Fraud Prevention Solution
Fraud Prevention Built for Speed, Precision and Scale
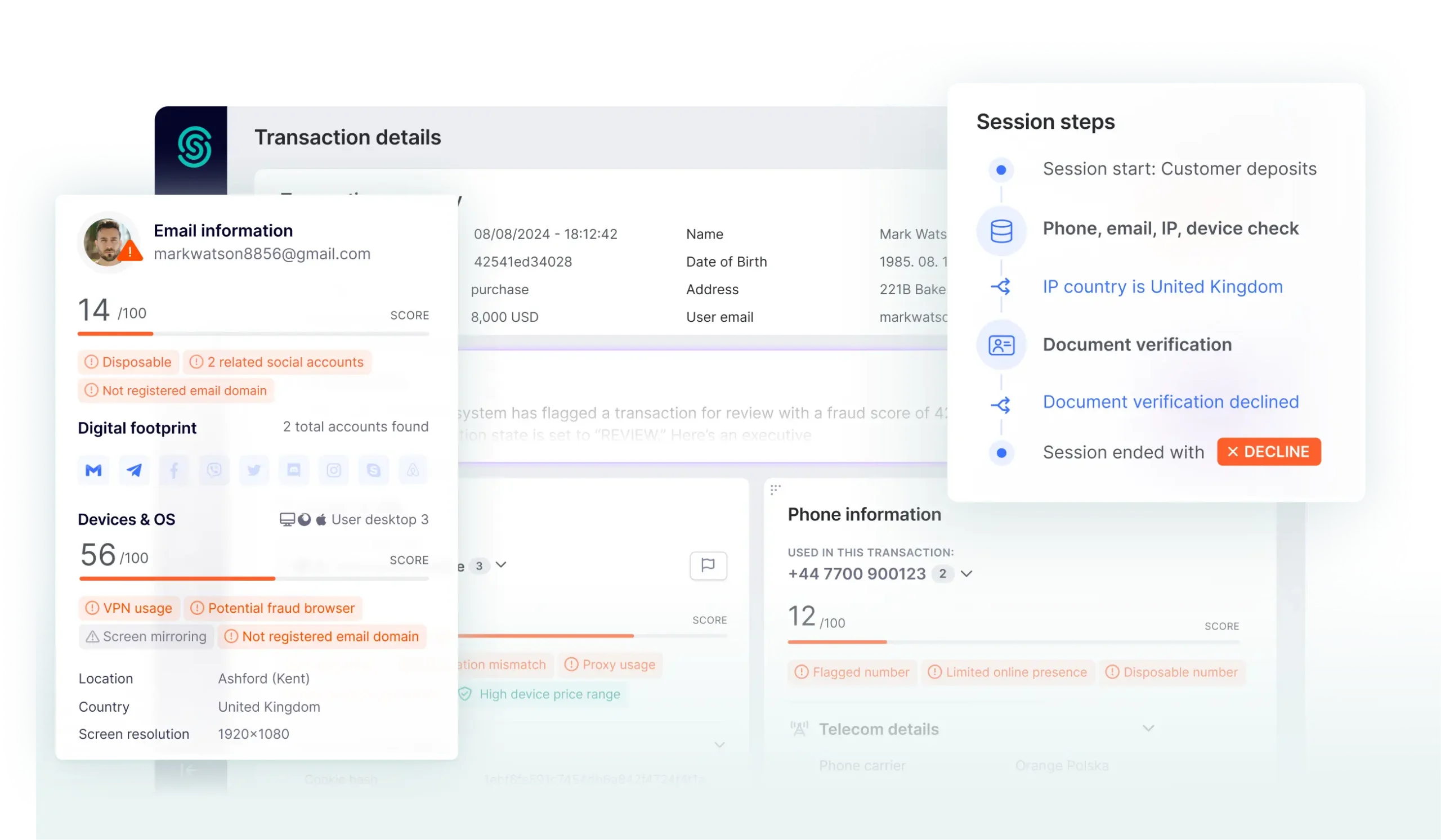
SEON’s fraud prevention solution connects 900+ first-party signals across digital footprint, device intelligence and behavioral data to automate real-time fraud decisions across the customer journey.
Trusted by the World’s Most Ambitious Companies
Fraud Prevention with SEON
Unified Fraud Prevention System
Pre-Screen Bad Actors Before KYC

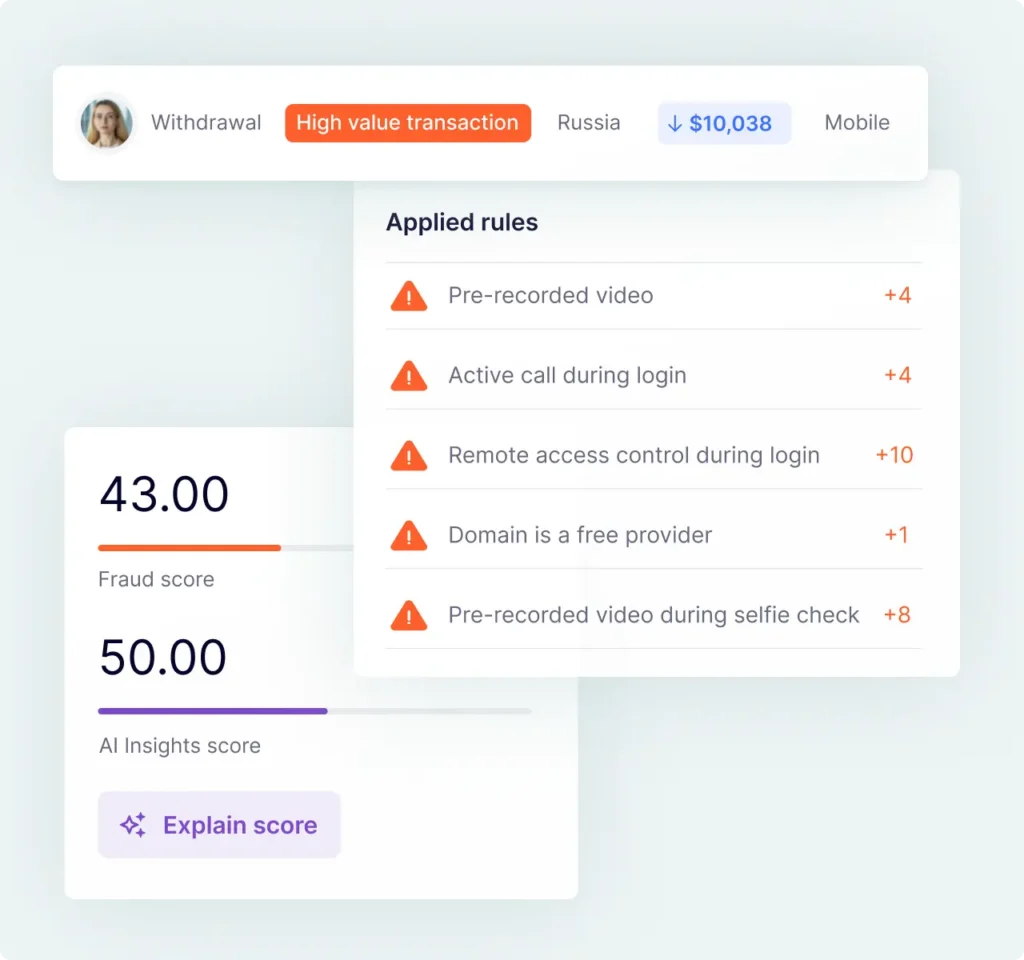
Detect Payment Fraud & Account Takeovers in Real-Time
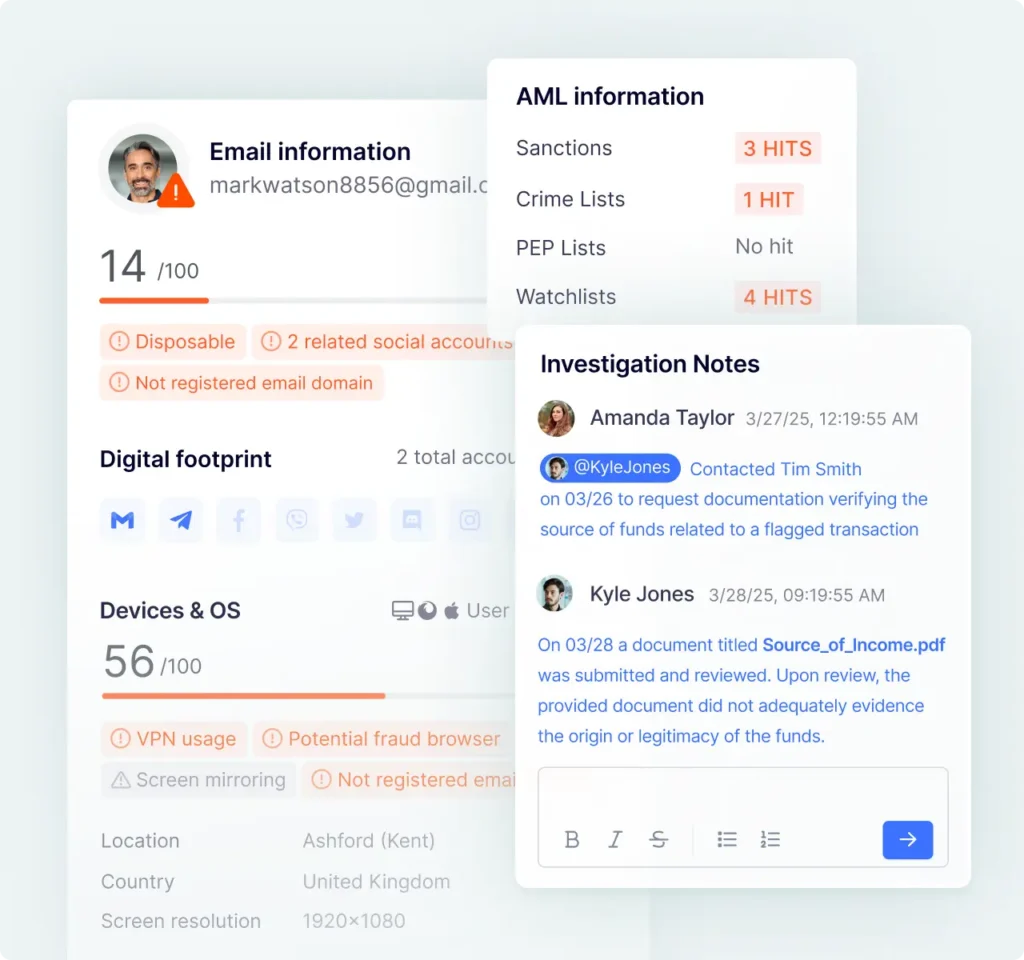
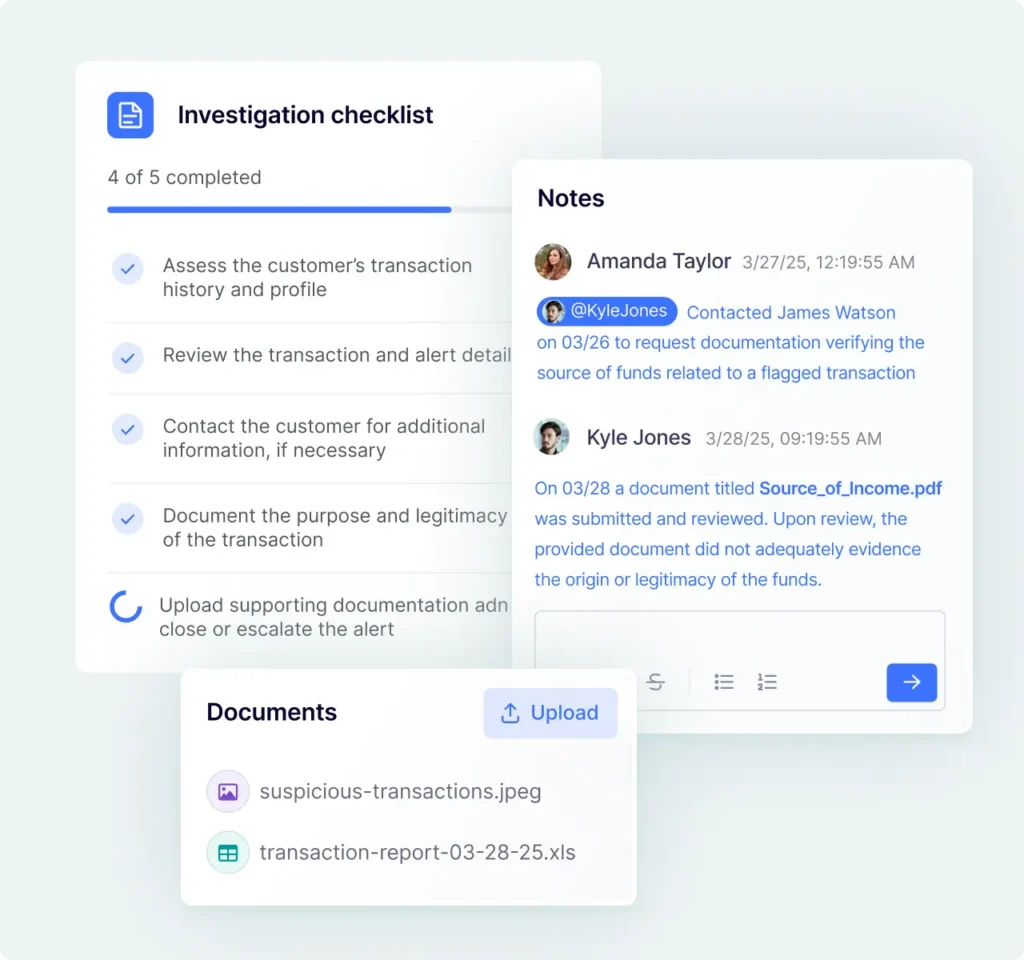
Investigate Cases Faster With Complete Customer Context
Unified Compliance and Fraud Prevention Solution
Fraud Prevention Across Different Risk Scenarios
Bonus Abuse
Real-time screening detects repeated or coordinated bonus misuse to protect revenue.
Fake & Synthetic IDs
Digital footprint analysis uncovers fake or synthetic identities before registration.
Account Takeover
Device and behavioral monitoring highlights unusual logins to block unauthorized access.
Payment Fraud
Adaptive scoring detects high-risk payments without blocking genuine users.
Registration & Onboarding
Data-driven checks identify fake users early, protecting growth and customer experience.
Login & Activity Monitoring
Social engineering attacks happen, but you can keep customer accounts safe.
Transaction Monitoring
AI-driven analysis detects fraud and risk in real time across millions of transactions.
Chargeback Fraud
Automated workflows manage chargebacks efficiently, reducing effort and recovering more revenue.
Deploy in Days, Not Months
Middleware orchestration tools take months to onboard. On average, teams go live with SEON in around 14 days. Go live quickly with a single API, ready-to-use rules and hands-on support.
in-house fraud prevention expertise
How Leading Teams Prevent Fraud at Scale
Learn More About Fraud Prevention
-
Get our free guide to reduce chargebacks, prevent fraud, and protect your revenue.
-
Discover tools to detect and prevent payment fraud. Protect your business and secure transactions effectively.
-
Explore AI-driven fraud detection, key fraud types, and strategies to choose the right system for real-time protection.
-
Learn how payment gateway fraud works and compare detection tools to stop BIN attacks, fake transactions, and account takeovers.
-
APP fraud is rising, driven by real-time payments. Businesses must use AI, ML, and digital intelligence to prevent scams.
-
Download our iGaming fraud guide to stop threats early, stay compliant, and protect revenue.
Fraud Prevention FAQs
A fraud prevention solution is a unified technology solution that detects, prevents, and manages fraudulent activity across digital channels. It combines data from multiple sources, including device intelligence, digital footprint analysis, and behavioral signals, to identify suspicious activity in real time and enable businesses to block fraud before it causes financial loss and downstream operational costs.
SEON detects fraud across the customer journey including synthetic identity fraud, bot attacks, promo and bonus abuse, multi-accounting, account takeover, payment fraud and chargebacks. The platform adapts to new patterns through configurable rules and AI models.
SEON’s API responses return in milliseconds, enabling real-time decisioning at registration, login, event and transaction monitoring without impacting user experience. High-volume environments can process thousands of transactions per second.
The solution also offers AML screening, payment screening, transaction monitoring and case management alongside fraud prevention, bring a wealth of unique signals together in one system to support coordinated fraud and compliance workflows.
Protect Every Interaction With a Unified Fraud Prevention Solution
Book time with fraud specialists who understand your industry and map your clear path forward.
Trusted by 5,000+ global organizations:
Speak With a Risk Expert
This form may not be visible due to adblockers, or JavaScript not being enabled.