Email profiling is becoming more and more sophisticated. Today, we’ll see how it works, and how you can leverage its power to improve fraud detection.
Try our tool below for free to see what it can reveal about your email address:
Check your IP fraud score here:
If looking up a phone number, please include its country code without plus signs, spaces or hyphens. By trying this tool, you’re agreeing to our Privacy Policy, General Terms of Service and Data Processing Agreement.
What is Email Profiling?
Email profiling, or any kind of profiling done based on a single data point, relies on a process called data enrichment. Here are the basics, of what it is:
- A user submits their email address to your system
- Your data enrichment tool checks and compares it against known databases
- The solution lets you know if the email address is suspicious or not
It is worth noting that data enrichment can be done manually. For instance, you could paste the email address into Google and see if any interesting results come up.
But of course, manual data enrichment is time consuming, difficult, and doesn’t really scale. Moreover, you might struggle to access certain databases, which is where a good fraud prevention tool can make all the difference.
Learn how reverse email lookup works, what data it uncovers, and how it helps detect fraud, verify identities, and analyze risk.
Read more
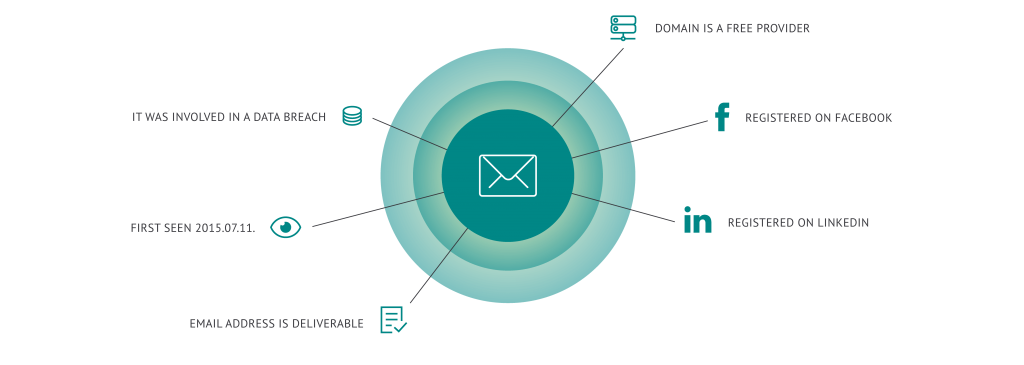
What Kind of Info Can be Collected from Email Profiling?
“…if you think about your own email address, it’s probably used to sign into a number of services, especially social media platforms. These are great places to investigate in order to validate the emails address usage.”
The first thing we will want to check is that the email address is real. This is done via:
- SMTP check: This is a simple, yet technical process that will ping the email server and returns a basic answer: Does it exist or not?
However, it’s extremely easy to create disposable email addresses hosted on real servers. A quick Google search will bring up hundreds of temporary or throwaway email address services. You simply log on and use it like a regular email platform, but the address is only valid for a limited period of time.
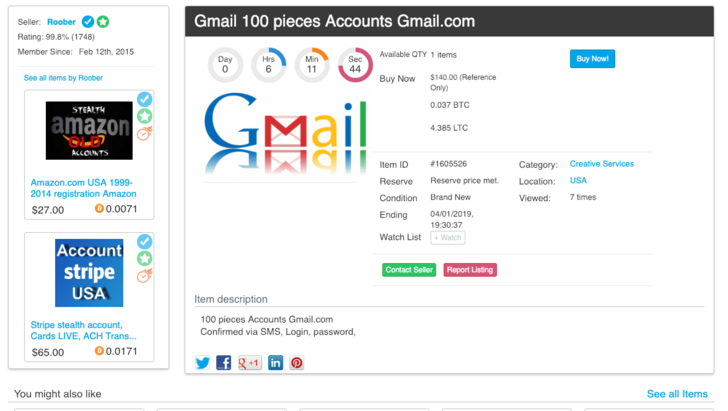
Moreover, fraudsters can bulk buy large numbers of real email addresses from official platforms such as Gmail or Hotmail. Some can even match a person’s stolen ID name, to make it look more official.
So a search should also let you know the following:
- Disposable address: By ensuring the domain is not one offered by temporary email services, we can lower the users’ risk score.
- Domain information: Is it a free domain? When was it created? Does it require SMS or any other verification to open it? How about recent updates? Just a number of data points that can give great insights into an email address validity.
Now if you think about your own email address, it’s probably used to sign into a number of services, especially social media platforms. These are great places to investigate in order to validate the emails address usage.
- Social Media Profiling: This process will essentially check if the email address has been used to sign on platforms such as LinkedIn, Instagram, Facebook, etc…
Then there are databases, both internal and external, useful for fraud prevention. So it’s important to check if the email address is associated with:
- Data breaches: Are the credentials openly available? Some services track all stolen account info, which makes it easy to see if an email address has potentially been released in the open before.
- Blacklists: Is this user a repeat offender? Have they been caught before? By sharing and cross referencing other blacklists, it should be easy to see if the user is legitimate or fraudulent.
Last but not least, some subtle data points that can reveal a lot about an email address. They all have to do with the string of letters, numbers and characters used in the actual email address name.
- Email risk assessment: Does the name on the email address resemble the user name? Does it use a number of suspicious characters or nonsensical words? Too many vowels vs consonant ratio? In short, this part of the system is trying to answer the question: Does this email address look fishy or not?
What About Fraud Risk Scores?
All the data enrichment above is great, but if you have to manually check it, you still end up doing a lot of the hard work. Which is why a good email profiling solution should also generate insightful fraud scores designed to let you mitigate fraud risk yourself.
Essentially, these will speed up the review process for you. But if you were to manually generate them, it would be a complex and tedious task. Which is why at SEON, we let machine learning algorithms do the hard work.
By combining the power of AI-driven systems and clear, human-readable results, we believe companies large and small have more control over how they manage fraud on their platforms.
Is Data Enrichment Legal?
Yes – provided it complies with data protection regulations. Which is why the SEON Intelligence extension and Email modules only use open source databases to cross check information.
How Can I Profile my Users’ Email Addresses?
At SEON, we have a number of flexible solutions that can be tailored to the way you fight fraud. The chief way that you can use SEON’s email verification software capabilities to combat fraud is by running a user’s email address into the software’s social profile lookup function.
This allows you to view SEON’s results after it’s run an online check to see which, if any, social media/general online accounts the given email address is registered to. This can help you determine the extent to which the email address is either suspicious or trustworthy – with a non-existent online presence being the most dubious result. After all, how many people don’t at least have a Netflix profile nowadays?
Conclusion
An email address is a lot like a digital passport. Since 51% of internet users have kept theirs for more than 10 years, it’s easy enough to quickly confirm their identity. But like real passports, it’s easy to fake them.
Luckily, a good email analysis tool will put all the odds in your favour to intelligently detect suspicious email addresses. Combined with other tools such as device fingerprinting or IP analysis, it’s easy to see how fraudsters are increasingly hindered by SEON.
Working with SEON gives you complete user profiles in an instant, helping you to reduce fraud rates.
Ask an Expert
You might also be interested in reading about:
- SEON: When Should You Deploy a Customer Risk Assessment Tool?
- SEON: The Ultimate Fraud Risk Assessment Checklist
- SEON: How an Email Data Breach Helps you to Verify Users
Learn more about:
Browser Fingerprinting | Device Fingerprinting | Fraud Detection API | Fraud Detection with Machine Learning & AI