In a world where fraud is constantly evolving, data analytics and predictive models have become essential for proactive fraud detection. These tools enable businesses to spot hidden patterns and anticipate fraudulent activities, moving beyond reactive measures.
According to the Association for Financial Professionals, 79% of organizations faced payment fraud attempts in 2024. This guide will walk you through the principles of fraud analytics, helping you uncover threats that might otherwise go unnoticed.
What Is Fraud Analytics and Why Does It Matter?
Fraud analytics is the practice of using data analysis techniques to detect, investigate and prevent fraudulent activities. It involves examining large datasets to uncover suspicious patterns and flag anomalies that may indicate fraud. Organizations can perform this analysis manually, but most rely on automated systems powered by machine learning, which can process vast amounts of data at speed and scale.
In a digital world where fraudulent tactics are becoming increasingly sophisticated, fraud analytics is essential. It allows businesses to proactively identify and mitigate risks, combining insights from transaction data, user behavior and other relevant sources. By leveraging advanced analytics, companies can not only prevent financial losses but also maintain customer trust and ensure compliance with regulatory standards.
Learn how our technology is an integral part of the leading neobank’s financial risk management strategy.
Read the case study
The Role of Data Analytics in Fraud Prevention
Fraud analytics is a critical component of any comprehensive risk management strategy. By leveraging data analysis, businesses can proactively identify and assess risks they may not have anticipated. Patterns and anomalies revealed through analytics can highlight emerging threats, from identity fraud and payment chargebacks to multi-accounting and bonus abuse.
Beyond just detection, fraud analytics helps optimize resource allocation, ensuring that your risk management team can focus on the most critical areas. It also provides continuous insights to refine your existing defenses, making it easier to adapt as your business evolves, whether you’re launching new products or expanding into new markets. For organizations with lean risk teams, these tools can dramatically reduce manual workloads and boost efficiency.
Traditional methods miss today’s threats. Learn how to fight fraud with smarter tools.
Lean more
How Do Modern AML Programs Use Data Analytics to Detect Suspicious Activity?
Modern Anti-Money Laundering (AML) solutions have evolved significantly, leveraging advanced data analytics to identify and mitigate suspicious financial activities more effectively. Traditional rule-based systems are increasingly being supplemented or replaced by sophisticated analytics techniques, including machine learning and AI, to enhance detection capabilities and reduce false positives.
These advanced analytics tools process vast amounts of transactional data in real time, identifying patterns and anomalies that may indicate money laundering activities. For instance, machine learning models can analyze historical transaction data to predict potential risks, enabling organizations to address threats proactively. Additionally, network analysis techniques, such as graph analytics, are employed to uncover complex relationships and transaction patterns that traditional methods might overlook.
By integrating these data-driven approaches, AML programs can more accurately detect suspicious activities, streamline compliance processes, and adapt to financial criminals’ ever-evolving tactics.
Fraud Data Analytics Techniques
Fraud data analytics uses various techniques to detect suspicious activities, each serving a unique purpose. Here are the most effective data analysis techniques for fraud detection:
- Unsupervised Learning (Descriptive Analytics): Identifies outliers and unusual behaviors in data without prior labels, using methods like z-scores, breakpoints, peer group analysis and RFM (Recency, Frequency, Monetary value).
- Clustering: Groups similar entities to uncover hidden fraud patterns, making it easier to identify coordinated attacks or suspicious behavior.
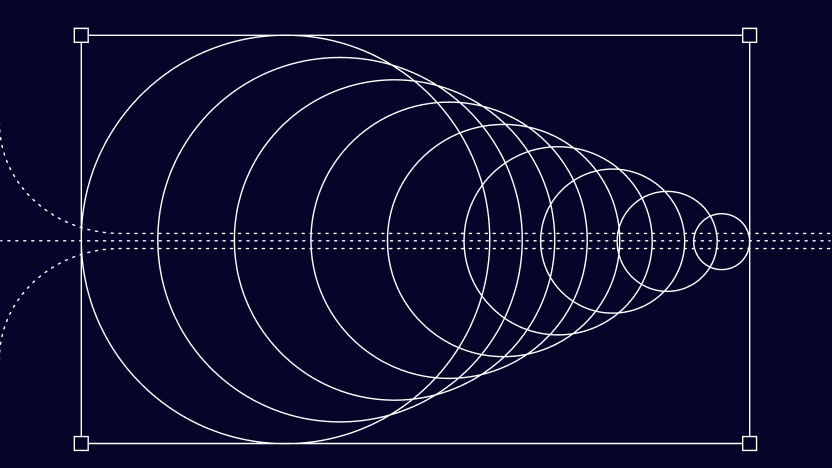
- Social Network Analysis: Maps connections between users based on data points (devices, IPs, emails), exposing fraud networks that may not be visible individually.
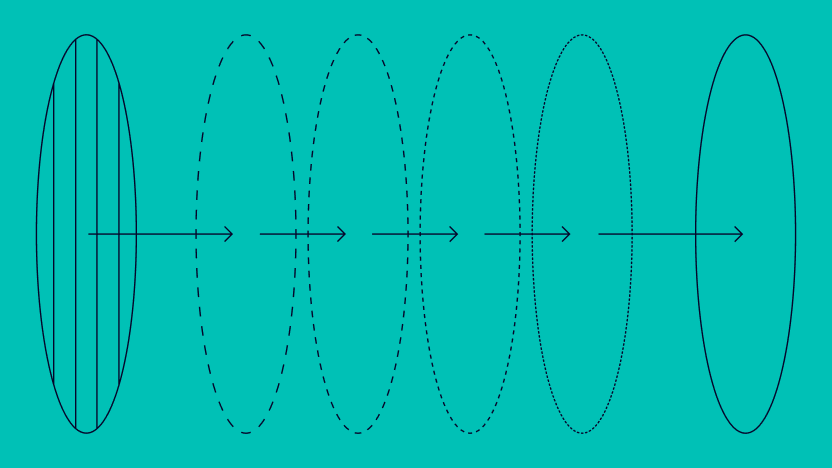
- Predictive Fraud Analytics: Analyzes historical data to forecast potential fraud incidents, enabling proactive prevention.
Building and Using Predictive Analytics for Fraud Detection
Predictive analytics is a powerful tool in fraud detection, enabling businesses to anticipate suspicious activities before they cause harm. It uses historical data to build models that flag potential fraud in real-time, ensuring a proactive approach. Here’s how you can leverage predictive analytics effectively:
- Data Labeling and Classification: First, categorize your historical data as fraudulent or legitimate. The labeled data serves as the foundation for training your predictive models.
- Identifying Key Fraud Indicators: Not all data points carry equal weight in detecting fraud. Analyze your dataset to identify variables that consistently correlate with fraudulent activity. Remove any data that adds noise without value.
- Developing Predictive Models: Use your labeled data and identified indicators to train your predictive model. This model can then analyze incoming data in real time, flagging risky actions based on established patterns.
- Implementation and Automation: Deploy your model by integrating it into your existing fraud detection system.
- Continuous Monitoring and Optimization: Fraud tactics evolve, so your model must be regularly monitored, tested and optimized. Adjust rules and retrain the model as new fraud patterns emerge, ensuring ongoing accuracy.
By following this approach, you can build a dynamic, self-improving fraud detection system that not only identifies known threats but also adapts to emerging ones.
How SEON Helps
SEON’s fraud prevention platform provides businesses with a sophisticated, adaptable approach to fraud detection, combining machine learning, digital footprint analysis, device intelligence and real-time monitoring to offer a comprehensive defense against evolving threats.
By leveraging machine learning, SEON’s models continuously adapt to new patterns, improving detection accuracy without manual intervention. Digital footprint analysis enables a deeper understanding of user behavior, while device intelligence assesses device attributes to identify suspicious connections in real time.
SEON also offers flexible risk management with a mix of preset and customizable rules, allowing businesses to tailor their fraud prevention strategies to their unique needs. Real-time monitoring ensures that potential threats are identified and managed immediately, while the Label API streamlines the process of marking fraudulent transactions, enhancing the precision of detection models. Together, these capabilities equip businesses with a proactive, data-driven approach to fraud prevention.
Frequently Asked Questions
It involves examining data to identify suspicious patterns, detect anomalies and uncover fraudulent activities using statistical methods, machine learning and real-time monitoring.
Predictive analytics uses historical data to identify patterns, build models and assign risk scores, enabling businesses to flag suspicious behavior before it leads to fraud.
Effective techniques include outlier detection, clustering, social network analysis and predictive modeling, each uncovering different aspects of fraudulent behavior.
Modern AML programs rely on data analytics to efficiently detect suspicious transactions, uncover hidden risks, and adapt to evolving fraud tactics with real-time insights.