of the most reliable pre-registration signals for identifying coordinated account creation.
- Velocity rules are the primary tool for catching batch attacks in real time.
- Explainable scoring lets risk teams calibrate thresholds without harming legitimate conversion rates.
What Fraudulent Account Registration Actually Looks Like
Fraudulent account registration is the use of fabricated or coordinated identities to create accounts at scale, typically to extract value before detection. The three most common patterns in fintech are batch registrations, synthetic identity fraud and bonus abuse.
- Batch registrations are the most visible. A single device (or a small cluster sharing hardware characteristics) generates dozens or hundreds of accounts in a short window. Each account uses different personal details, often generated or purchased, but the underlying device profile stays consistent.
- Synthetic identity fraud is slower and harder to catch at registration. Fraudsters combine real data points (a valid SSN, a real address, a phone number) with fabricated ones to create an identity that passes basic KYC. These accounts often age for weeks before being used. At the point of registration, the identity looks clean. The problem only surfaces once the account is used
- Bonus abuse overlaps with both. The goal is extraction, not account takeover. Register, claim the promotional reward, withdraw, abandon. The account lifecycle is measured in minutes.
All three follow the same logic: get in fast, extract value and leave before detection catches up.
Why Fintech Onboarding Is the Easiest Target
Onboarding in fintech is a conversion funnel. Every step that adds friction costs signups, and most platforms optimize relentlessly to reduce it. This exact pressure creates the conditions fraudsters exploit.
New platforms face an additional problem: the lack of a historical baseline. A fraud model trained on customer behavior needs data to calibrate against. A platform with six months of transaction history has very little. Fraudsters target new entrants specifically because the rule engines haven’t been tuned yet.
The lending vertical illustrates this well. Groups of applicants with no prior credit history onboard quickly, take out loans and disappear. The credit profiles look clean, but the behavioral pattern is anomalous: multiple applicants linked by shared IP addresses, applying within minutes of each other. Without historical data, there is no baseline to catch it before the funds are gone.
The same tension appears in any product that advances funds before settlement clears — buy now pay later, instant bank transfers, early wage access. The faster the disbursement, the shorter the window to catch fraud before the money is gone.
The standard onboarding checklist (email verified, phone confirmed, ID document matched) was designed to verify identity, not to assess risk. Those are different tasks, and platforms that treat them as equivalent leave a gap that fraudsters reliably find.
The Signals That Give Fraudsters Away
Fraudsters exploit those gaps precisely because the signals they leave behind fall outside standard onboarding checks. Understanding what those signals are is the first step to catching them.
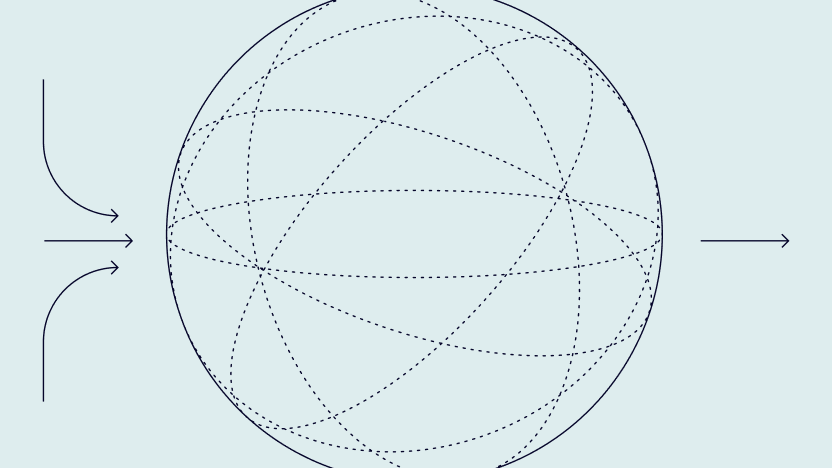
- Device intelligence is the first layer. Modern device fingerprinting uses more than 200 data points (including hardware characteristics, browser attributes and network configuration) to reliably identify a device, even when cookies are cleared, incognito mode is active or the app has been reinstalled. When the same device appears across 40 registrations in 90 minutes, the pattern is visible; where document verification sees 40 different people, device intelligence sees one.
- Email age and digital footprint are sharper signals than most onboarding flows account for. An email address created four minutes before signup has no associated digital presence: no social profiles, no forum activity, no platform registrations. This absence is informative. An email used across GitHub, LinkedIn and a decade of online activity presents a fundamentally different risk profile. Email risk assessment tools check hundreds of online platforms to surface that footprint difference in real time.
- IP history is where coordination becomes visible. A residential IP that has appeared in prior fraud cases, or a data center IP routed through a residential proxy to defeat geo-detection, falls into a different risk category than a clean ISP connection. IP fraud scoring evaluates connection type, VPN/proxy likelihood, geo-mismatch against device location and prior fraud association.
- Phone enrichment adds another layer. A phone number registered two days ago, on a carrier known for disposable SIMs, with no associated accounts on any major platform, is a weak identity signal regardless of whether the number is technically valid.
- Velocity patterns tie the signals together. A withdrawal of the maximum bonus amount occurring 22 minutes after registration is one data point. Combined with a new email, a proxy IP and a device that registered four other accounts in the last hour, it becomes a pattern with a clear interpretation.
Checked individually, each of these signals has a plausible explanation. Checked together, they describe a fraud operation.
Why Most Onboarding Checks Miss It
Standard onboarding checks answer only part of the question. Verifying that identity data is real and consistent matters, but it says nothing about whether the account creation is isolated or coordinated.
Blackbox fraud models compound the problem. A model that outputs a risk score without explaining its reasoning creates an operational dead end. When a legitimate user gets declined, the customer service team has no explanation to offer. The risk team has no lever to adjust the threshold intelligently. The result is false positives that damage conversion rates — a known challenge across fintech platforms of all sizes.
Over-reliance on static blocklists creates a different failure mode. Blocklists catch known-bad indicators. Fraudsters burn through email domains, phone prefixes and IP ranges rapidly. A domain added to a blocklist today was probably abandoned yesterday. The fraud operation that generated it is already using new infrastructure.
Detect and block coordinated signups using device, IP and email signals.
Speak with an expert
How to Block It Without Hurting Legitimate Users
The goal is to separate isolated anomalies from coordinated patterns and to intervene proportionally.
Velocity rules are the primary instrument. A velocity rule triggers when a defined pattern exceeds a threshold within a defined time window. For detecting batch registration fraud, this could look like: more than 3 registrations from the same device ID within 60 minutes; a withdrawal event within 30 minutes of the first login; more than 5 accounts sharing the same IP subnet within 24 hours. Each rule is configurable — threshold and time window are variables, not fixed values.
The action attached to a velocity rule can be more nuanced than a block. The practical workflow separates three outcomes: approve, review and decline. Most anomalies trigger review. A new email with no digital footprint may warrant step-up verification rather than an outright rejection. A device matching five prior fraud cases warrants a decline. The distinction between reviewing and blocking is where false positive rates are managed.
Explainable scoring makes calibration possible. When a risk score of 74 is accompanied by the specific signals that drove it (email age: 3 days, IP connection type: data center proxy, device seen on two prior declined accounts), a risk analyst can evaluate whether the threshold is correctly set, see which signals carry the most weight and adjust without rebuilding the model.
Registration fraud scales because most onboarding stacks were built for speed, not detection. The platforms that catch it treat registration as a risk event, not just a conversion step. Risk teams tune thresholds without waiting on developers. Customer service agents can explain every decline. And legitimate users move through without added friction, because the scrutiny is directed at patterns, not individuals.
FAQ
Batch registration fraud involves creating large numbers of accounts in a short time window, usually from shared device infrastructure, to exploit promotional offers or onboarding incentives. The defining characteristic is coordination: accounts are generated programmatically, which produces detectable patterns in device data, IP addresses and behavioral timing.
Common evasion tactics include clearing cookies, using incognito mode, reinstalling apps or spoofing device attributes via emulators. Device intelligence that includes data across these methods uses hardware fingerprints, network configuration and behavioral biometrics that survive cookie clearing and app reinstalls.
A velocity rule monitors the rate at which a defined event occurs within a time window and triggers an action when that rate exceeds a threshold. The threshold, time window and triggered action (approve, review or decline) are all configurable independently
Layer signals rather than acting on any single indicator. Configurable score thresholds and review queues, rather than binary block/approve decisions, reduce the impact on conversion rates of borderline cases without letting coordinated fraud through.
The highest-value pre-registration signals are device fingerprint, IP reputation and connection type, email age and digital footprint, phone carrier and account age and velocity data across device and IP in the last 24 hours. Checking these before account creation completes is what separates preventive detection from reactive investigation.