Account Takeover Prevention
Catch Account Takeovers In Real Time
SEON detects suspicious login attempts using device, behavioral and velocity signals to block unauthorized access instantly.
TRADITIONAL AUTHENTICATION HAS BLIND SPOTS
How SEON Detects and Stops Account Takeovers
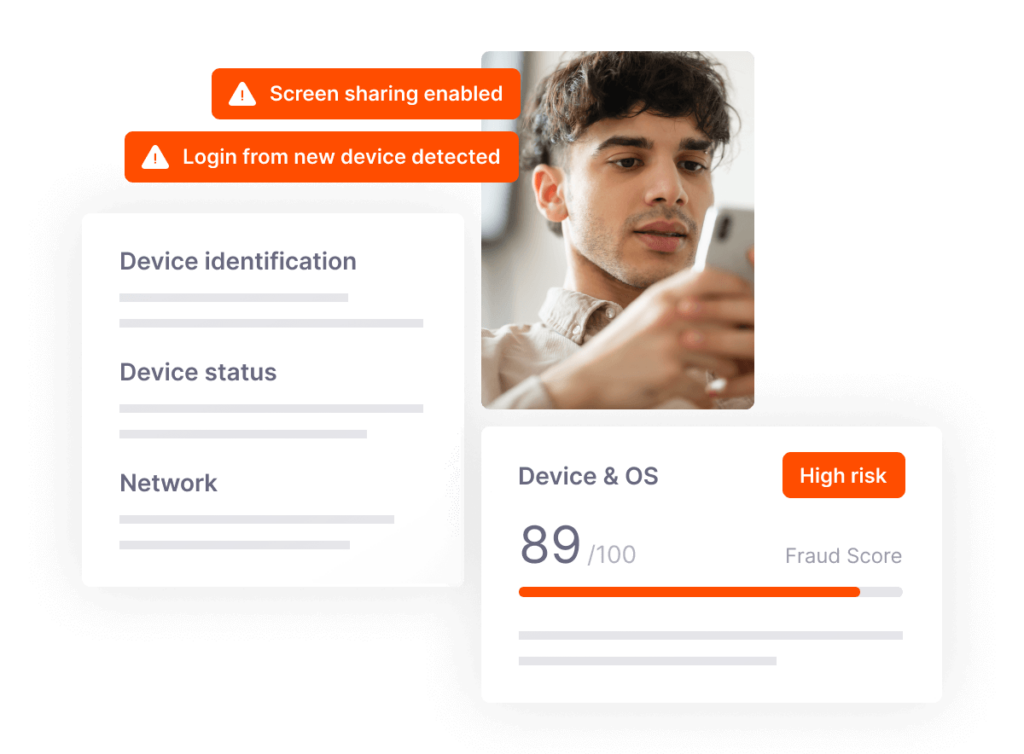
Stolen credentials, OTP interception and SIM swaps give fraudsters a way in. SEON analyzes device identity, behavioral biometrics and session activity to detect and stop account takeover attempts that traditional authentication misses.
Detect Suspicious Login Activity Early
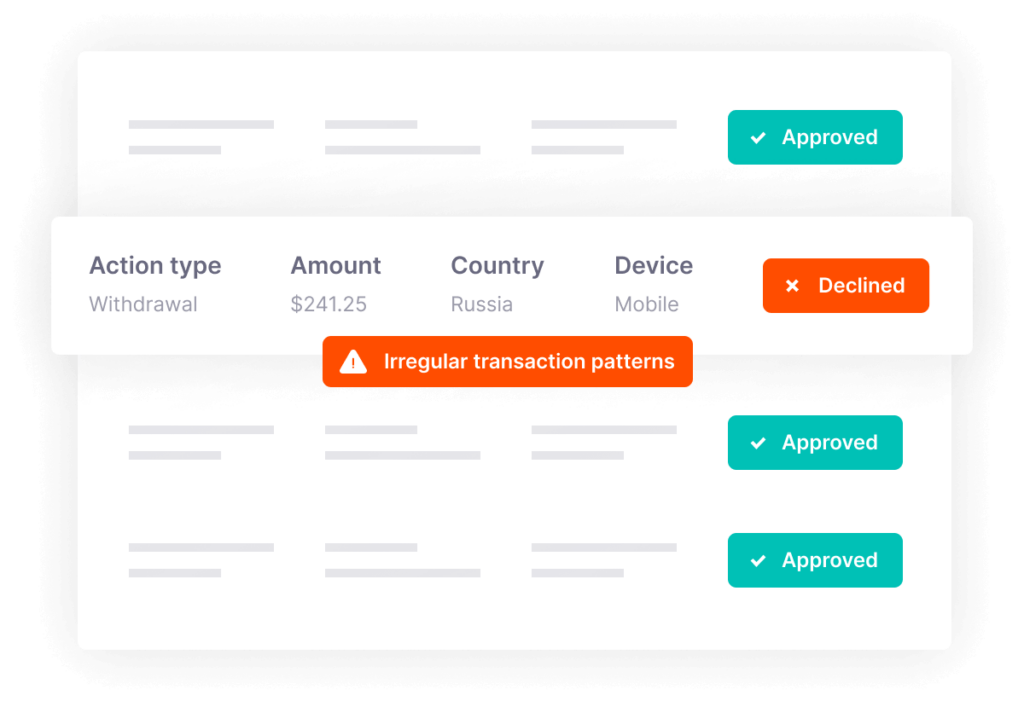
Automate Fraud Detection and Decisioning
Strengthen Account Security and Customer Trust
How Companies Block Account Takeovers
“What’s really cool is the way you can set up rules. There is a whole bunch of logic that we’ve just started playing with – the velocity checks when you change the device, the amount spent over a month, and so on. It gives us much more confidence that we can safeguard our customers’ accounts in the long run.”

Daniel Martinez
Head of Operations, Rebtel
“SEON shows you how much fraud is on the market, and with their help, you can reduce it. Working in real time is a key difference, and to top it off, the customer support is excellent; getting an answer very quickly, in easy-to-understand terms with examples – this is what I expect from a solution.”

Joeran Kiencke
Manager Risk Operations, Lottoland
Choose How to Integrate with SEON
The choice is up to you: integrate directly with SEON’s APIs or through the AWS Marketplace.
Learn More About Account Takeovers
-
Here’s why you need a robust alert system for account takeovers.
-
Account takeover risk assessments are key to ensuring you are not vulnerable to ATO attacks.
-
New account fraud explained: how it happens, red flags, and ways to stop fake or stolen-identity signups during onboarding.
-
Learn how to detect and prevent account takeover fraud using advanced tools like device fingerprinting and behavior analysis.
-
Learn how login and activity monitoring reduce account takeover risk in Brazil’s iGaming market.
-
What is Shopify fraud and how do you prevent it? See top apps to reduce chargebacks, stop ATO, and approve…
FAQ
Account takeover fraud occurs when an attacker gains unauthorized access to a user’s account, typically using stolen credentials, session hijacking or social engineering. Once inside, attackers can steal funds, make purchases, access sensitive data or use the account for further fraud.
Device intelligence identifies when logins originate from new, spoofed or previously flagged devices. Attackers rarely have access to the victim’s actual device, making device fingerprinting a strong ATO signal.
Yes. While MFA adds security, SEON’s ATO prevention detects unauthorized access through device, behavioral and network signals, regardless of the authentication method. Organizations without MFA still benefit from layered detection.
SEON scores risk silently in the background. Based on your configured thresholds, suspicious sessions can trigger the response defined in your risk framework, including step-up identity verification such as a selfie check or a temporary account freeze until an investigation is complete. Legitimate customers continue with fast, low-friction logins, while high-risk activity is contained immediately.
Device fingerprint changes, impossible travel, behavioral anomalies, velocity patterns, RAT detection and network characteristics combine to identify unauthorized access with high accuracy.
Take the First Step Toward Transformative Fraud Prevention
“SEON significantly enhanced our fraud prevention efficiency, freeing up time and resources for better policies, procedures and rules.”
Chief Compliance Officer, Soft2Bet
Trusted by 5,000+ global organizations:
Book Time With Our Experts
This form may not be visible due to adblockers, or JavaScript not being enabled.