What Is Account Takeover (ATO)?
Account takeover (ATO) is a form of fraud in which a criminal gains unauthorized access to someone else’s account to steal funds, commit fraud in the account holder’s name, or use the compromised access as a foothold for further attacks.
ATO affects accounts across banking, e-commerce, iGaming, and corporate systems. For individuals, the consequences include unauthorized financial transactions and loss of sensitive data. For businesses, a compromised staff account can give attackers access to internal systems, enabling them to launch phishing campaigns against colleagues, commit payment fraud, or move laterally through the organization.
How Does Account Takeover Work?
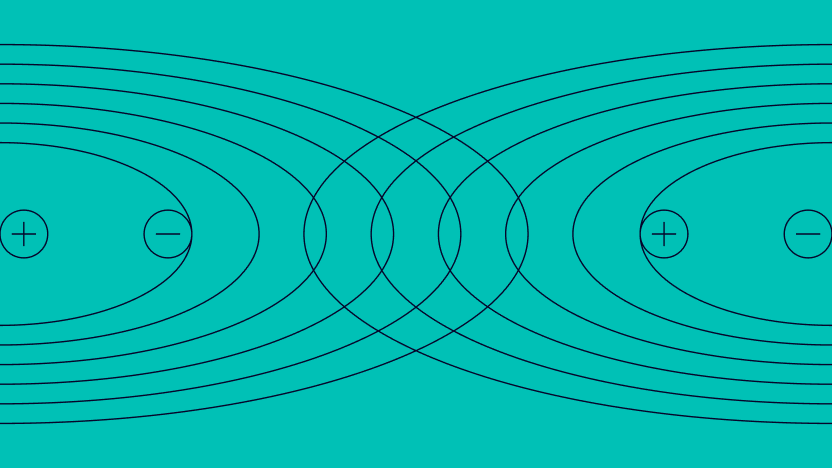
Fraudsters use a range of techniques to obtain valid credentials or bypass authentication controls:
- Phishing: The fraudster tricks the target into providing login credentials via a fake email, SMS, or website designed to mimic a legitimate service.
- Credential stuffing: Lists of username and password pairs from data breaches are tested automatically against target accounts using bots at high speed and scale.
- Brute force: Automated tools systematically attempt password combinations until one succeeds, particularly effective against accounts with weak or reused passwords.
- SIM swapping: The fraudster convinces a mobile carrier to transfer the victim’s phone number to a SIM they control, intercepting SMS-based two-factor authentication codes.
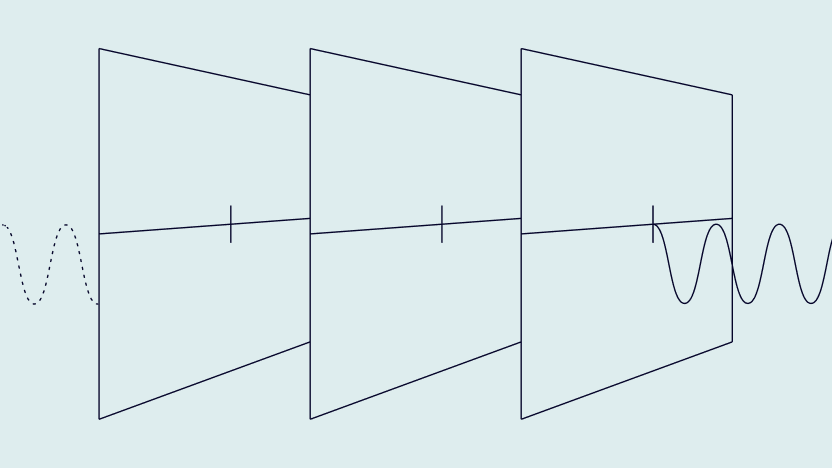
- Malware and keyloggers: Software installed on the victim’s device captures credentials as they are entered.
- Session hijacking: Stolen browser cookies are used to access an already authenticated session without needing a password.
Account Takeover vs. Identity Theft: What’s the Difference?
Account takeover is limited in scope: the fraudster gains access to one or more existing accounts. Identity theft is broader, involving the use of a victim’s full identity to open new accounts, obtain credit, or access services in their name. ATO is faster to execute and typically monetized quickly. Identity theft takes longer but tends to cause more lasting damage and is harder for victims to fully resolve
The Business Impact of Account Takeover
Account takeover causes direct financial losses, operational disruption, and reputational damage across every industry that manages user accounts. For financial institutions, ATO enables unauthorized transfers and loan applications. For e-commerce platforms, it results in fraudulent orders and chargeback liability. A single compromised corporate email account can serve as a launchpad for social engineering attacks targeting an entire organization.
In the UK alone, over 78,000 account takeover cases were recorded in 2025, making up 18% of all fraud-risk filings, a 6% rise year on year. Globally, businesses lose an estimated $20–40 billion annually to AI-powered fraud and impersonation attacks, of which ATO is a primary driver. According to SEON’s analysis of US cybercrime data, Americans reported $16.6 billion in cyber-enabled losses in 2024 alone, a 33% increase on the previous year.
Industry Use Cases for Account Takeover
Banking & Fintech: Unauthorized Transfers
Bank ATO attacks target accounts to initiate unauthorized wire transfers or change registered payee details. Fraudsters increasingly bypass two-factor authentication via social engineering to obtain one-time passcodes, making behavioral and device signals an essential secondary detection layer beyond authentication alone.
iGaming: Account Hijacking for Funds and Bonuses
Fraudsters target iGaming accounts to drain stored balances, withdraw loyalty points, and exploit promotional credits. Accounts with established histories are also sold on dark web markets. Platforms detect ATO through behavioral monitoring that flags sudden changes in login location, device profile, or activity patterns.
Corporate Environments: Business Email Compromise
A compromised employee email account gives attackers access to internal communications, enabling them to impersonate executives for fraudulent payment requests, move laterally to other internal systems, or launch targeted phishing campaigns against colleagues or customers.
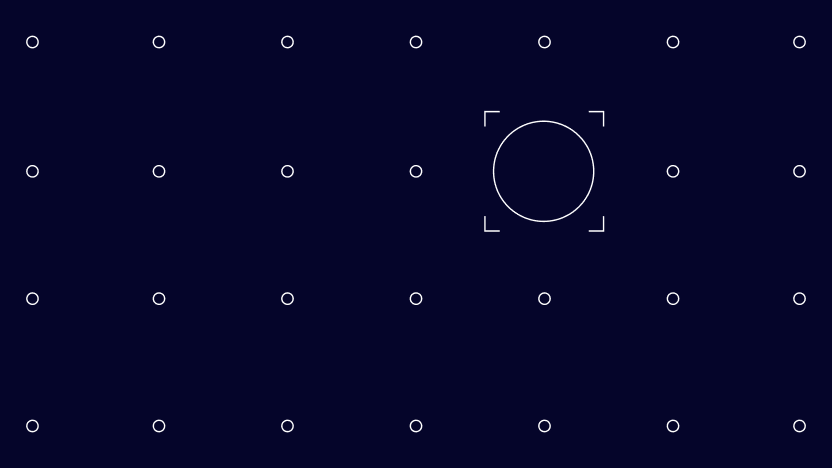
How SEON Helps with Account Takeovers
SEON’s Device Intelligence and login monitoring detect ATO attempts by flagging logins from unfamiliar devices, suspicious IP addresses, and behavioral patterns inconsistent with the account holder’s established history. Velocity rules identify credential stuffing attacks by detecting abnormally high failed authentication rates across accounts in a short window.