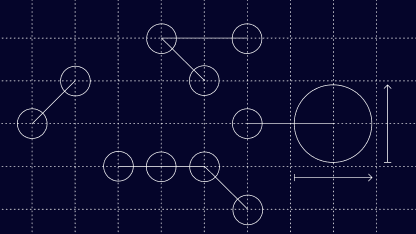
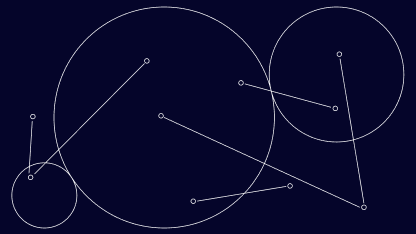
Short for graph neural network, a GNN is a system of machine learning software that analyzes data that is presented to it in the form of a graph. GNNs use deep learning to reach conclusions based on two chief parts of the input graphs: their nodes and their edges.
The nodes, which are the vertices on the graph represent input data points, and the edges – the lines between nodes – represent the connection between data points.
By analyzing nodes and edges, graph neural networks can interpret data that is presented to it as a graph, such as the diagram above, and then carry out problem-solving and predictions using the interpretation.
Such decision-making can apply to many industry sectors and online systems. For example, by spotting patterns between edges and nodes that, for instance, represent connections between apparently disparate addresses, GNNs can not only generate predictions but also find anomalies in those points of data. This helps to spot suspicious online activity, or other vital outliers in datasets.
A graph neural network is a kind of data structure, namely a specific approach to processing, storing, and interpreting data. GNNs are unique data structures in that they reflect a specific definition of the word “graph”.
Unlike a typical graph with an x-axis and y-axis, the computer science-specific context of GNNs refers to a graph that is a representation of the data in a given data structure, formed of nodes and edges.
How Powerful Are Graph Neural Networks?
Graph neural networks are very powerful tools because they form accurate models of their inputted data and achieve representation learning with efficiency. Representation learning is the phenomenon whereby a software system automatically discovers patterns in its inputted data.
GNNs achieve representation learning due to their unique capacity to find multiple data connections and/or anomalies – the node-and-vertex organization derives unique insights. As a result, they inform humans’ abilities to achieve real-world problem-solving and decision-making.
GNNs are also powerful in the sense that they are largely (but not wholly) self-sufficient: as we’ll see below, graph neural networks can determine their points of data without as much assistance from humans as other machine learning systems may require.
How Do GNNs Work?
GNNs are machine learning (ML) systems that work by using graphs as their input and then extracting data and forming conclusions based on them.
Such an approach to making calculations and predictions reflects a principle known as graph theory. Graph theory proposes that various phenomena such as systems and networks can be contextualized into graphs.
GNNs utilize graph theory by establishing one or more connections, and these connections may be directed or undirected.
This is why we have directed graphs and undirected graphs in GNNs. Using social media as the example application, let’s now look at how directed graphs and undirected graphs work in GNNs.
Directed Graphs
It’s first worth noting that an online social network is just one of the many real-world applications that relate to graph theory, but it is also one of the most relatable, so we’ll consider online connections in the next examples.
Let’s say that, on a social media platform, there are three people called Person A, Person B, and Person C.
If A searches the given social media site for B and C’s profile, but B and C have searched for neither each other’s profiles nor the profile of Person A, then this dynamic could be represented as follows:
This is a directed graph. Naturally, there are many ways in which this simple dynamic could be visualized. “Directed graph” just means that the graph reflects a one-way relationship that a node has to one or more other nodes.
Undirected Graphs
Let’s now consider the example of an undirected graph and how this would relate to a slightly different scenario on social media.
If Person A and Person B both search for each other’s online profile, and Person A and Person C also search for each other’s profiles, then there is a two-way relationship between both the former and the latter pair.
In such a situation, there would be no arrowheads in the graph because the lines are bidirectional.
When a dynamic such as the above arises on social media, Person B and Person C’s mutual connection to Person A may lead to the website suggesting to the former two users that they may know each other.
This connection is known as a triadic closure, meaning that a triangular set of data points may be closed if a three-way connection can be made.
A triadic closure can be applied to the above scenario: Given that A and B are connected, and A is also connected to C, then it stands to reason that B may also be connected to C.
This would effectively “close the triangle”. As a result, a GNN that were to process this scenario on social media could conclude (just as a human may conclude) that a three-way connection may apply between the three profiles.
In short, graph neural networks are designed to apply graph theory when organizing a dataset, working by both analyzing and forming data structures to help determine both directed and undirected connections between nodes and edges.
5 Applications of Graph Neural Networks
The below subsections will cover five applications of graph neural networks. And they are just five key examples of potentially limitless applications.
Users, their transactions, and their accounts can form a trail of data that may be effectively analyzed by graph neural networks.
1. Fraud Prevention
New accounts that may be connected to a history of malicious activity can be flagged by GNN analysis, essentially marking those accounts as “guilty by association”. Potentially, singular aspects of a device or browser fingerprint could be used to identify potentially suspicious users. Two apparently disparate users have the same unique browser settings, and they are both shipping to the same place? This could potentially be enough to close the triangle in a meaningful, actionable way.
In this way, GNNs can be used to form predictions of what activity that malicious entity may carry out in the future. Such a system is known as link analysis, and will be covered later.
2. Online Safety
As covered previously, graph neural networks are vital to enhancing online safety in social media.
The fact that GNNs can apply graph theory to online networks allows humans to better understand key dynamics of users’ web activity. This approach to cybersecurity is known as social media analysis.
3. Medicine
Graph neural networks can analyze patient data, such as their age and gender, and find trends that correspond to those factors.
This allows medical professionals to identify trends in their diagnoses and treatments that are specific to various patient demographics.
4. Computer Vision
Computer vision is a system of artificial intelligence that allows computers to scan images, categorize them, and form conclusions based on their resultant image classification.
GNNs can enhance the capabilities of computer vision systems by identifying both the patterns and anomalies present in various images and forming conclusions as a result.
One area where this is especially important is in cancer screenings, where x-rays may be analyzed for signs of abnormal tissue in patients.
5. Geolocation
GNNs are able to improve the capacity for geolocation software, which includes such navigation applications as Google Maps, to inform drivers of their ETA.
This is down to the fact that graph neural networks can process multiple nodes (in this case, such factors as traffic conditions, speed limits, and weather conditions) and cross-check those factors to reach an accurate journey time.
How Can GNNs Fight Fraud?
Graph neural networks are equipped to fight fraud because they can analyze multiple nodes, and by forming connections between those nodes, they are able to determine whether suspicious online activity may apply.
By utilizing graph theory, GNNs can help to flag whether an online user is likely to be any one or more of the following: associated with malicious activity, guilty of malicious activity, or likely to commit suspicious activity in the future.
Respectively, risk-associated flags like these can be achieved by one or more of the following GNN functions.
Social Network Analysis
The aforementioned social network analysis function of GNNs means that, not only can suspicious accounts be flagged, but accounts that are associated with suspicious users may also be detected.
For instance, if a fraudster sets up a new social media profile and carries out similar web activity to their old account, that profile may be flagged as being “guilty by association” with the original, malicious account.
Link Analysis
The aforementioned system known as link analysis enables another process by which fraudulent activity may be detected.
Link analysis in GNNs allows suspicious activity to be flagged, particularly in terms of online transactions. As one example, a graph neural network could detect when the same bank card is being used frequently – and suddenly – on the same ecommerce site.
This would form an unusual pattern that a graph neural network could flag as potentially fraudulent. And it would then be the job of human operators to consider the possibility that a user’s account may have been hacked, or their card details were misused.
Automated security and learning processes like graph neural networks are a vital part of fraud prevention. Their existence inside a security stack means that a great deal of risk analysis can be handed over to cost-saving, friction-lowing solutions that aim a GNN-powered eye at incoming traffic.
Though every ecommerce company will have a need for human oversight when it comes to making borderline review calls and adjusting software to fit respective risk appetites, GNNs help lighten manual workloads while also presenting more intense mathematical scrutiny than humans are capable of performing, particularly at scale.