What Is a Man-in-the-Middle Attack?
Also shortened to MitM attacks, man-in-the-middle attacks involve hackers and cybercriminals intercepting communications and data transfers. Particularly prevalent on public and insecure Wi-Fi networks, they often target confidential information such as login credentials, bank details and private conversations.
Man-in-the-middle attacks are surprisingly common and disturbingly simple to carry out. There are even walkthrough-style tutorials on YouTube. An IBM study suggests that 35% of “exploitation activity” involves man-in-the-middle attacks.
One particular characteristic of man-in-the-middle attacks is that they frequently go undetected. Victims may be unaware that their details have been compromised until they suffer from payment fraud or other issues.
How Do Man-in-the-Middle Attacks Work?
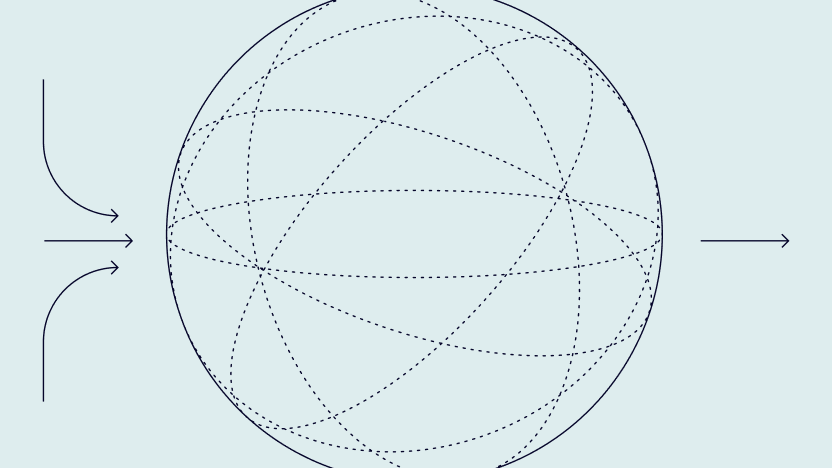
A good way to visualize a man-in-the-middle attack is as an incident of digital eavesdropping, where the attacker is trying to intercept information for various purposes.
Typically, a cybercriminal would:
- set up a packet sniffing tool, often operating at a low level on the network
- intercept data flowing along a certain path – for example, between an individual’s laptop and a remote host, such as a website or corporate system
- record and take advantage of this data in various ways, e.g. for identity theft, account takeovers, etc.
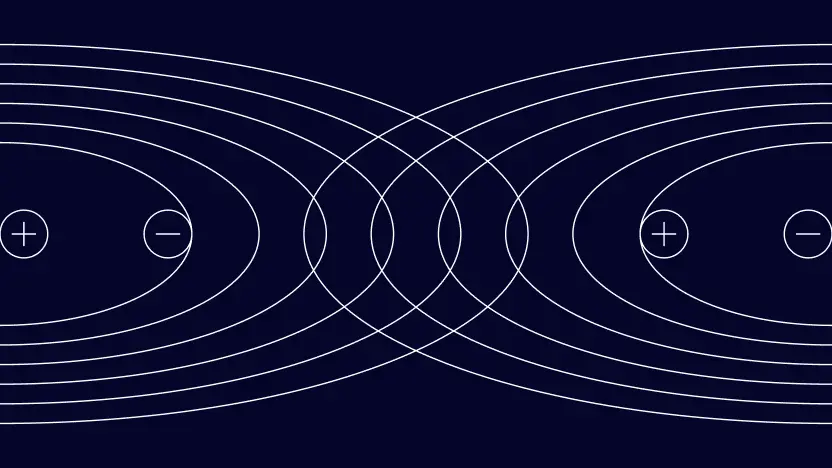
Alternatively, a hacker may intercept a communication by spoofing, which would mean essentially impersonating a legitimate device or server.
One example of spoofing involves the use of rogue wireless access points:
- A hacker sets up a rogue wireless access point using the same SSID (network name) as a legitimate wireless network, such as a public network or one in a café or hotel.
- Unsuspecting members of the public connect to that network instead of the genuine network, from where they are forwarded to the internet.
- Though the victim manages to connect to the websites they were looking to access, the hacker intercepts this traffic as a MitM, including passwords and other sensitive information.
Cybercriminals may employ various other techniques, such as compromising DNS servers to reroute traffic, redirecting people to fake websites, or accessing web cookies containing sensitive information.
Types of Man-in-the-Middle Attacks
Types of man-in-the-middle attacks include:
- IP address spoofing: Often combined with fake websites, this type of attack can lead a victim to think they’re interacting with a legitimate party when they are, in fact, providing information to a hacker.
- SSL and HTTPS exploits: These attacks employ various techniques based around abuse of the SSL certificates that lead people to believe they’re interacting with a secure website. Hackers may, for example, hijack an HTTPS redirection to a secure server of their own.
- Fake Wi-Fi: This common type of man-in-the-middle attack involves the setup of a fake Wi-Fi network that poses as a legitimate one in a café, hotel or other public location. 87% of people use public Wi-Fi, with the majority assuming their data is secure – but that’s often not the case without the use of additional precautions.
- Email hijacking: This form of man-in-the-middle attack involves a cybercriminal gaining access to (or successfully spoofing) legitimate email accounts. They can then use social engineering attacks to interact with individuals who believe they’re dealing with a genuine company or person.
- Browser cookie theft: Browser cookies often contain private information such as name and address details, and possibly login credentials. By gaining access to these cookies, hackers can pose as their victims – placing orders, gaining access to online accounts, and committing financial fraud.
Why Are Man-in-the-Middle Attacks Dangerous?
MitM attacks enable a huge range of other types of fraud, including credential stealing, account hijacking, account takeover fraud, carding, identity theft, and so on. Both companies and individuals can be affected.
Man-in-the-middle attacks are popular with fraudsters because they can be carried out at scale with a minimal risk of detection. For example, a hacker can set up in a café or within Wi-Fi range of a hotel, collect data and disappear.
Sophisticated attacks also fail to raise suspicion from victims. IP or DNS spoofing, for example, accompanied with a convincing banking or ecommerce website, could lead somebody to enter card details or login information without hesitation.
Consequences of MitM Attacks
Man-in-the-middle attacks can have consequences that include data breaches, financial loss, and reputational damage to companies.
Several high-profile data breaches and cyber attacks have involved man-in-the-middle tactics. They include the headline-making Equifax breach of 2017. In 2011, a digital certificate issuer in The Netherlands, DigiNotar, suffered a man-in-the-middle attack that ultimately resulted in the company’s bankruptcy.
A man-in-the-middle attack on an individual can have knock-on effects for an entire organization.
A hacker who successfully intercepts login credentials to a corporate system can use these as the basis for further cybercrimes. For example, they could introduce a worm to a corporate network, or use access to email for phishing or CEO fraud.
How to Protect Against Man-in-the-Middle Attacks
Companies can deploy endpoint protection and make use of mobile device management (MDM) to reduce the risk of man-in-the-middle attacks. For example, they may choose to restrict use of public Wi-Fi networks, or even lock down access to unknown or insecure websites.
However, protecting from the ever-present risk of man-in-the-middle attacks often comes down, primarily, to awareness and the minimization of human error. Companies should ensure that all employees are aware of the following basic precautions as part of their cyber training programs:
- Use of VPNs on public Wi-Fi: VPN services encrypt all traffic between a device and the websites and online services that that device is accessing. This can protect against packet sniffing, both on questionable networks and legitimate networks shared with others.
- Exercising caution using public Wi-Fi: It’s important to check which network to use in any public place, such as a hotel or coffee shop.
- Checking for HTTPS: It’s crucial that people know to check for browser padlock icons that demonstrate a website is secure, especially on any website that requires the submission of personal information.
- Caution around emails and websites: Often, a man-in-the-middle attack originates from human error, such as clicking a link in a phishing email or downloading something from a malicious website. Cyber awareness and extreme skepticism can help to prevent this.
- Cybersecurity software: Good quality and up to date antivirus and antimalware can help to detect issues that may facilitate a man-in-the-middle attack.