What Is a Mobile Proxy?
A mobile proxy is a gateway that assigns a device mobile IP address rather than a residential IP or a VPN. In other words, mobile proxies make it look like their user is connected to the internet via a mobile data network, masking their real address.
This seems like a small variation on residential proxies but, due to mobile data network architecture, results in major under-the-hood differences that make mobile proxies much more likely to be utilized by fraudsters and scammers who are looking to commit unlawful or illegal acts online.
It should be noted that mobile proxies are called that because they use the IP address of a mobile network. They are not necessarily run on nor assigned to mobile phones or any other mobile device.
Similarly, a mobile device such as a smartphone does not have a mobile IP if it’s connected to a residential network (for instance, when connecting from a home Wi-Fi.)
How Do Mobile Proxies Work?
As with residential proxies, mobile proxies use gateway software on any type of device to assign a specific type of IP to this device – an IP that belongs to a mobile data network.
In order to access the internet, a mobile device will first connect to a mobile cell tower, where it will be given an available IP. Several mobile IPs belonging to the same network will connect through the same tower.
It is possible to use a mobile proxy from a device that is not a mobile phone or tablet. This can happen as long as the proxy uses mobile hardware that enables their device to read a SIM card. For instance, this can be a mobile dongle.
Since mobile IPs are assigned by the mobile network carrier, they have access to all IP addresses associated with this carrier, which number in the thousands and tens of thousands.
However, an integral characteristic of mobile proxies is that the IPs they assign are not unique, which can work to the advantage of anyone looking to hide their intentions online.
Mobile proxy types include 4G and 5G mobile proxies, as well as rotating and dedicated mobile proxies.
How Are Mobile Proxies Set Up?
There are two primary methods to create a mobile proxy:
- Proxy providers create software, installing which makes a device into a mobile proxy node. This is usually intentional, although it is possible to be running a proxy node without knowing it.
- SIM card farms, after accumulating several SIM cards, set up proxies using mobile data dongles and appropriate software.
Once set up, each of the above is then sold to anyone interested in accessing the internet through a mobile proxy, or even hired in exchange for goods or services, often illegitimate.
Are Mobile Proxies Different from Other Types of Proxy?
Yes, mobile proxies have some marked differences from other types of proxies, which all come from the way cell carriers assign IP addresses to mobile devices.
All of the below are methods of masking one’s internet location/IP address. But how do they compare to each other?
| Residential Proxy | VPN | Mobile Proxy | Tor | |
| Assigned IP type | Residential IP, assumed to be provided by a land-based traditional ISP | Static, non-unique | Mobile IP, assumed to be provided by mobile network | The end node’s IP |
| Proxy detectability | Medium-hard to identify as a proxy | Easy to identify as a proxy (known addresses) | Almost impossible to identify as a proxy | Moderately easy to identify (lists of known end nodes) |
| Uniqueness | Can request a dedicated IP, if needed | Can request a dedicated IP, if available | Can never be unique or private (IP address is always shared with others) | Cannot be unique (exit nodes ever-changing and shared with others) |
| IP reputation | Varies by residential proxy type | Medium IP reputation | Best IP reputation | Low IP reputation |
As you can see from the comparison table, there are clear differences between different types of proxies, including residential proxies, mobile proxies, VPNs and onion routing such as with Tor.
Why Are Mobile IPs Assigned Differently?
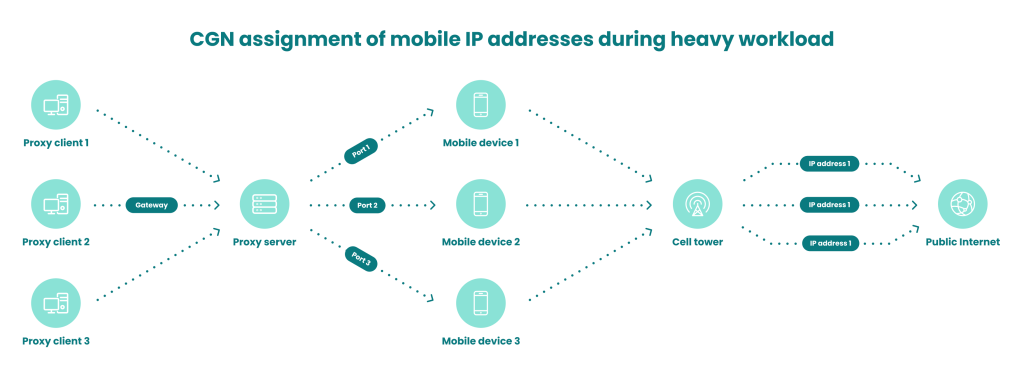
Because of the nature of the architecture of mobile data networks, they do not assign one IP address to each individual device.
During times of heavy workload, they will assign the very same IP address to several mobile devices – dozens, or even hundreds, depending on the mobile network. This is due to IPv4 shortage, and the carrier-grade NAT technology (CGN) used to address this issue on mobile data networks.
One example of this calculates that in 2019, when Vodafone had 17.2 million active subscribers in the UK, it had a total of just 131,000 IP addresses available. These were shared between all 17.2 million of Vodafone’s users.
In other words, up to 131 users could have been sharing the same IP address when the network load was high. These figures change with time but the general idea remains:
On mobile data networks, hundreds of different devices are being assigned the very same IP address. And this is what makes mobile IPs so unlikely to be banned by websites, as well as so useful to fraudsters.
Nobody wants to risk banning so many users because one of them could potentially be a criminal, so they will not ban someone based on their IP, no matter how they are acting.
Naturally, fraudsters are eager to take advantage of this…
How Are Mobile Proxies Used in Fraud?
Mobile proxies can be used by tech-minded fraudsters to evade detection and falsify their location when they are attempting any type of fraud at all, from card testing and arbitrage to auction fraud and beyond.
Mobile proxies are a tool to help fraudsters hide rather than a method to achieve fraud, constituting part of their OPSEC.
This is primarily due to the technical particularities of mobile proxies, which we outlined above. Since websites and online services are well aware that dozens (if not hundreds) of users can share the same IP but have nothing else in common apart from their mobile carrier/mobile proxy provider, they are unlikely to ban any mobile IPs outright because they would be stopping legitimate users from accessing their services and content – or worse, the buyers of their products.
How Can You Stop Mobile Proxy-Enabled Fraud?
Nobody wants to risk taking down dozens of well-meaning, legitimate consumers by banning a mobile IP, no matter how one of the devices that use it conducts itself.
And this is why fraudsters are more likely to get away with it if using mobile proxies, creating problems for those who use traditional anti-fraud tactics.
However, sophisticated anti-fraud protection goes beyond only looking at the IP and thus enabling fraudsters who use mobile proxies to circumvent one’s measures. Simple IP reputation filtering is not adequate protection.
Instead, IP analysis is one of several data points that should inform the assessment of risk that each user could pose. For instance, velocity checks add the dimension of time, while proxy detection tells us how likely each user is to have arrived through a proxy in the first place.
Combined with additional information also gathered via fingerprinting tools, all of these will constitute parameters that will form the answer to the simple question “How dangerous could this user be and what do I need to ask them to decide to trust them?”
You can use SEON’s IP lookup tool to get useful information about any IP, including mobile IPs.
Sometimes, the answer will involve a hard KYC verification check. Sometimes, the outcome will be outright banning.
And many other times, users with legitimate, lawful intentions will be allowed to continue with minimal disruption and friction.
Importantly, such a tactical approach treats users on an individual basis instead of penalizing those who use advanced technology without having bad intentions. This way, fraudsters using mobile proxies are deterred, at minimal cost to legitimate users – and to the business.
Fraudsters do their best to hide their identity with proxies. How do you catch them? Device fingerprinting detects Tor, emulators, VPNs, mobile & datacenter proxies, and more.
More Information
Sources
Nirsoft: Major IP Address Blocks For Hungary
ipinfo.io: AS25135 – Vodafone Limited IP Address Ranges