
The Benefits of Phone Risk Assessment for Your Business
June 11, 2020 by Tamas Kadar
You might have heard of email analysis, but did you know phone risk assessment is increasingly popular to combat fraud?
If you’ve had to sign up to a new online service lately, chances are you’ve had to enter your phone number along with an email address and name.
This wasn’t always the case. But the growing popularity of mobile-first design and social messaging apps like Whatsapp, Viber or Facebook messenger means it’s increasingly common to request this additional customer data point.
But these phone numbers aren’t just useful for providing two-factor authentication (2FA). As we’ll see, a phone number is now an important part of a user’s digital footprint, which is exactly why phone risk assessment can help reduce fraud in your company.
How Often Do You Change Your Phone Number?
If it’s a landline, probably once every five to ten years. Even mobile phone numbers have surprising longevity, as mobile operators understood it was in their interest to help users keep their numbers when switching.
This is precisely why phone numbers are a great tool for authentication, for the average user at least. Every time the number is used to register with a social messaging service, it stays associated with the same person.
The only problem is that fraudsters do know how to change their numbers often – when they don’t steal other people’s.
The Ways Fraudsters Acquire Phone Numbers
So how do fraudsters bypass 2FA and registration with phone numbers? While historically phone numbers were harder to create and to find on data breaches (acquired on darknet marketplaces) there is now no shortage of options as they can use:
- SIM hijacking: fraudsters ask mobile carriers to switch a phone number to another SIM card under their control. They then access all online accounts tied to the phone number as well as incoming SMS messages.
- Advanced phone hijacking: more sophisticated methods will see fraudsters posing as fake WiFi public hotspots or even cell towers to intercept mobile data.
- Phishing and social engineering: fraudsters are often versed in the techniques designed to steal people’s real information, such as email links redirecting to keylogging websites, for instance….
Creating Virtual Phone Numbers
It’s now also surprisingly easy for anyone to create a disposable or temporary phone number using a burner phone, much like a disposable email address.
A burner phone is a term originating from the drug-dealing world, when inexpensive mobile phones were used temporarily and discarded. These days, phone numbers are generated virtually with burner phone apps or services, such as Hushed or Burner App.
The burner apps register their own names with the provider instead of the user’s. The numbers are typically unlisted, and recycled regularly between numerous users.
The good news for fraud fighters, however, is that the numbers must go through the phone’s original cellular data, which means they are not untraceable.
Finally, the less sophisticated fraudsters will simply enter an invalid phone number just to register to a service.
What Phone Risk Assessment Can Tell You
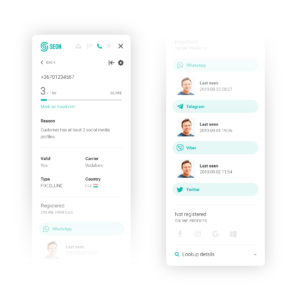
So we now see that phone numbers aren’t a bulletproof verification method, and that they can be a strong indicator of risk. But what are we looking for exactly to tell us? Here is what phone risk assessment looks like:

There is then a lot of extremely valuable data associated with social media accounts:
- Connected accounts: see if the phone number is linked to someone’s Facebook, Google, Instagram or Twitter account – which will give you a username. Ideally, it should match other details used for registration.
- Messenger data: when the phone number is linked to messenger apps (Whatsapp, Viber, Telegram) we can also retrieve the profile picture and information about when the user was last seen online. Incredibly useful to confirm user identity and activity.
Monitoring the Right Stage in the Customer Journey
So how do you get started with phone risk assessment? First of all, we recommend you focus on your users’ registration stage as it’s the best place to catch fraudsters before they can wreak havoc with your business (for chargebacks, bonus abuse, multi-accounting fraud, etc…)
But you can also check phone numbers later, for transactions, logins or other user actions. As to how you can integrate SEON’s phone risk assessment tools, you have multiple options there:
- Manual review: our innovative phone API lets you check phone numbers directly with near instant results.
- API integration: our phone API gives you the same granular results at scale, and without adding friction for users. Getting the raw data is particularly useful if you already have a fraud prevention tool and need to boost its precision with extra information.
- Full end-to-end platform: SEON Sense is the modular, end-to-end fraud detection solution that gives you complete control over the rules and risk scores. Phone data is analyzed along with IP, email and device information to give you a full picture of who your users are.
How Legal is Phone Risk Assessment?
It’s completely legal, as long as the data is found on open source databases. At SEON, our phone analysis tool is fully GDPR compliant, and designed to let your business meet all data protection regulations.
We are also ISO27001-certified, so you can be certain your customer data is in safe hands with us.
Ready to Protect Your Business With the Right Tools?
Getting started with phone risk assessment is only a few clicks away. If your business is seeing an increase in fraudulent transactions, chargebacks or other forms of attacks, we’re confident phone screening will help.
This is particularly true if you combine it with any of our other fraud modules, such as Email analysis, IP analysis and Device Fingerprinting — all designed to work independently or together to give you full control over how to grow your business safely.
You might also be interested in reading about:
Speak with a fraud fighter.
Click here
Tamas Kadar
Tamás Kádár is the Chief Executive Officer and co-founder of SEON. His mission to create a fraud-free world began after he founded the CEE’s first crypto exchange in 2017 and found it under constant attack. The solution he built now reduces fraud for 5,000+ companies worldwide, including global leaders such as KLM, Avis, and Patreon. In his spare time, he’s devouring data visualizations and injuring himself while doing basic DIY around his London pad.
SEON Resources
Sign up for our newsletter
The top stories of the month delivered straight to your inbox