A single fraudster looking for a quick payout is one problem. A coordinated group with shared resources, specialized roles and a repeatable playbook is another.
Fraud rings are organized. They plan. And because every member of the group can look clean on their own, they are significantly harder to catch than opportunistic fraud.
This guide covers what fraud rings are, how the most common types operate and what it actually takes to detect them before the damage is done.
What Is a Fraud Ring?
A fraud ring is a group of individuals working together to commit fraud in a coordinated way. Unlike a solo fraudster acting on impulse, fraud rings operate more like a business: roles are divided, methods are refined and attacks are repeated across multiple targets.
Most rings do not specialize in a single attack type. It is common for one ring to combine identity theft, account takeover and money laundering across a single campaign, often working with specialists in each area.
Defining exactly what makes a fraud ring is harder than it sounds. Some are two or three people sharing resources and splitting profits. Others are large criminal networks spanning multiple countries. What they have in common is that no single member needs to do everything, and that coordination is what makes them harder to catch than a solo fraudster.
Types of Fraud Rings
There are, plainly speaking, as many types of fraud rings as there are types of fraud. Here are examples of the most common ones you may encounter online:
Synthetic Identity Fraud Rings
Synthetic identity fraud is now one of the fastest-growing threats facing online lenders, BNPL platforms and digital banks. Rather than using purely stolen identities, modern fraud rings engineer new ones: combining real and fabricated personal data to create profiles that pass standard identity checks.
What makes these rings difficult to catch is the investment they make in building credibility. Profiles are given manufactured digital histories. Social media footprints are linked to registration emails to simulate a real person. The identity looks legitimate because it was designed to.
Who is affected? Banks, digital banks, online lenders, BNPL companies, crypto platforms and any business with a KYC process.
Credit Card Fraud Rings
Credit card fraud rings remain one of the most common forms of organized payment fraud. The core model involves acquiring stolen card numbers, encoding them onto new cards and using them to purchase high-value goods for resale.
What has changed is the sophistication of the operation. Modern rings use residential proxy networks and mobile botnets to mask their activity, moving away from the static datacenter connections that legacy detection tools were built to catch.
Who is affected? Online retailers, brick-and-mortar stores and any business processing card-not-present transactions.
Account Takeover Fraud Rings
As synthetic identities have become harder to generate at scale, fraud rings have shifted focus toward stealing accounts that already exist. Hijacking an aged, verified account is more efficient than building and aging a fake one from scratch.
The attack pattern is precise. Rings identify high-value accounts through credential stuffing or brute-force attacks, then access them through unrecognized devices or foreign IP addresses. The goal is often retention bonuses or stored payment methods rather than the account itself.
Detection requires looking beyond the signup gate. A verified account accessed from a new device and a foreign IP after months of inactivity is a signal that traditional identity checks will not catch.
Who is affected? iGaming operators, financial platforms, any business offering loyalty programs or stored payment methods.
Dormant Account Fraud Rings
One of the most sophisticated patterns emerging from professional fraud rings involves what security teams have started calling sleeper cell tactics. Rings acquire aged, verified accounts and deliberately keep them dormant. The goal is to fall outside standard risk observation windows, which are typically calibrated for new account activity.
Once off the radar, the account is activated for a high-value transaction or bonus claim. Because the account is already verified and has a legitimate history, it bypasses the security checks reserved for new users.
The shift in defense this requires is significant. Operators can no longer ask only “who are you?” at signup. They need to continuously ask “are you still the same person?”
Who is affected? iGaming operators, financial platforms and any business where account age or verification status grants elevated trust.
Money Laundering Fraud Rings
Money laundering rings rely on scale and coordination to move illicit funds through legitimate-looking transactions. Banks and financial institutions remain the primary targets but the threat extends to online retailers, BNPL companies and crowdfunding platforms.
Modern laundering rings exploit data silos between disconnected fraud and compliance systems. When fraud detection and AML monitoring operate separately, the connections between accounts are harder to surface and rings can move funds across platforms without triggering alerts in either system.
Who is affected? Banks, digital banks, online lenders and any platform processing high volumes of transactions.
SIM Jacking Fraud Rings
SIM jacking involves transferring a target’s phone number to a SIM controlled by fraudsters. Once they control the number they receive all SMS and two-factor authentication codes, giving them access to linked accounts.
Modern SIM jacking rings have raised the sophistication of their attacks significantly. Residential proxies are used to mask geographic signals. AI-generated deepfakes are deployed to bypass liveness verification and selfie-based onboarding checks. High-profile individuals remain targets but rings increasingly attack accounts at scale rather than focusing on single high-value victims.
Who is affected? Telecoms, financial platforms and any business using SMS-based two-factor authentication.
How to Detect Fraud Rings
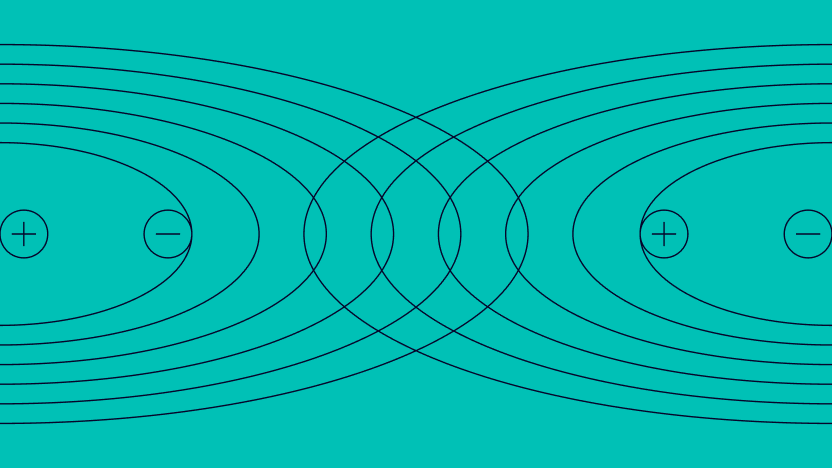
Detecting a fraud ring means looking for connections between users. A single account may look clean. The pattern across multiple accounts is where the fraud becomes visible.
Collect as much data as possible
Start with what you have: email addresses, phone numbers, IP addresses, device data and card details. The more signals you can gather at the point of onboarding, the easier it becomes to find shared data points later.
Enrich the data
Data enrichment exposes information that is not immediately visible. Social media profiles linked to an email address, whether an IP points to a VPN or proxy, whether a card number is prepaid. These signals add depth without adding friction to the user journey.
Enrichment also helps surface the manufactured digital histories that synthetic identity rings build. A profile with a social media footprint that was created recently and linked to a registration email the same day is a signal worth investigating.
Look for patterns across accounts
Fraud rings cannot run infinite devices. They rely on emulators and spoofing tools, which means shared device configurations appear across multiple user accounts. Filtering by device hash, operating system, installed plugins or IP subnet can surface connections that are invisible at the individual account level.
Modern rings are aware of this and invest in residential proxies and unique hardware to avoid basic detection. Multi-signal alignment — verifying device, IP address, phone number and email together rather than in isolation — is what catches them.
Visualize connections
Graph visualization maps the relationships between users based on shared data points. A cluster of accounts sharing the same device fingerprint and email structure is a signal worth investigating. The same accounts sharing an ISP alone may not be.
SEON’s network analysis tools allow fraud teams to switch between interactive graphs, ranked lists of connected users and shared data point views depending on what the investigation requires.
Use machine learning to scale
Manual investigation works when the data volume is manageable. When it is not, machine learning can surface patterns that no analyst would find by hand. A well-trained model learns from historical fraud decisions and suggests new rules based on emerging patterns in your data.
For fraud teams dealing with high volumes and limited analyst capacity, machine learning is where detection starts to scale. Rules stop the attacks you already know about. Machine learning surfaces the coordination you have not seen yet.
Already know what fraud rings are? Read how to catch the ones your transaction rules miss.
Fraud rings detection: guide
Fraud Rings Are Getting Harder to Catch
Low-effort attacks are in retreat. What remains is more deliberate: coordinated rings using synthetic identities, dormant account tactics and residential proxies designed to look like legitimate traffic.
No single account in a fraud ring triggers a rule. The network is the problem and rules are not built to see networks.
The teams catching rings before the damage is done are not working harder. They have better signal coverage and the infrastructure to connect it.
See how Tradeify identified coordinated fraud rings that manual processes would have missed.
Read the Case Study
FAQ
A fraud ring is simply a group of fraudsters sharing resources to commit fraudulent acts. It is hard to distinguish between fraud rings and one fraudster targeting companies under multiple aliases. However, once apprehended, it often becomes more clear whether you were dealing with one person or multiple accomplices by looking at the methods they’re using.
There are as many types of fraud rings as there are types of fraud. Over the years, authorities have caught fraud rings specializing in romance scams, account takeover, and SIM jacking. What they all have in common is that they pool resources to coordinate and automate attacks at scale.
Like multi-accounting, you can detect fraud rings by identifying patterns in your fraudulent users. It may be that they often hide behind the same VPN or use a rotation of similar devices. In one of our use cases at SEON, we found that similar email addresses and ISPs could point to fraud rings, for example.