In 2024, anti-money laundering (AML) violations led to a staggering US$3.3 billion in fines from just eight cases, highlighting the high stakes of non-compliance and underlining the importance of good business practices.
This guide outlines 10 crucial steps to help businesses navigate the maze of AML requirements, reduce the risk of hefty penalties and protect customer trust.
What Is an AML Checklist?
An AML checklist is a structured list of actions, controls, and procedures that help businesses comply with anti-money laundering regulations. It ensures organizations can detect and prevent illicit activities like money laundering, terrorist financing, and financial fraud. AML checklists are essential for regulated industries such as banking, fintech, crypto, and online gambling, and help companies meet requirements set by bodies like FATF, FinCEN, and the EU.
A typical AML checklist includes customer due diligence (CDD), enhanced due diligence (EDD) for high-risk clients, ongoing AML transaction monitoring, sanctions screening, suspicious activity reporting (SAR), proper recordkeeping, staff training, and periodic audits. It streamlines compliance efforts, reduces regulatory risk, and ensures businesses stay audit-ready and protected from reputational damage.
9 Steps to Better AML Checklists
This AML checklist outlines key actions and procedures organizations must follow to detect, report and prevent money laundering risks. It helps maintain a robust AML program, reduce the chances of being involved in illegal activities and stay compliant with relevant laws and regulations.
1. Assess Industry Risk
Chances are that if you’re on this page, you’ve already been asked to meet AML requirements. But just to recap, here are the key industries where this will be needed:
- Money service businesses: A money service business, or MSB, is a legal term for businesses that transmit or convert money. It includes banks and financial institutions, as well as foreign currency exchanges and post offices.
- Real estate agencies: Criminals use real estate agencies to purchase property assets, usually hiding behind complex company structures. Governments have implemented strict AML regulations to ensure commercial or personal properties aren’t sold to money launderers.
- High-value dealers: Companies whose cash payments average above $10,000 or more in exchange for goods.
- Trust or company service providers (TCSP): Companies involved in a range of services and activities for their customers, including acting as a director or secretary, providing a registered address, acting as a trustee, etc.
- Accountancy sector: Accountants would be the first ones to know if the source of funds from their clients appears illegitimate. Governments go straight to the source by targeting them with AML compliance.
- Art industry: The art market is attractive to money launderers. Art dealers and other participants must put controls in place to ensure they remain compliant.
2. Appoint an AML Compliance Officer
A dedicated AML Compliance Officer ensures regulatory compliance, oversees risk assessments, and trains employees to identify suspicious activities. Without centralized oversight, compliance efforts can become fragmented, leading to monitoring and reporting gaps.
This role is responsible for overseeing the implementation of compliance policies, conducting risk assessments and ensuring that all employees are properly trained to identify suspicious activities.
3. Develop a Comprehensive AML Policy
A strong AML policy sets clear guidelines for preventing, detecting and reporting suspicious activity while establishing an operational framework to ensure compliance across the organization.
- Run a risk assessment: Identify and evaluate the specific money laundering risks the business faces based on factors such as customer profiles, transaction types and geographic exposure.
- Create processes for transaction monitoring and reporting: Implement systems to detect suspicious activities, define escalation protocols, and ensure timely reporting to regulatory authorities.
- Plan and conduct employee training and audits: Provide ongoing AML training for employees, enforce compliance standards and conduct regular independent audits to assess policy effectiveness.
- Implement Customer Due Diligence (CDD) procedures: Establish clear guidelines for verifying customer identities through background checks, including financial history, transaction patterns, business activities, and links to high-risk entities or jurisdictions. This ensures accurate risk assessment and helps detect potential connections to money laundering or other financial crimes.
- Conduct Enhanced Due Diligence (EDD) for high-risk customers: EDD requires additional verification for high-risk clients, including assessing the source of funds and monitoring transactions more closely. This proactive approach prevents exposure to financial crime and strengthens regulatory compliance.
By addressing these core areas, businesses can strengthen their defenses against money laundering, reduce regulatory risks and foster a culture of compliance. A well-structured AML policy not only protects the organization but also reinforces trust with customers and regulators.
4. Establish Ongoing Transaction Monitoring
The biggest weakness of AML systems is that they can be easily fooled. Fraudsters and criminals often know how to bypass standard checks, using stolen or fake identities to slip through compliance measures.
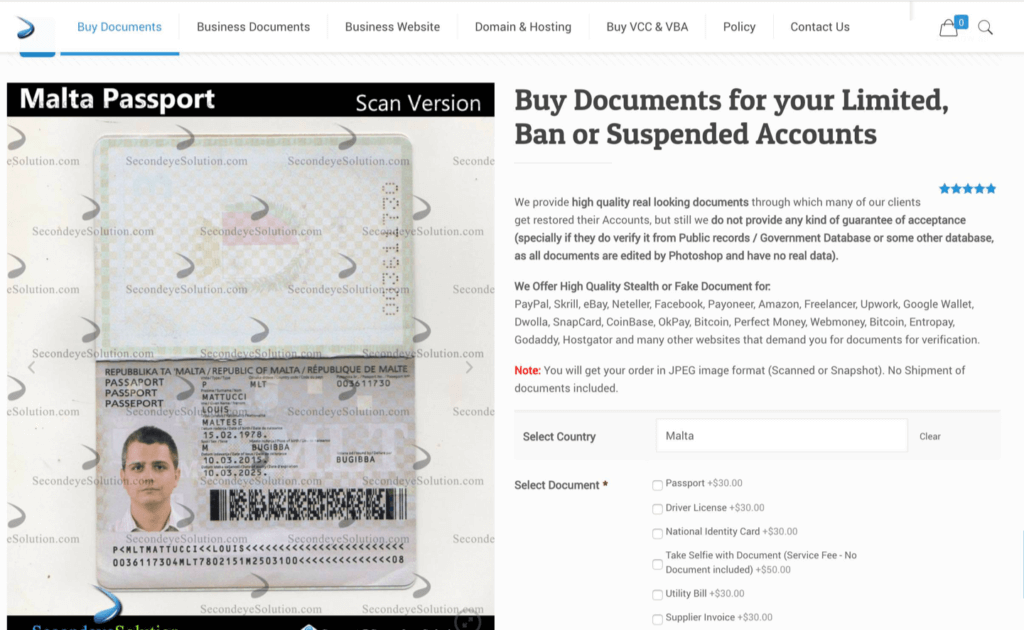
Relying solely on traditional verification methods can result in blind spots, leaving businesses vulnerable to money laundering risks. To counteract this, organizations must layer in additional methods to validate customer information and detect inconsistencies before they lead to financial or regulatory consequences.
Ongoing transaction monitoring and digital footprint analysis provide crucial context about who customers really are and whether their claims match their behavior. By continuously assessing transactional patterns and analyzing alternative data points — such as IP addresses, email histories, device types, and geolocation — businesses can uncover discrepancies that standard identity checks might miss. This approach ensures that suspicious activities are flagged in real time, allowing compliance teams to intervene before threats escalate.
Rigid AML checks can turn away good customers. SEON uses alternative data and smart scoring to reduce false positives and stay fully compliant.
Ask an Expert
5. Use Behavior Analysis
Think like a money launderer — because that’s exactly who you’re up against. What patterns would you exploit? How would you avoid detection? Behavior analysis helps you flip the script, revealing anomalies that traditional AML checks often miss.
With custom risk rules and behavioral signals, you can flag activity that strays from the norm. Watch for red flags like:
- Frequent logins from unrelated IPs or geolocations
- Repeated device or browser changes
- A surge of low-value deposits in a short timeframe
- Multiple users sending identical amounts to one recipient
- Transactions that don’t fit a user’s typical behavior
By layering these insights into your AML strategy, you’re not just reacting—you’re staying one step ahead. It’s a smarter, more proactive way to uncover hidden risks and go beyond regulatory checkboxes.
6. Report Suspicious Activities Promptly
Suspicious Activity Reporting (SAR) is a mandatory process under AML regulations where businesses must report suspicious financial activities to relevant authorities. Failure to do so can result in severe penalties, including fines or criminal charges. To comply effectively and prevent financial crimes, it’s essential to establish a streamlined approach for identifying, escalating, and reporting suspicious activities. Here are key elements to ensure prompt and accurate reporting:
- Establish clear reporting procedures: Create detailed, step-by-step protocols that employees can follow when identifying suspicious activities. This ensures speed and consistency by reducing confusion and errors in the reporting process.
- Provide regular trainings: Equip employees with the knowledge to recognize red flags and understand the reporting process. Ongoing training helps them stay alert and responsive to emerging risks.
- Ensure timely reporting: Report suspicious activities as soon as they are identified to meet legal obligations and avoid potential penalties. Prompt reporting is a key step to prevent illicit activity and avoid harm.
- Review and update procedures regularly: Audit and update reporting procedures to keep up with changing regulations and threats. This helps maintain an effective compliance framework that can adapt to evolving risks.
7. Maintain Comprehensive Records
Keeping detailed and up-to-date records is vital for AML compliance. These records should include transaction details, customer information and any communications related to suspicious activities.
Comprehensive record-keeping helps facilitate audits, investigations and compliance reporting while also serving as a critical tool for identifying potential patterns of money laundering.
Records must be retained for a specified period, typically five years, depending on jurisdiction. Regular audits should be conducted to ensure that all necessary documents are present and properly maintained.
8. Provide Regular Employee Training
AML compliance is only as effective as the people enforcing it. Regular, targeted training ensures that employees are up-to-date on the latest regulatory requirements and understand how to identify and report suspicious activities. A strong training program empowers staff to act confidently and consistently in compliance with AML policies.
Effective training should include both general compliance education and scenario-based exercises that help employees recognize red flags in real-world contexts. Ongoing education is essential, as regulations and money laundering tactics evolve. By fostering a culture of compliance through regular training, you ensure that your team is always at the ready.
9. Conduct Regular Independent Audits
Independent audits are essential for assessing the effectiveness of your AML program. These audits provide an objective evaluation of your processes, policies and overall compliance efforts. By conducting regular audits, organizations can identify areas for improvement, update procedures and ensure they are meeting regulatory standards.
Audits not only assess compliance but also provide an opportunity for internal teams to learn and improve. By reviewing processes with an external or independent auditor, businesses can gain fresh perspectives and catch any potential gaps in their compliance strategy.
How to Augment Your AML Checklist With SEON
SEON is a flexSEON is a flexible fraud prevention and customer intelligence platform designed to supercharge your AML processes with real-time insights and modular tools.
Whether you’re tightening compliance or scaling up, SEON gives you the flexibility to build the right solution for your needs.
- Smarter identity verification: Go beyond basic checks. Screen users against global watchlists, crime databases, PEPs and more. Verify identities using digital footprint analysis and filter out bad actors before they can do harm.
- Real-time transaction monitoring: Set custom thresholds and flag high-risk behavior instantly. Whether it’s a suspicious transaction pattern or a high-value transfer, SEON alerts you the moment something is amiss.
- User profiling for better investigations: Capture and log detailed customer data to support SARs and other compliance reporting. SEON helps your compliance team work faster and smarter, with enriched user profiles and real-time alerts that highlight high-risk activities for manual review.
AML Checklist FAQ
AML requirements are set by governments to ensure businesses do not help money laundering. They include a form of identity verification, PEP and sanctions check, and transaction monitoring.
An AML policy must be stated on your company website or in communications with customers. See our articles for a complete AML policy template.
A SAR, or Suspicious Activity Report, must be submitted to authorities when you suspect you may be dealing with money laundering. See our article for a downloadable SAR template.
Learn more about: