What Is Customer Identity and Access Management?
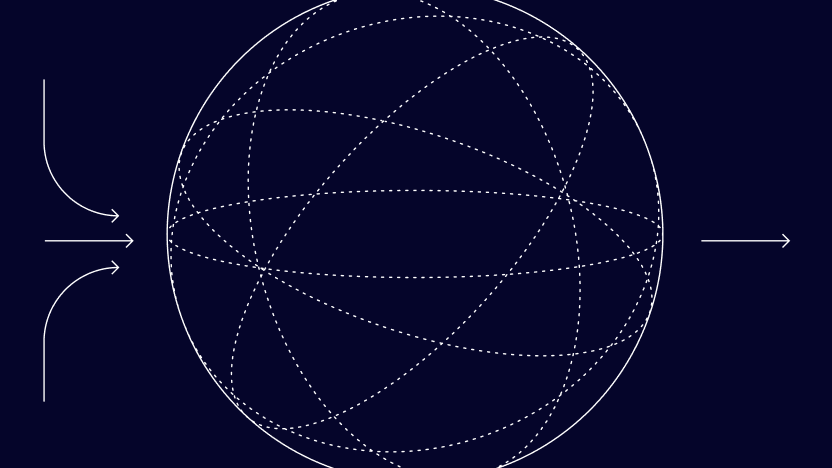
Customer identity and access management (CIAM) is a way for companies to provide millions of customers with easy, secure access to their digital properties. It helps companies reduce friction for users who are logging in to their applications. This delivers benefits to the users, in terms of an enhanced user experience (UX), as well as to the company, by reducing friction that might otherwise contribute to customer churn.
Both UX and data security sit at the heart of CIAM solutions. A well-implemented CIAM system means that users have to spend less time dealing with burdensome log-in procedures. Meanwhile, CIAM plays an important role in reducing the risk of account takeover (ATO) fraud – something that poor user password practices mean is an ever-present threat across the digital landscape.
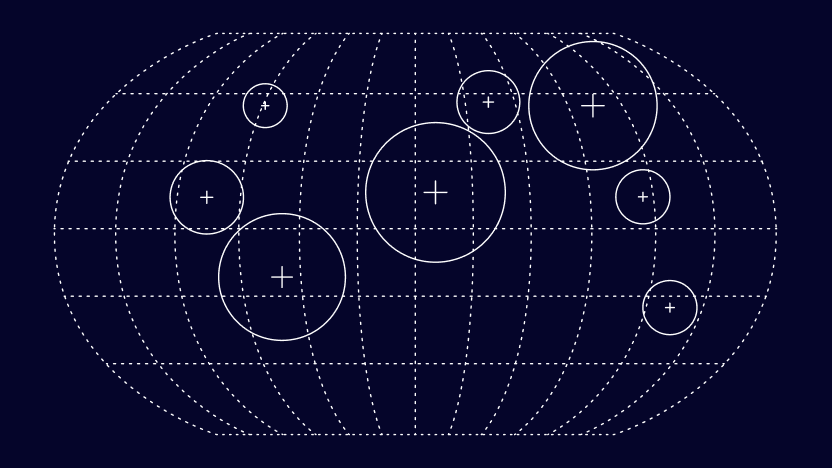
CIAM is also eminently scalable, enabling businesses to roll out slick authentication and authorization processes that can serve millions of customers. Part of this is down to the fact that CIAM solutions are self-serve for end users: Customers can change their privacy, security, and personalization settings themselves, without the need for an IT team’s involvement, thus enabling efficiency at scale.
The CIAM market is growing fast. Markets and Markets forecasts a compound annual growth rate (CAGR) of 15.3% between 2021 and 2026, as the global CIAM market increases from a value of $8.6 billion to $17.6 billion. The firm estimates that North America holds the highest market share.
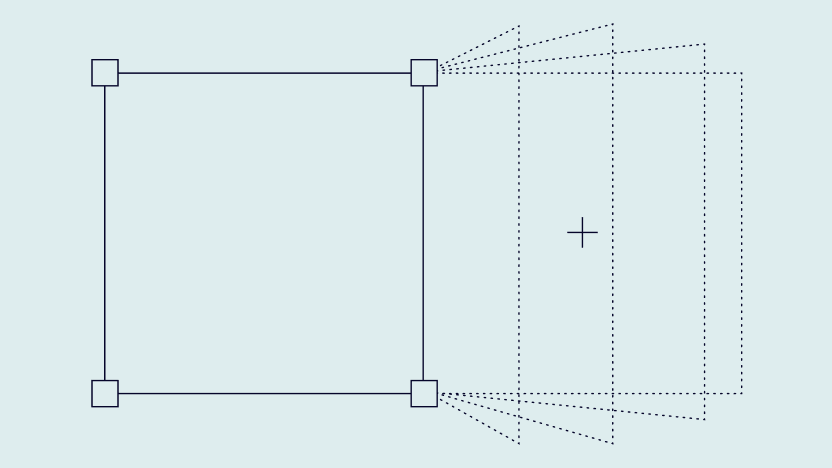
Businesses often use multiple providers and pieces of software to build up CIAM solutions that suit their particular needs, rather than building solutions in-house. While there are comprehensive CIAM offerings out there, a layered approach means that businesses can develop and evolve their solutions over time as they scale. In the process, they can choose only the features that they need.
CIAM is a form of identity and access management (IAM) that focuses on the user experience while also supporting robust security. We’ll dive into the differences between CIAM and IAM below.
Partner with SEON to reduce fraud rates in your business, stopping identity fraud, chargebacks, and account takeovers. Enable your growth.
Ask an Expert
How Is CIAM Different from IAM?
Identity and access management is about enabling the right internal users to access the right digital assets while preventing unauthorized access and fraud. Customer identity and access management is a subset of this that provides external users with significantly greater control and a superior UX. This is a fundamental difference between the two disciplines.
One key difference is that IAM solutions are designed to provide internal authentication and authorization, with strict barriers to access in place. CIAM solutions, meanwhile, need to lower those barriers in order to reduce friction.
The differences between CIAM and IAM become clear when we compare the two disciplines side by side.
| CIAM | IAM | |
| Capacity | CIAM is designed with users in mind. Millions of them. Solutions can handle rapid scaling and major traffic spikes. | Capacity generally tops out at 100,000 users, with less robust handling of traffic, including surges. |
| Intention | CIAM is intended to deliver a frictionless, comprehensive authentication and authorization experience for the end user. | IAM is mainly intended to achieve greater operational efficiency. |
| Scalability | Self-service and self-registration support robust scalability. | The need for company registration and interventions limits efficiency in terms of scalability. |
| Approach | CIAM is a comprehensive, accessible solution that’s designed based on an outside-in approach. | IAM is a closed system designed with an inside-out approach. |
| Users | Users can have multiple identities without any issues. | Users can only have a single identity. |
At the core of these differences is the intention behind the use of IAM versus CIAM. IAM tends to focus on employee access, while CIAM is concerned with customer identity and access. CIAM must, out of necessity, be a more scalable solution, as all businesses (at least, all successful businesses!) have more customers than staff.
How Does Customer Identity and Access Management Work?
In essence, CIAM solutions work by handling the administration of users’ identities while providing user privacy and consent management functionality. They also provide fraud detection and prevention functionality. Modern CIAM solutions are increasingly factoring in decentralized, self-sovereign identities as well.
Customer identity and access management solutions vary in terms of their features, with different businesses requiring different functionality. That said, most CIAM implementations include certain core features and functions when it comes to delivering customer authentication and authorization. These include:
- Single sign-on (SSO): Providing users with a single sign-on mechanism removes the friction involved in signing into multiple different digital assets. Microsoft and Google both ably demonstrate the value of SSO by enabling users to log in to multiple digital properties with a single sign-on.
- Bring your own identity (BYOI): The use of social logins achieves the same as single sign-on in terms of enabling users to log in to multiple digital properties with one process. A user who is logged into Facebook, for example, can use this to access various other sites without having to reenter their credentials.
- Multi-factor authentication (MFA): The use of MFA makes life harder for hackers. It also introduces friction for users. CIAM solutions can address this by taking a risk-based approach to MFA based on monitoring user behavior (known as adaptive authentication). If a user logs in from an unusual location or at an unusual time, for example, the CIAM system can trigger the MFA mechanism.
- Fraud detection: Behavioral monitoring can also serve to reduce instances of fraud. Unusual and suspicious behavior can be detected at an early stage, helping to minimize the harm caused by account takeovers and other forms of fraud.
- Consent and preference management: Giving customers more control over their data builds trust and customer satisfaction as part of the overall CIAM experience.
- Self-service account management: Part of what makes CIAM systems so scalable is that customers can manage their own accounts via automated systems and prompts. This means that the user can handle anything from changing a forgotten password to updating their preferences quickly and painlessly.
Access management, identity proofing and orchestration, directory services, and more can also fall under the remit of CIAM, depending on businesses’ needs.
In terms of implementation, many CIAM functions are delivered via application programming interfaces (APIs) and, for mobile apps, via software development kits (SDKs). This means that businesses can implement complex CIAM solutions with relative ease – assuming the API or SDK has been well-designed and documented.
Examples of Customer Identity and Access Management
We’ve mentioned three examples of how customer identity and access management works in practice above: Microsoft, Google, and Facebook. These examples show the value that CIAM systems can deliver in terms of delivering an enhanced user experience.
Let’s look at Google’s CIAM approach in a little more detail. All a user needs to do is log in to their Gmail account and they will be able to use Google Drive, YouTube, and other Google assets without having to log in to each digital property separately. This enhances the user experience significantly by removing multiple instances of friction from the user journey across Google’s digital assets.
Why Is Customer Identity and Access Management Important?
Customer identity and access management is important for end users and the businesses whose services they use. From a business perspective, a decent CIAM mechanism can keep customers happier while helping to detect and prevent instances of fraud.
From a user perspective, a slick customer identity and access management solution makes life easier. It can remove the frustration associated with inefficient authentication.
While this may seem a minor source of friction at first glance, research by CMO Council has shown just how irritating customers find authentication difficulties. The firm’s survey of 2,000 consumers spread across the US, UK, Canada, and Ireland found that 60% reported having canceled a transaction because of inefficient authentication.
Clearly, this has major implications for businesses looking to reduce their churn rates and drive up their customer satisfaction levels.
Businesses also rely on CIAM solutions for the security benefits they deliver. Interestingly, this is another area in which IAM and CIAM solutions differ: IAM solutions are more focused on defending core business systems from hackers, while CIAM solutions are concerned with protecting customers’ accounts from abuse.
Risk-based security is key to this. With CIAM in place, businesses can spot red flags that could signal account takeovers at an early stage. This can prevent fraudulent translations from taking place. Customer identity and access mechanisms can also prevent fraudsters from opening accounts, thanks to identity verification procedures such as digital footprint analysis.
As well as protecting customers from account takeovers, CIAM solutions can also support businesses to avoid data breaches. Given data breaches cost global businesses an average of $4.35 million in 2022, according to IBM, and cost US businesses an average of $9.44 million, this is certainly a major point in favor of CIAM solutions.
Partner with SEON to reduce fraud rates in your business with real-time data enrichment, machine learning, and advanced APIs.
Ask an Expert
Benefits of CIAM
There are multiple benefits to implementing CIAM processes, from enhanced security to superior customer experiences. Let’s look at some of the ways that businesses can benefit from CIAM solutions.
- Easy integration: Systems that enable customers to pay bills, manage their accounts, track orders, arrange returns, and more all benefit from the ease with which CIAM solutions can be implemented. The fact that CIAM processes are easy to integrate also means that they can be introduced seamlessly, with no impact on the user experience.
- Data protection: Companies are legally required to protect their customers’ data. However, customers don’t always do all they can to support this aim. Many reuse passwords across multiple sites, making life easier for hackers trying to work their way into customers’ accounts and companies’ systems. One of the benefits of CIAM is that its behavior-based monitoring can trigger the need for multi-factor authentication if the risk associated with a log-in attempt seems higher than usual. An example of this is if the user is logging in from a different location or using a different device.
- Building customer trust: CMO Council’s research found that 81% of consumers would seek out companies that use easy, secure identity verification processes. Businesses that implement such solutions are therefore doing much to build customer trust through the delivery of seamless customer experiences.
- Customer empowerment: Because CIAM solutions emphasize self-service, customers are empowered to manage their own accounts through automated functionality.
- Multichannel support: CIAM solutions can span a range of devices, from PCs and laptops to cellphones, tablets, and gaming consoles, further reducing friction from the customer’s perspective.
- Comprehensive analytics: Because CIAM systems monitor customer behavior, they can provide unique insights into that behavior. This data can drive business decisions around anything from monetization to retention strategies.
- Scalability: As mentioned above, CIAM solutions can serve millions of customers. This means that businesses that implement them can aim for the stars, confident that their customer identity and access management processes will function seamlessly no matter how large they grow.
In addition to the above, CIAM systems can also support businesses to meet regulators’ requirements in terms of data security and privacy. Let’s take a look at this last business benefit in a little more detail.
How Can CIAM Help Fight Fraud and Assist Compliance?
CIAM can fight fraud by monitoring customers’ behavior to look for risks and by addressing the challenges associated with poor password hygiene. It can also support compliance with regulatory requirements by adding robust security to onboarding and log-in processes.
There are plenty of security standards that organizations need to comply with these days. The Health Insurance Portability and Accountability Act (HIPAA), standards set by the International Organization for Standardization (ISO), Service Organization Control Type 2 (SOC 2), the General Data Protection Regulation (GDPR), and other regional requirements combine to create a challenging regulatory landscape for a wide range of businesses.
By introducing security measures through CIAM solutions, businesses can help ensure compliance with these standards without negatively impacting the customer experience.
The fact that CIAM systems protect customer data doesn’t only keep regulators happy: It can also support businesses to detect fraud and stop fraudsters in their tracks before they do any damage. Security Magazine reports that there are 24 billion username and password combinations available on the dark web.
With many customers reusing the same username and password combination for multiple sites, it’s staggeringly easy for hackers to undertake password-stuffing attacks on a large scale, particularly when botnets come into play.
CIAM combats this, helping to fight fraud through MFA log-in and social log-in mechanisms while using adaptive authentication to address any log-ins that are considered unusually risky.
All of this means that businesses can fight fraud and ensure regulatory compliance while minimizing friction through a user-focused approach. This combination of abilities means that organizations around the globe are embracing CIAM solutions.