Crypto transaction monitoring is the process of tracking digital asset movements across blockchain networks to identify suspicious activity, meet regulatory requirements and reduce exposure to financial crime.
This guide explains how crypto-specific monitoring works, how it differs from traditional AML approaches and what an effective implementation requires.
Key Takeaways
- Crypto transaction monitoring combines on-chain blockchain data with off-chain signals such as user identity, device data and behavioral patterns to detect suspicious activity.
- Blockchain analytics tools trace on-chain fund flows but cannot identify the person behind a wallet — off-chain intelligence fills that gap.
- The Travel Rule requires VASPs to collect and transmit originator and beneficiary information alongside transfers, directly shaping monitoring workflows.
- Non-compliance carries severe financial risk — Binance’s $4.3 billion DOJ settlement in 2023 remains the largest corporate criminal penalty in US history.
- Unlike traditional AML monitoring, crypto requires purpose-built detection logic — pseudonymity, chain-hopping and the Travel Rule create risks that fiat-era systems cannot address.
How Crypto Transaction Monitoring Works
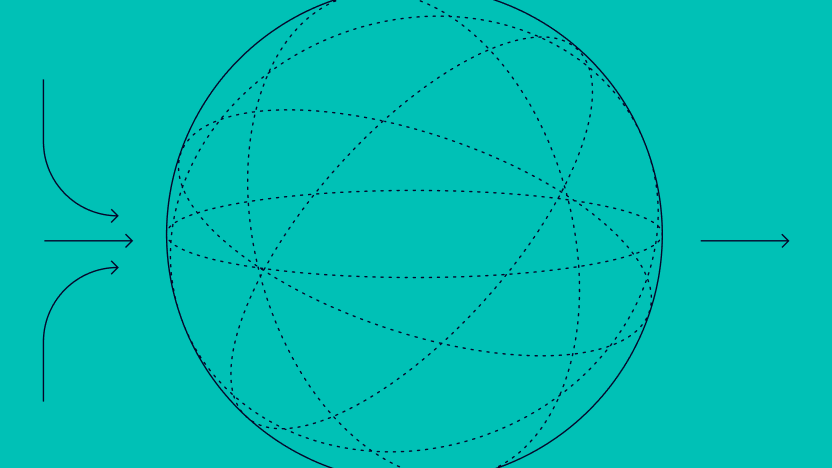
Crypto transaction monitoring operates across six sequential stages, each requiring tooling and logic that traditional AML systems were not built to handle.
1. Aggregating Multi-Chain Data
Effective transaction monitoring begins at the data layer. Crypto systems ingest raw blockchain data directly from nodes or third-party analytics providers — transaction graphs, wallet clusters and token contract interactions — rather than the structured ledger records traditional AML systems rely on. Off-chain data (identity records, device signals, IP addresses) is layered on top to provide the behavioural context the blockchain cannot provide on its own.
2. Cross-Chain Wallet Risk Scoring
Each transaction is scored against a richer set of variables than standard AML risk models use. Wallet exposure screening checks addresses against known high-risk entities — sanctioned wallets, mixer services, darknet markets. Cross-chain transaction history adds depth, and where available, Travel Rule data feeds serve as structured identity inputs, linking pseudonymous addresses to verified customer records.
3. Identifying Cross-Chain Typologies
When scoring surfaces anomalies, alert logic determines what gets flagged. This is where crypto monitoring diverges most sharply from conventional AML rules: effective detection must specifically identify mixer use, chain-hopping and peel chains, as well as high-frequency interactions with unhosted wallets — patterns that fall entirely outside standard rule sets.
4. Crypto Alerting
Flagged alerts move into investigation, which in crypto means following funds across multiple blockchains simultaneously. Unlike fiat investigations that rely on correspondent bank records, analysts must reconstruct fund flows across chains, correlating on-chain address clusters with off-chain identity signals to establish attribution. This step requires blockchain-specific tooling that fiat-era systems were never designed to handle.
5. Forensic Tracing & Technical SAR Narratives
Where investigation confirms suspicious activity, SAR filing requires a level of technical precision that standard templates don’t accommodate. Analysts must document the specific obfuscation technique identified, the sequence of addresses involved and the on-chain evidence supporting the suspicion — making it a considerably more demanding narrative than a conventional structuring report.
Automated SAR drafting tools can accelerate this by pre-populating narratives with structured on-chain data, improving both speed and consistency.
6. Unified Crypto Compliance Audit Trails
Throughout the entire process, audit-ready records must cover both on-chain monitoring activity and the associated off-chain identity data. This dual-layer audit trail — spanning blockchain evidence alongside KYC and behavioural records — is a crypto-specific compliance requirement that goes beyond standard transaction logging.
How Is Crypto Transaction Monitoring Different from Traditional AML Monitoring
The core AML monitoring workflow, including data collection, risk profiling, alert generation and investigation, applies to crypto as it does to any regulated financial activity. What makes crypto structurally different is the environment in which those controls operate.
- Pseudonymity: Crypto transactions are tied to wallet addresses rather than verified identities. A single individual can control thousands of wallets with no link between them, making attribution fundamentally harder than in traditional banking where accounts are identity-bound by design.
- Irreversibility: Once confirmed on-chain, a transaction cannot be recalled or reversed. Unlike a bank transfer flagged mid-flight, a suspicious crypto payment that clears before an alert is acted on is gone, making pre-transaction and real-time detection critical rather than optional.
- Cross-border speed: Crypto moves across jurisdictions in seconds, with no correspondent banking delays or currency conversion friction. A fund flow that would take days through traditional rails and trigger multiple compliance checkpoints along the way can traverse multiple countries and wallets in minutes.
- Blockchain-specific laundering techniques: Crypto enables obfuscation methods that have no traditional equivalent. Mixers pool and redistribute funds to break transaction trails; chain-hopping moves assets across multiple blockchains to obscure origin; peel chains fragment large sums through long sequences of small transfers. Each technique is a recognized form of crypto money laundering that requires specialist detection logic to catch.
- Fragmented regulatory frameworks: There is no global standard for crypto compliance. Requirements vary significantly by jurisdiction, from MiCA in the EU to FinCEN’s Travel Rule interpretations in the US to outright prohibition in some markets, meaning a platform operating internationally must manage multiple, sometimes conflicting, obligations simultaneously.
Why Is Transaction Monitoring Important for Crypto Firms?
The stakes of inadequate monitoring for crypto firms are clear: regulatory sanctions, reputational damage and direct financial exposure.
This section focuses on what is specific to the crypto context. For the broader compliance case, see our AML transaction monitoring article.
- On-chain data ingestion works differently from standard data collection. Traditional AML systems ingest structured records from internal ledgers and correspondent banks. Crypto monitoring must additionally pull from public blockchain networks, parsing raw transaction graphs, wallet clustering data and token contract interactions in real time. The data is open but unstructured, and volume can be extreme; a single active address may generate thousands of interactions across multiple chains simultaneously.
- Travel Rule data feeds directly into the workflow as a structured identity input. Under FATF’s Travel Rule, Virtual Asset Service Providers (VASPs) are required to collect and transmit originator and beneficiary information for qualifying transfers. This data, including names, wallet addresses and account numbers, enters the monitoring workflow as a compliance-mandated identity signal, helping link pseudonymous on-chain activity to verified customer records where they exist and flagging gaps where they don’t.
- Cross-chain tracing materially changes the investigation step. In traditional AML, following funds typically means requesting records across correspondent banks. In crypto, an investigator following a suspicious transfer may need to trace assets as they move from Bitcoin to Ethereum to a privacy chain, each hop requiring different analytical tooling and blockchain-specific expertise. Investigation workflows must account for this fragmentation rather than assuming a single ledger view.
- SAR narratives for crypto-specific typologies require different framing. Filing a SAR for mixer use or chain-hopping demands technical precision that standard SAR templates weren’t designed for. Analysts must document the obfuscation technique identified, the chain of custody across addresses and the on-chain evidence supporting the suspicion — a more technically demanding narrative than a conventional structuring or layering report.
Cryptocurrency Transaction Red Flags
Not all suspicious activity looks suspicious at first glance. In the crypto world, where anonymity, speed and global reach are the norm, unusual behavior often hides in plain sight. That’s why knowing the key red flags is critical for any exchange, wallet provider or crypto fintech aiming to stay compliant and secure. Here are some of the most common signs that should trigger closer scrutiny:
- High-frequency transactions in short timeframes: Especially when involving newly created wallets or addresses with no prior history.
- Unusual transaction patterns: Round-number transfers, structured amounts just under reporting thresholds, or activity inconsistent with known user profiles.
- Use of mixers or tumblers: These services obscure the origin of funds and are commonly linked to money laundering efforts.
- Interaction with high-risk jurisdictions: Transactions tied to countries with weak AML controls or under international sanctions raise immediate concerns.
- Rapid fund movement across multiple chains: Cross-chain transfers can be used to obfuscate the trail of funds and complicate tracking efforts.
- Minimal or falsified KYC information: Incomplete or suspiciously perfect user profiles can be a sign of synthetic identity fraud or mule accounts
While no single indicator guarantees wrongdoing, these red flags often point to elevated risk. Transaction monitoring systems must not only detect them but contextualize them, ensuring compliance teams focus on what truly matters.
Free up time and resources to build stronger fraud policies and customized rules.
See How Our Monitoring Works
Scaling within the Crypto Space
As crypto moves further into the financial mainstream, transaction monitoring has become a cornerstone of sustainable growth rather than just a compliance requirement. Platforms that treat it as a strategic capability rather than a checkbox are better positioned to scale across jurisdictions, onboard users with confidence and withstand regulatory scrutiny.
The gap between platforms that manage this well and those that don’t comes down to data quality and signal coverage. Monitoring programs that combine on-chain blockchain analytics with real-time off-chain signals, such as device intelligence, digital footprints and behavioral context, can act on risk as it develops rather than after funds have moved. For exchanges, wallet providers and crypto-native fintechs operating at scale, that speed of detection is what separates a flagged transaction from a completed one.
SEON gives crypto platforms access to 900+ real-time signals across the full customer journey from onboarding through to settlement, enabling compliance and fraud teams to detect suspicious activity earlier, reduce false positives and build the audit trails regulators expect. As the industry matures, so must its defenses, and monitoring that evolves alongside emerging typologies is what makes that possible.
Related Articles Around Crypto Fraud
- Cryptocurrency Fraud: What to Know & How to Protect your Exchange
- How to Detect Payment Fraud in Cryptocurrency Exchanges
- FIAT API Reduces Weekly Chargebacks From $40K to $0 with SEON
Sources
- Kroll: Global Enforcement of Anti-Money Laundering Regulation: Shift in Focus
- Europarl: Crypto assets: deal on new rules to stop illicit flows in the EU
- Bloomberg: Robinhood Crypto Unit Fined $30 Million by New York Regulator
FAQ
Effective crypto transaction monitoring tool must ingest on-chain data natively, screen wallet addresses against sanctions lists in real time, and support cross-chain investigation. Key differentiators are Travel Rule integration, configurable rule logic for crypto-specific typologies, and automated SAR drafting. Platforms that consolidate fraud and AML monitoring into a single workflow reduce both false positive rates and analyst workload.
Crypto transaction monitoring tracks activity in real time against predefined AML rules, flagging structuring, velocity anomalies or exposure to high-risk addresses as they happen. Blockchain analytics is a retrospective investigation tool, tracing funds across the ledger to map wallet clusters, identify illicit actors, and reconstruct transaction chains after the fact. Effective compliance programs use both: monitoring to catch suspicious activity early and analytics to support SARs and law enforcement requests.
The FATF Recommendations require virtual asset service providers (VASPs) to apply AML/CFT controls equivalent to those for traditional financial institutions, including ongoing transaction monitoring. In the EU, MiCA and the Transfer of Funds Regulation extend these obligations directly to crypto-asset service providers. In the US, FinCEN’s BSA rules require money services businesses operating in crypto to implement transaction monitoring programs. Most national regulators have now adopted or are actively transposing FATF’s VASP guidance.
FinCEN and equivalent regulators identify several high-priority typologies: structuring just below reporting thresholds, rapid layering through multiple wallets or chains, chain-hopping, and use of mixers or privacy coins on platforms that prohibit them. Any transaction involving OFAC-flagged addresses warrants immediate review. Context determines the threshold — a single pattern may not be sufficient; the combination of behavioural and on-chain signals drives the SAR decision.
The limiting factor is not alert volume but the analyst time required to review and close each case. Platforms scale by reducing false positives through risk-based rule finetuning and by automating low-complexity case handling. AI-generated SAR narratives and automated rule suggestions significantly reduce per-case workload: analysts review AI-generated outputs rather than writing from scratch. Consolidating fraud and AML monitoring into a single platform also eliminates duplicate review queues, thereby reducing effective headcount requirements.