What Is a Blended Threat?
A blended threat is an attack that combines a range of different malware or different types of attack (such as combining malware with social engineering). These combine to attack different vulnerabilities, often meaning that blended threats can deliver greater infection speed, severity and impact than individual threats.
The complexity and sophistication of blended threats can make it difficult to determine what the attacker is targeting and how. This makes it harder to defend against them.
What Do Blended Threats Include?
Blended threats usually include one or more forms of malware, from scareware and viruses to trojans and worms. Many take advantage of zero-day exploits, where the attacker targets a vulnerability of which the software vendor and antivirus programs are as yet unaware.
These attack forms are often combined with social engineering tactics such as phishing or lures to trick users into downloading malicious files.
By combining multiple tools, SEON allows you to detect bots and block their attacks from damaging your business.
Learn More
How Do Blended Threats Work?
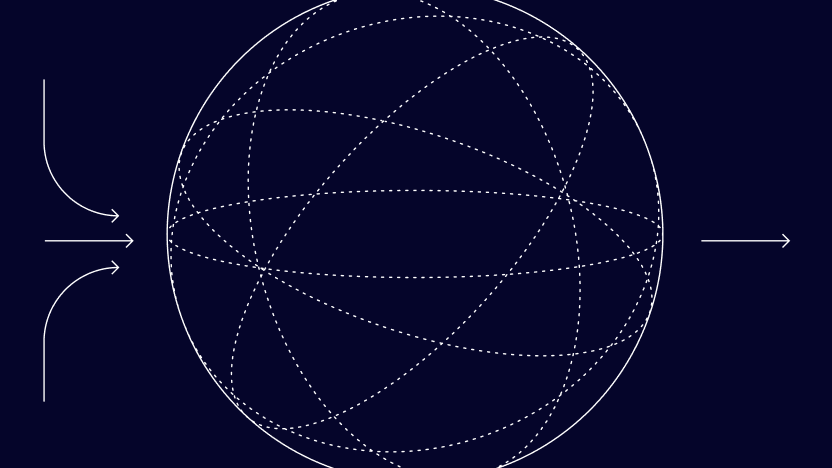
Blended threats work by attacking in multiple ways, from multiple directions, in an effort to overwhelm defenses or at least be more likely to find gaps. This means that they can be very sophisticated and very effective in terms of the harm that they do.
Blended threats work by creating confusion around where the primary source of the attack is and what it is intended to achieve.
In practical terms, each blended threat is different, but an example of how one might work is as follows:
- Phishing: The attacker attempts to compromise a business directly or via a partner company or application.
- Worm: The attacker tricks employees into opening a malicious file from an email or downloading it from a website. This allows a worm to spread through the company network.
- Botnet: The attacker uses a worm to access the system via a backdoor and creates a botnet.
An attacker can build an extensive botnet very quickly in this way. With that done, they have the power to launch devastating distributed DDoS attacks.
Examples of Blended Threats
Blended threats may be designed to bring down a company’s system, enable access to sensitive and confidential data, extort a ransom or achieve various other nefarious goals. Here are some real-life examples of blended threats:
Code Red
The Code Red virus is widely accepted as the first example of a blended threat, combining a self-propagating worm’s powers of infection with the ability to launch DDoS attacks. On July 15, 2001, it infected hundreds of thousands of computers and defaced websites, targeting enterprise networks.
Nimda
Another example of a blended threat is Nimda. The Nimda worm first surfaced in September 2001 and spread incredibly fast, through infected emails and files. Nimda caused hundreds of millions of dollars’ worth of disruption by combining worm, trojan and virus capabilities.
Conficker
Conficker is a blended threat that spreads fast. It was first discovered in November 2008 and propagated widely, combining various malware techniques to create a botnet, with infections in more than 190 countries to date. Conficker infects Windows OS devices and is also known as Downup and Downadup. Twelve years later, an article in Forbes discussed Conficker as “the nuisance worm” that “refuses to die”.
Partner with SEON to reduce fraud rates in your business with real time data enrichment, unique insights, machine learning and advanced APIs.
Ask an Expert
How to Protect Against Blended Threats
Protecting against blended threats means implementing robust IT security processes, following best practice, and deploying appropriate tools and software.
Firewalls, antivirus products, all the latest patches and updates… These are all key to ensuring that systems are as safe as they can be.
Educating users is another important element of protection against blended threats. Users who are on the lookout for phishing attempts and who understand the dangers of opening suspicious emails or downloading suspicious files can help to keep networks safe through their everyday actions.
The global nature of cybercrime, as we saw in our Global Cybercrime Report, and of the digital world as a whole, means that teams have to counter threats from a huge range of sources.
Compared to individual malware, blended threats are particularly hard to protect against due to their complex nature. They are becoming increasingly sophisticated as time passes, keeping IT security teams hard at work to ensure their systems are protected.