User activity monitoring may appear simple, but in fraud detection, it reveals a critical and complex process. As cyber threats and fraud evolve, tracking user behavior is key to effective risk management.
This article explores the crucial role of user activity monitoring in fraud detection, offering real-world examples that highlight its power in detecting and preventing fraud. We’ll also cover best practices to optimize your monitoring efforts.
Whether you’re new to this field or looking to improve existing strategies, this guide provides the insights and tools necessary to strengthen your fraud prevention approach.
What Is User Activity Monitoring?
User activity monitoring (UAM), often referred to as user access monitoring, involves the implementation of systems designed to log and track user actions across devices, networks, and websites. In the context of fraud detection, “user” can refer to customers, visitors, or even internal company employees, all of whom are potential sources of risk.
The primary objective of UAM is to analyze data on how users interact with digital platforms such as websites, apps, or other online products, extracting valuable insights from this information. While UAM can be used to enhance customer segmentation, streamline business processes, and improve overall efficiency, its most critical application lies in reducing risks associated with cybersecurity, IT security, and, notably, fraud detection.
This data becomes a powerful tool in protecting businesses from financial and reputational damage. By identifying patterns of malicious behavior, whether originating from internal sources like employees or external threats, UAM helps detect and stop fraudsters before they can cause significant harm. In this way, UAM optimizes internal operations and serves as a frontline defense against fraud, preserving the return on investment (ROI) by preventing costly breaches
Learn how an iGaming company automated risk reviews with SEON to free up 40% more resources.
Read the Case Study
How Does User Activity Monitoring Work?
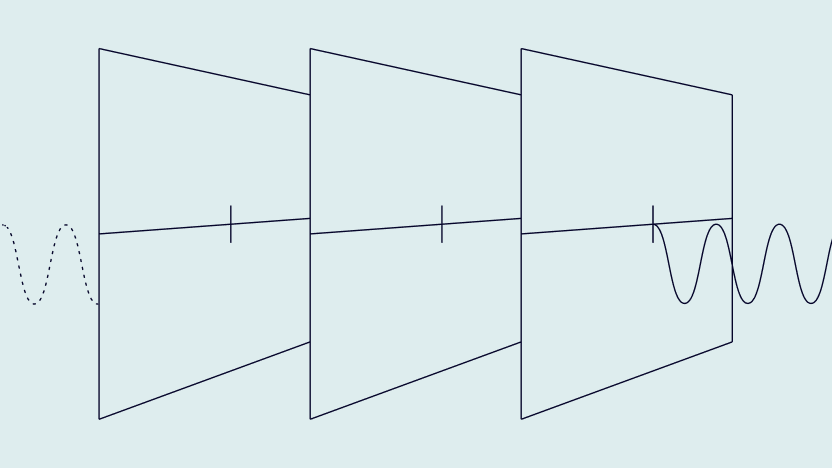
User activity monitoring works by gathering user activity data on a website, server, device, or app. The data is labeled and sorted so that organizations can interpret it for marketing, security, or productivity purposes. For user activity monitoring to work, a company must deploy specific tools that are either built-in, developed in-house, or purchased and integrated, usually via a SaaS model. You can read more about build vs buy fraud solutions here.
Some user activity monitoring solutions focus on recording key actions (such as clicking on buttons or opening web links), while other tools offer more sophisticated session recordings, capturing every action in video form.
The B2B market is abundant with tools and features designed to capture as much valuable user data as possible. A non-exhaustive list of these include:
However, collecting every data point isn’t always efficient. Depending on your user activity monitoring strategy, focusing on specific data points is much more effective rather than taking a one-size-fits-all approach or getting lost in endless data.
These days, most software comes with user logging, so you have full visibility of which user has done what. You can also monitor suspicious activity and investigate what went wrong. That is a start, but you would want to capture even more for many use cases.
Is User Activity Monitoring Illegal?
No, user activity monitoring is not illegal – broadly speaking, at least. In fact, the GDPR specifically states that user monitoring is legal when necessary for the purpose of preventing fraud and for targeted marketing:
“The processing of personal data strictly necessary for the purposes of preventing fraud also constitutes a legitimate interest of the data controller concerned. The processing of personal data for direct marketing purposes may be regarded as carried out for a legitimate interest.”
Recital 47
However, the fact that user activity monitoring essentially amounts to a form of surveillance makes things a little more complicated. It means that restrictions come into play around how data is collected, stored and used (courtesy of the GDPR in Europe and the Electronic Communications Privacy Act and Stored Wire Electronic Communications Act in the US).
The crux of this, so far as GDPR is concerned, is that UAM data may include personal data. This brings requirements around data obfuscation, encryption, and retention into the spotlight. Over in the US, state-level legislation comes into play as well, meaning that every business must pay close attention to the requirements of multiple pieces of legislation if it is to remain on the right side of the law when monitoring user activity.
User Activity Monitoring Tools
User Activity Monitoring tools are designed to detect suspicious behavior and activity, helping businesses monitor users and prevent fraudulent actions. These tools track a wide range of actions across websites and applications, including login attempts, transaction activities and account changes, providing visibility into user behavior patterns.
Key features include real-time alerts that notify teams of potentially fraudulent activities, such as unauthorized access attempts or unusual patterns. This proactive defense helps businesses quickly address threats and minimize the risk of fraud.
Many tools also offer detailed activity logs, recording events like failed login attempts or account takeovers. Some solutions go further by capturing device or location data to help verify user legitimacy. Tailored to meet specific fraud prevention needs, these tools enhance security, ensuring that risky behavior is flagged and handled before it impacts the business.
5 Reasons to Implement User Activity Monitoring
Implementing user activity monitoring delivers deep insights into how users are behaving, whether internal staff members or external customers. This means that businesses can make better-informed, data-driven decisions on a range of matters. They can use anything from organization-wide data to individual use cases to inform their thinking and actions.
This puts businesses in a strong position to fight fraud, safeguard their data, assess risks, identify short—and long-term trends, meet legal and compliance obligations, and take a more strategic, informed approach to their future plans.
Here are five key reasons why UAM should be a priority for any company operating in the digital sphere:
1. Data Security
One key reason to monitor users is to secure a company’s data, both physically (IT security) and digitally (cybersecurity). In 2022, the average cost of a data breach reached a record $3.86 million, according to IBM.
Whether the warning signs exist inside internal SQL databases, OS or other administrative commands, malicious patterns associated with potential data breaches can be detected when a comprehensive UAM platform is implemented. This is true whether the patterns originate from customers, employees or executives. Any kind of unwanted change will be logged and potentially blocked, depending on its severity.
2. Legal and Compliance
Compliance monitoring is a regulatory requirement for companies in the context of KYC and AML. It also involves looking at user data and behavior. Relevant data must also be logged when submitting a suspicious activity report, aka SAR.
The goal is to reduce risk, which in this case includes the risk of having to pay a heavy compliance fine by allowing identity thieves and money launderers to interact with your business.
3. Affiliate Security
Web analytics are a major part of user activity monitoring. Marketing teams will certainly use user activity monitoring services and web analytics to improve website experiences and, ultimately, the road to checkout. However, any marketing team employing affiliate programs like pay-per-click should also be using that data to catch fraudulent affiliates.
A particular problem for companies large enough to have automated affiliate onboarding systems in place is the plenty of shady online outfits that exist purely to take advantage of various PPC marketing campaigns. PPC affiliates can collect a premium for directing traffic to a website offering such a campaign. UAM can help detect fraudulent affiliates directing bot traffic to partner sites and collecting payouts for apparently legitimate traffic. In other cases, fraudsters mislead real people to the site through pop-ups, layered links, or other malicious online practices – naturally, these rarely lead to a sale.
4. Fraud Prevention
User monitoring is a core feature of fraud prevention. You want to be able to separate legitimate customers from fraudsters. This involves collecting data relating to the following:
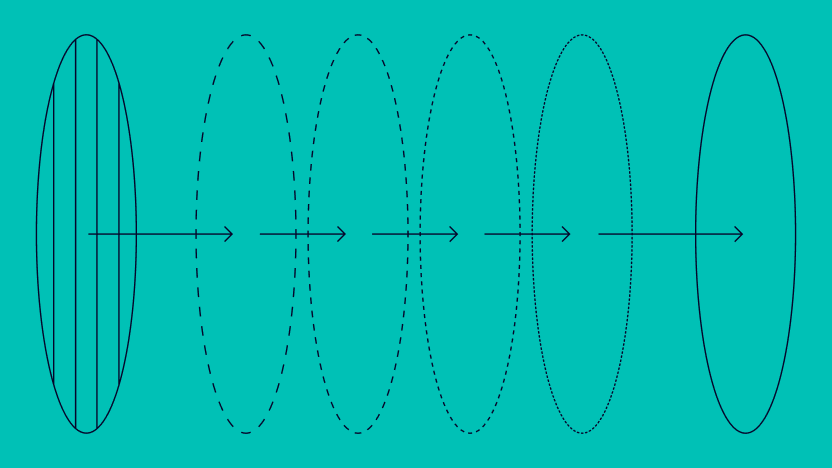
- The user’s identity, either through document verification steps or digital footprint analysis, which looks at alternative data such as their device setup and social media activity.
- The user’s behavior: By monitoring and comparing user actions (for instance, a signup or money deposit), we can identify suspicious behavior that may point to fraud or high-risk customers.
- The user’s connections: The user may be part of a fraud ring or multi-accounting. To stop them, we will be looking at similarities in data points to catch as many members and related accounts as possible.
Prevent fraud by monitoring user behavior, detecting suspicious patterns, and blocking fraudulent transactions. Automate defenses with AI and reduce manual reviews to stop fraud efficiently.
How It Works
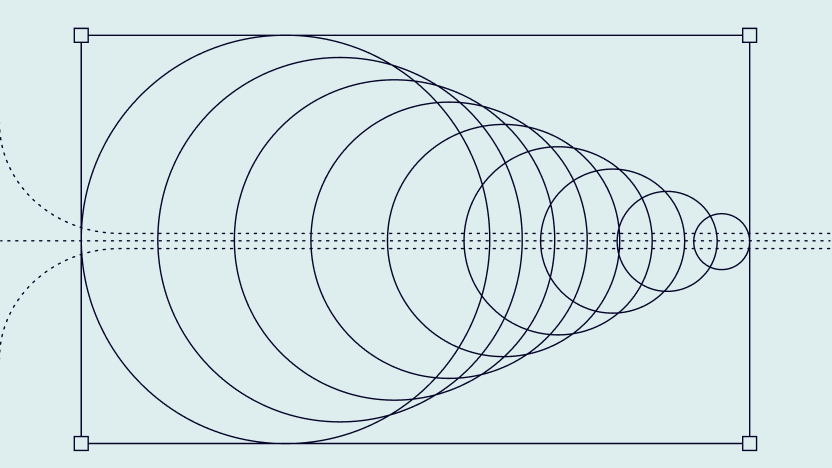
5. Bot Detection
Another important aspect of fraud prevention is the ability to detect when a user is exhibiting behavior that is less like a real person and more like an automated bot – a sadly common tool of many fraudsters.UAM is overwhelmingly important when it comes to bot detection. Of course, bots interact with apps and websites very differently from humans, and since many fraudsters use bots at scale, with dozens or even thousands of bots, these interactions are repeated and thus easier to flag as bad traffic. Users that repeat the exact same usage pattern, move at inhuman speeds, or attempt to shove themselves through a single gateway at once for attacks like credential stuffing are easily detected with UAM – indeed, this is one of the primary functions of a strong user activity monitoring system.
Best Practices for User Activity Monitoring
While every company can benefit from user activity monitoring, it can also be seen as a controversial practice, especially for users who value their privacy. This is why it is important to respect the best practices.
- Be transparent about user activity monitoring: the users, whether they are employees or online customers, should be aware of the ongoing monitoring, whether it’s stated in an online policy, terms, and conditions, or a contractual agreement.
- Anonymize data when possible: while you can monitor user actions and link them to a specific account, it is often beneficial to hide these connections if possible, for instance via tokenization or using data hashes.
- Allow privileged access to the data: in another effort to minimize the potential for falling foul of data privacy regulations, you should only allow certain positions to access the data (for instance, data analysts, marketers, or cybersecurity experts).
- Draft better data protection policies: these should include your monitoring actions outlining acceptable use, your handling of sensitive data, authorized services and applications, etc.
- Be vigilant with third-party providers: it’s crucial to understand your obligations as a company, but also to double-check whether the company that provides your user activity monitoring solution is also fully compliant with data protection regulations.
Finally, it’s also worth considering how you choose your user activity monitoring solution, as multiple user activity monitoring tools can be combined into one. For instance, marketing analytics and fraud prevention software for user activity monitoring may have overlapping features.
How Can SEON Help With User Activity Monitoring?
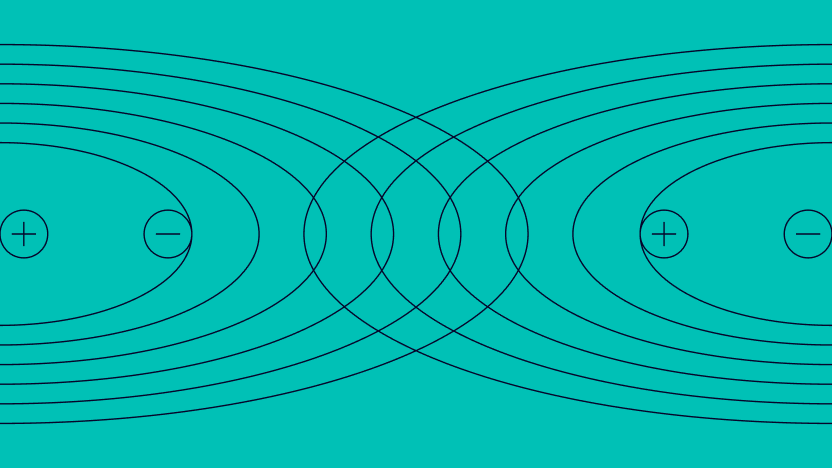
SEON is a comprehensive fraud prevention software that excels in user activity monitoring for fraud detection and risk management. It operates in three key steps: capturing user data, enriching it with additional insights and analyzing it using customizable risk rules and AI-powered machine learning. This approach helps businesses assess the risk of user actions to:
- Automatically flag suspicious behavior
- Block fraudulent logins and signups using stolen or fake data
- Enhance KYC and AML checks
- Categorize users by risk level (low, medium, high)
- Identify high-value or low-value customers
- Mitigate various forms of fraud, including payment fraud, bonus abuse and chargebacks
One of SEON’s standout features is its use of velocity rules, which monitor user activity within specific timeframes. This allows your risk team to flag abnormal patterns like multiple login attempts or excessive password resets for further review.To effectively manage compliance, prevent fraud and secure user accounts, SEON’s digital onboarding and registration monitoring solutions provide robust protection at every stage.
Frequently Asked Questions for UAM
Most companies rely on user activity monitoring software, which logs and records user data. The features may include keylogging, video recordings, or data logs.
User activity includes any kind of interaction on your server, system, app, or website. This may be a transaction, a signup, a login, or even browsing and filling out a form.
User activity monitoring looks at all kinds of user actions, while user access monitoring tends to only focus on access permissions. However, both terms are increasingly used interchangeably, and both are often shortened to UAM.
Sources