Most payment fraud detection strategies focus on merchants or cardholders who have a direct relationship to the transaction. Payment Service Providers (PSPs) operate as the critical infrastructure in the middle, processing volume for thousands of merchants simultaneously without owning the end-customer relationship.
Global card fraud losses hit $33.41 billion in 2024, and the Nilson Report projects they will reach $41 billion by 2030. A growing share of that fraud flows through PSP infrastructure, where detection tools were never designed for the structural gap PSPs actually face.
This gap is where PSPs must learn to detect risk at scale. It requires identifying threats without the data banks see or the control merchants have, all while ensuring that risk management never slows down legitimate payment volume across the network.
Key Takeaways
- PSPs inherit risk from every merchant they onboard but lack the customer-level data that banks and merchants use to detect fraud.
- Transaction data arrives from merchant integrations in inconsistent formats, without the enrichment needed to surface patterns in real time.
- Risk doesn’t stop at the gateway, it starts at merchant onboarding and extends through payouts and withdrawals.
- Built-in PSP fraud tools were designed for predictable risk at moderate volume and break down as merchant diversity and transaction scale increase.
Why Fraud Detection Is Different for PSPs
Most fraud tools assume access to customer identity, transaction history and behavioral baselines. PSPs have none of that: they inherit risk from every merchant they onboard, across every market they operate in, with no direct line of sight into who is on the other end of a transaction.
PSPs don’t own the customer relationship
When a suspicious transaction comes through, a bank can check it against years of cardholder behavior, while a merchant can compare it to a buyer’s purchase history. A PSP can do neither. The only question available is whether the transaction looks normal relative to that merchant’s volume. That’s a fundamentally weaker signal, and it’s often the only one a PSP has to work with.
Risk is distributed across merchants and transactions
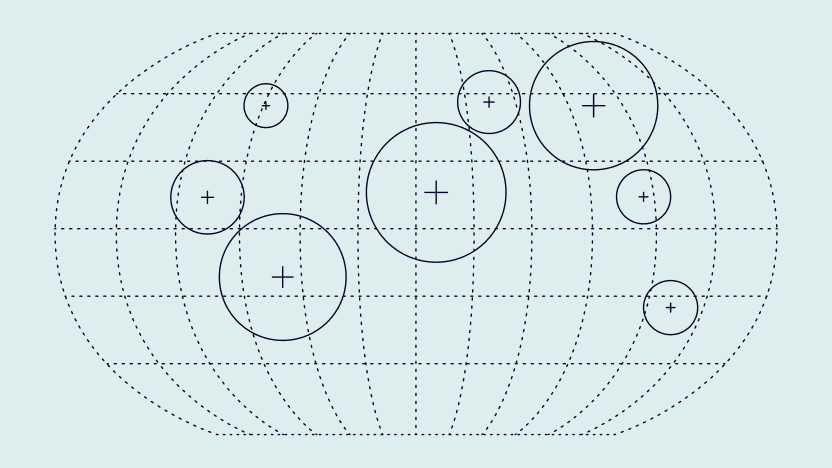
That weaker signal also has to cover a much larger surface. A PSP’s fraud exposure accumulates across an entire merchant portfolio: a single high-risk merchant, an unusual spike in chargebacks across five mid-tier merchants or a coordinated attack exploiting multiple accounts. Managing risk at that scale requires visibility at both the transaction and portfolio levels simultaneously, but most fraud tools optimize for one or the other.
Fraud happens across the entire payment flow
The exposure doesn’t stop at the transaction either. Gateway-level fraud detection catches problems at the point of payment authorization, but PSP fraud risk starts earlier and ends later. It begins with merchant onboarding, when a fraudulent business gains access to payment rails and continues through settlements, payouts and withdrawals. Gateway-only monitoring misses everything that happens before and after the payment.
The Real Problem: Lack of Visibility Into Transaction Risk
PSPs can handle scale, so volume isn’t the real challenge. The problem is that transaction data arrives without the structure or enrichment needed to make it useful for payment fraud detection. Without context, even high-risk patterns stay buried in the noise.
Why PSPs struggle to see risk in real time
One merchant sends IP and billing country, another sends email and amount, while a third sends card data and a timestamp. With no standardized format to connect the dots, a velocity spike across all three remains invisible.
Real-time detection requires data that is already structured and enriched at the point of decision, and most PSPs don’t have that. They have raw transaction logs from dozens or hundreds of integrations, each formatted differently, lacking data enrichment with the behavioral or device-level data that makes risk signals meaningful.
The limits of manual monitoring and static rules
A rule that flags transactions over $5,000 misses a coordinated attack using 200 transactions at $49 each, because the rule was written for a different type of fraud. Static rules don’t adapt to new patterns, and the longer they stay in place, the more predictable they become to the attackers working around them.
Manual reviews compound the problem. Analysts working through queues can evaluate one case at a time, which means the fraud that gets caught tends to look like last quarter’s fraud. Everything that doesn’t match an existing pattern passes through.
Why proving risk matters for compliance and partners
Card networks set explicit chargeback thresholds, and PSPs that breach them face fines, monitoring programs or merchant termination. Acquiring banks layer their own requirements on top, often demanding evidence that the PSP is actively monitoring and managing risk across its portfolio.
Without that evidence, the commercial relationship is at stake. A PSP that can’t demonstrate how it detects and acts on risk is a liability to the partners it depends on to operate.
Where Risk Appears in PSP Payment Flows
Risk surfaces at three different stages: merchant onboarding, transaction processing and payouts. Each stage has its own unique signals and requires a different detection approach.
Merchant onboarding risk
High-risk actors increasingly target PSPs through the merchant onboarding process, submitting falsified business documentation or misrepresenting business type to gain access to payment rails. Some establish accounts specifically to launder funds or commit friendly fraud at scale.
Onboarding checks that rely solely on document verification miss signals that emerge during account setup: device data, email age, IP geolocation mismatches and patterns matching previously flagged merchant profiles.
Transaction-level risk signals
At the transaction level, risk signals include velocity anomalies like sudden spikes in transaction frequency or value, unusual geographic patterns and mismatches between billing and IP location. Behavioral inconsistencies in how a session interacts with the checkout flow also carry weight.
For PSPs, the challenge is evaluating these signals across merchants simultaneously. A legitimate flash sale at one merchant looks very different from a coordinated fraud attack hitting five merchants at once, but both produce a sudden volume spike. Distinguishing between them requires portfolio-level context.
Payout and withdrawal risk
Payout risk is where PSP exposure can become severe quickly. Bad actors who gain access to a merchant account or create a fraudulent one will drain available balances through withdrawals or redirect payouts to mule accounts.
The strongest signals at the payout stage are sudden changes in bank account details and withdrawal amounts that exceed recent transaction volumes. Payout destinations that don’t match the merchant’s historical patterns also deserve scrutiny, particularly when combined with recent changes to account credentials.
How PSPs Detect Risk Without Full Customer Data
PSPs detect risk without full customer data by combining behavioral signals, velocity patterns and merchant-level anomalies at the transaction and portfolio level. Unlike banks or issuers, PSPs need to prevent payment gateway fraud by assessing risk from extremely limited data: transaction patterns, merchant behavior and signals from across the network.
1. Using behavioral and velocity signals
PSPs use behavioral and velocity signals to infer risk from session-level data without needing cardholder identity. Short sessions, transactions initiated in rapid succession, and consistency in user behavior are all signals that convey risk information, regardless of who the end customer is.
2. Identifying merchant-level anomalies
Individual transactions can look clean even when a merchant is behaving suspiciously at the portfolio level. Chargeback ratios creeping upward, transaction approval rates diverging sharply from peers in the same vertical and sudden shifts in average order value are merchant-level signals that only become visible when you look across the entire lifecycle.
3. Detecting network-wide patterns
The most sophisticated fraud attacks do not announce themselves at a single point. They distribute activity across merchants, payment methods and time periods specifically to avoid triggering any single threshold. When the same device fingerprint appears across three different merchants in a PSP’s portfolio within 48 hours, that in itself is a signal, even if no individual transaction crossed a threshold.
Key Capabilities PSPs Need to Detect Risk at Scale
Identifying risk is only half the problem. PSPs also need the infrastructure to act on it in real time, at transaction volume, without slowing down payments or overwhelming risk teams.
Real-Time Risk Scoring Across Transactions
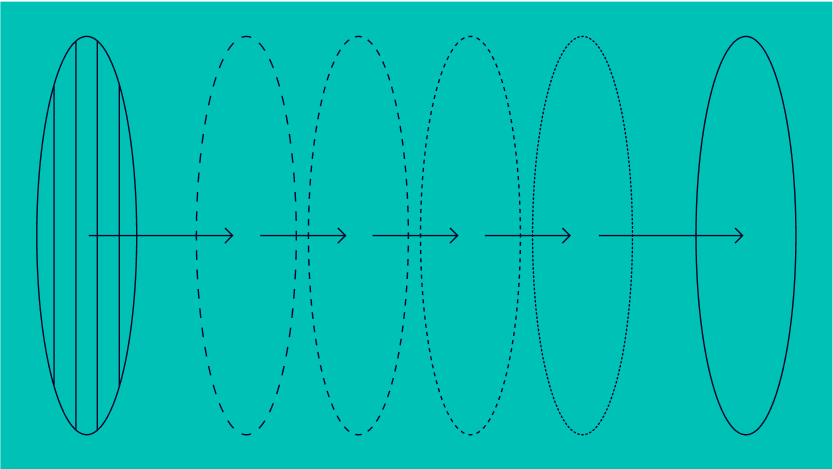
Risk scoring must operate within the authorization window, which for most card networks is measured in milliseconds. Scoring models that require batch processing or manual review queues cannot operate at that speed. Effective real-time scoring draws on transaction data, device intelligence, behavioral patterns and merchant context simultaneously to assess risk before the payment authorization completes.
See how Enovipay scaled fraud detection across high-risk merchant verticals without adding headcount.
Read case study
Flexible Rule Engines and AI-Assisted Detection
Static rule sets break fast: the fraud patterns targeting PSPs today are not the same ones from 18 months ago. PSPs need rule engines that allow risk teams to create, test and adjust rules without engineering support, combined with AI-assisted detection that identifies emerging patterns no one has written rules for yet.
Alerts, Case Management and Investigation Workflows
Detection without action is just noise. PSPs need tools that translate risk signals into structured workflows: alerts that reach the right analyst, case management that tracks decisions and outcomes, investigation tools that give analysts enough context to make a call quickly. Without structure, risk teams end up working from spreadsheets and email threads. That works at 50 merchants but will definitely collapse at 500.
How SEON Helps PSPs Detect Risk Beyond the Gateway
SEON gives PSPs real-time risk scoring across transactions, merchant monitoring at the portfolio level and cross-network pattern detection, without requiring full end-customer data.
Risk teams get a flexible rule engine they can operate directly, AI-assisted detection that adapts to emerging patterns and case management tools that turn alerts into structured investigations. For PSPs that need compliance documentation, SEON provides the audit trails and decision transparency that Visa, Mastercard and acquiring banks require.
FAQ
PSPs must detect high-risk transactions without blocking legitimate payments. This requires a risk-based approach that evaluates transaction patterns, merchant behavior and network signals in real time, rather than relying on rigid rules that lead to unnecessary declines.
Reducing false positives starts with better context. By analyzing behavioral patterns, transaction velocity and merchant-level activity, PSPs can distinguish between genuine and suspicious activity more accurately, approving more legitimate transactions while still controlling risk.
Real-time risk detection must operate within strict latency constraints to avoid slowing down payment processing. PSPs typically use lightweight scoring models and pre-configured rules that can evaluate transactions instantly, ensuring risk checks do not impact user experience or conversion rates.
Binary rules approve or decline transactions based on fixed thresholds, which can be too rigid at scale. Risk-based decisioning assigns a score to each transaction, allowing PSPs to take more flexible actions such as approving, reviewing or flagging activity based on overall risk levels.